Category: Vulnhub
-
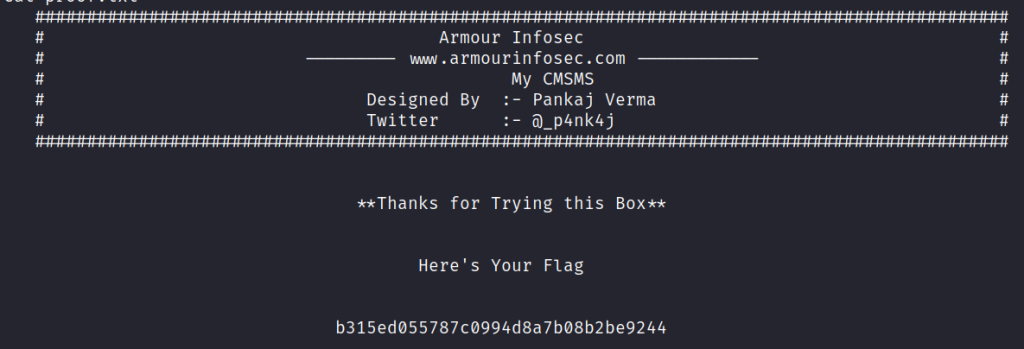
My CMSMS: 1
This VM has been designed by Pankaj Verma. Like its name, this box contains some interesting things about CMS. It has been designed in way to enhance user’s skills while playing with some privileges. Its a quite forward box but stay aware of rabbit holes.
-
So Simple : 1
This is an easy level VM with some rabbitholes. Enumeration is key to find your way in. There are three flags (2 user and 1 root flag).
-
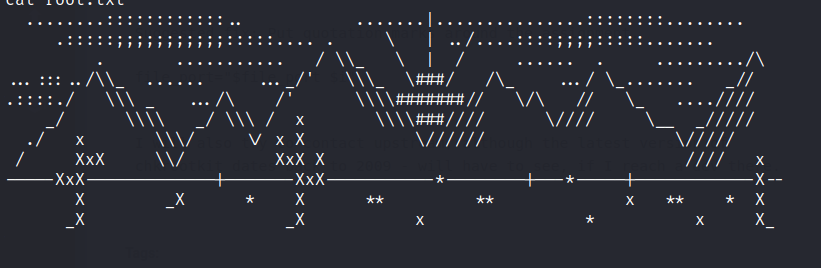
RickdiculouslyEasy :1
https://www.vulnhub.com/entry/rickdiculouslyeasy-1,207/ Review Enumeration Run nmap scan to find for open ports. FTP Server Able to access it annoymously. Found a flag. Port 9090 Unable to do much with he website as there is no login or password input. Port 13337 Port 60000 Netcat into the port to find a flag Port 80 Run a gobuster…
-
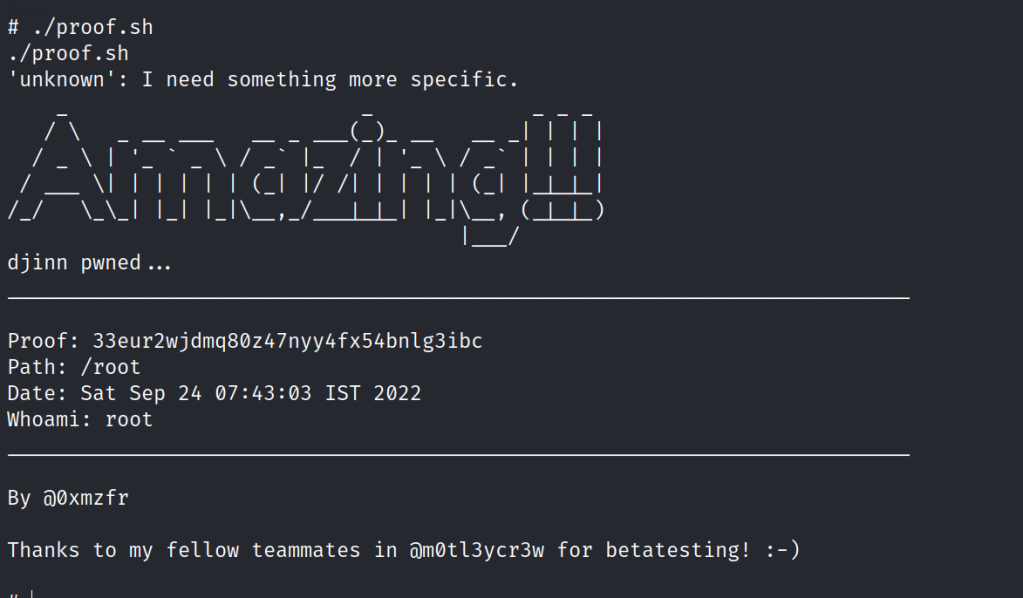
Djinn : 1
https://www.vulnhub.com/entry/djinn-1,397/ Review Enumeration Run nmap scan to find for open ports. FTP Enumeration Let’s try connecting to the game server. Let’s use netcat to connect. Port 7331 Http Run a gobuster scan to find for hidden directories. /genie is just an error page /wish We are able to input cmd and view the info in…
-
BBS (cute): 1.0.2
https://www.vulnhub.com/entry/bbs-cute-102,567/ Review Enumeration Run nmap scan to find for open ports. Port 80 Port 88 Run a gobuster scan to find for hidden directories. index.php We find CuteNews interface. Let’s register a new user , for the Captcha code we can use /captcha.php to find one. In the profile section of the interface we are…
-
Photographer : 1
This machine was developed to prepare for OSCP. It is boot2root, tested on VirtualBox (but works on VMWare) and has two flags: user.txt and proof.txt.
-
Cybersploit : 1
https://www.vulnhub.com/entry/cybersploit-1,506/ Review Enumeration Run nmap scan to find for open ports. Port 80 Found a username in the sourcecode. Run a gobuster scan to find for hidden directories. /robots.txt Use base64 to decrypt the code and the first flag is found. Foothold Let’s try to ssh into the itsskv user with the flag password. Found…
-
DriftingBlues:6
https://www.vulnhub.com/entry/driftingblues-6,672/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. /robots.txt , /robots /textpattern/textpattern /spammer gives us a zip file Let’s crack the password for the zip protected file. Found the credentionals. Foothold Login via text pattern From textpattern interface we are able…
-
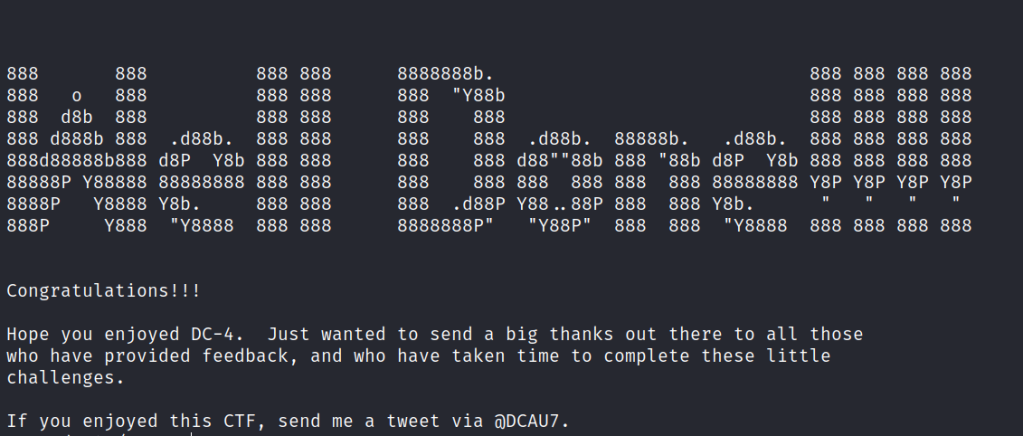
DC: 1
https://www.vulnhub.com/entry/dc-1,292/ Review Enumeration Run nmap scan to find for open ports. port 80 Run a gobuster scan to find for hidden directories. robots.txt gives us a long list. After some time exploring the robots.txt folders , I am unable to find anymore clues. From the Nmap scan we know that Drupal is running version 7.…
-
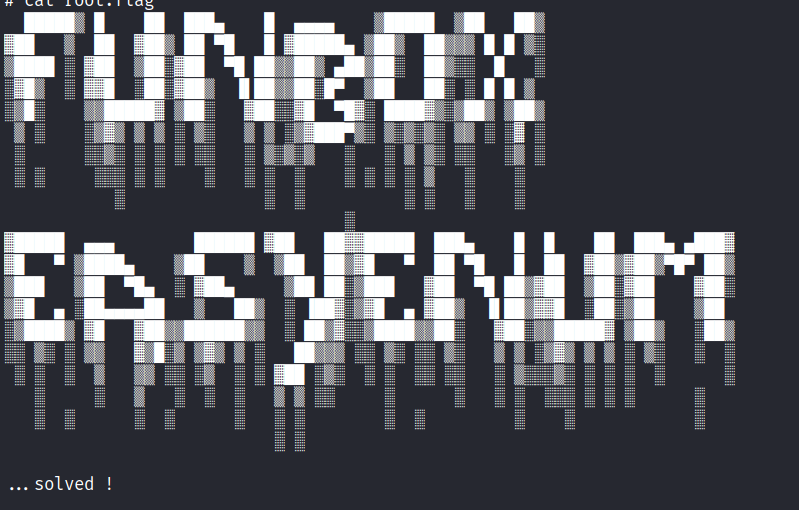
Funbox : EasyEnum
https://www.vulnhub.com/entry/funbox-easyenum,565/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. robots.txt secret/ mini.php/ In this mini shell we are able to upload files. Let’s upload a php reverse shell and execute it. Foothold Access gained. In the home directory there are the following…