https://tryhackme.com/room/owasptop10
[Severity 1] Command Injection Practical
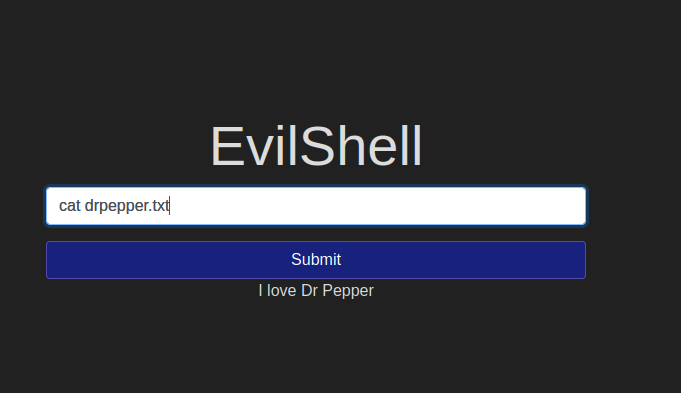
What strange text file is in the website root directory?

How many non-root/non-service/non-daemon users are there?

What user is this app running as?

What is the user’s shell set as?

What version of Ubuntu is running?

Print out the MOTD. What favorite beverage is shown?