It’s likely that you are honing your skills on beginner-friendly CTFs (Capture the Flags) if you are just getting started in information security. There may be categories in reverse engineering or binary exploits if you encounter certain intermediate to advanced level challenges. While we can first try to avoid them, eventually we must accept them. In my previous article I wrote about creating our own programs and breaking into them to learn fundamental concepts and skills. Slowly but surely.
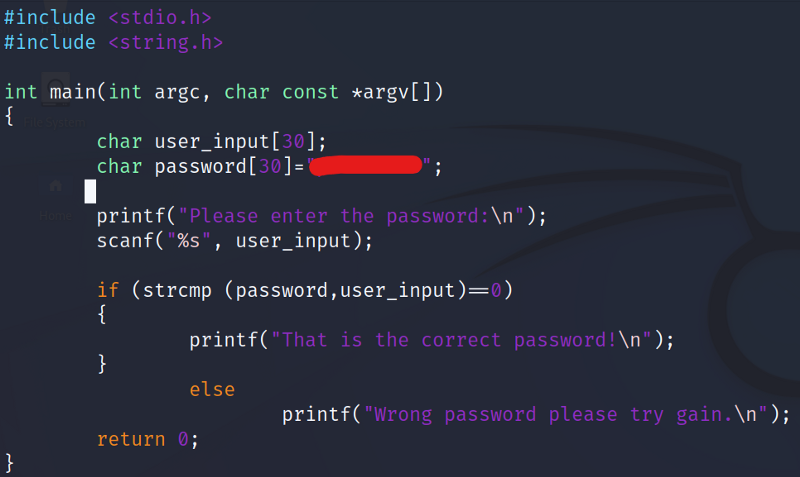
I created a simple C language password program which you can download here. Let’s use a debugger to dissect the program and see how we can bypass the password.
What is a debugger? A tool that aids in finding and fixing problems in a program. For this practice I’m going to start out with the Linux based debugger, GDB.
You can install this program in your Linux machine with the following commands:
sudo apt-get update
sudo apt-get install gdb
Assembly has two flavors AT&T and Intel. Why? I wish can explain it but I have no idea. (yet)
You can download the the practice file here.
First let’s view the source code.
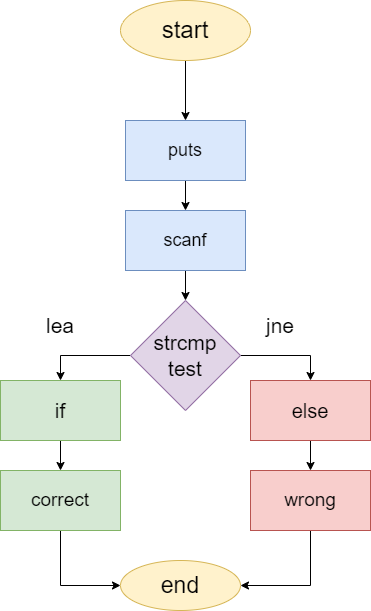
I drafted out a rudimentary flow chart to have a clearer understanding of the program.
Now we that we have a gist of how the program functions we can start up GDB. use gdb <FILE>
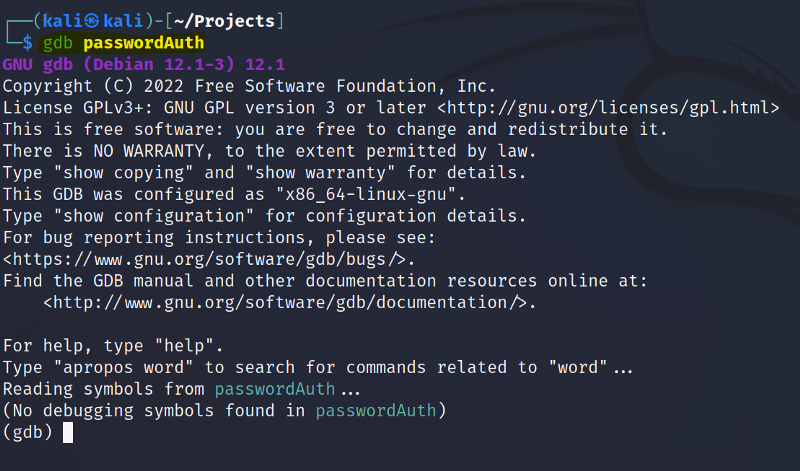
First let’s look at the functions available for us to debug. Enter info functions
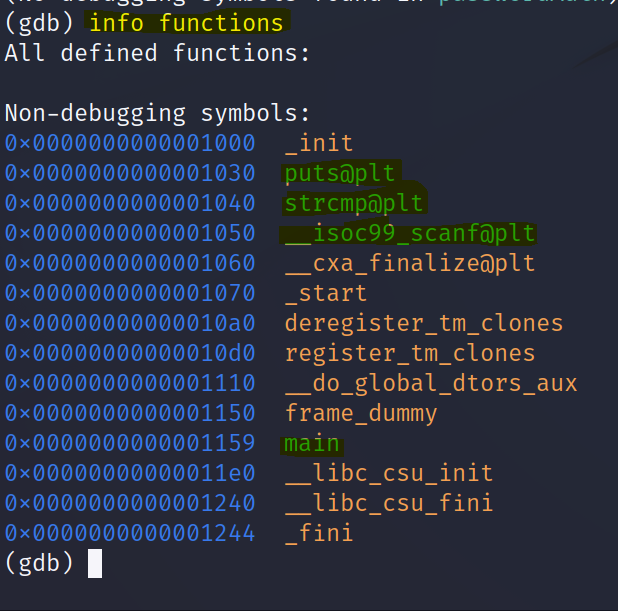
We can see some familiar inbuilt functions like puts(printf) , scanf and strcmp. For most programs we will start with the main function.
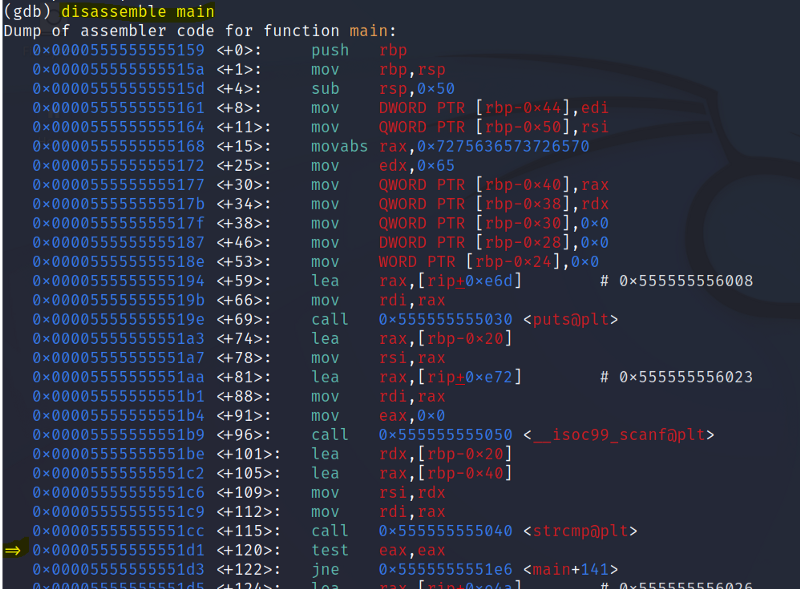
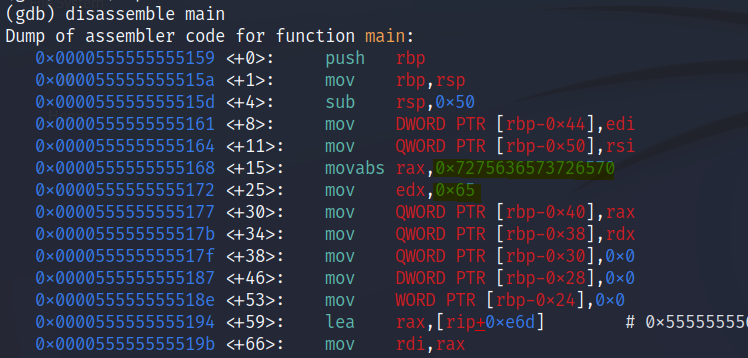
Enter disassemble main to dissect the main function into Assembly language.
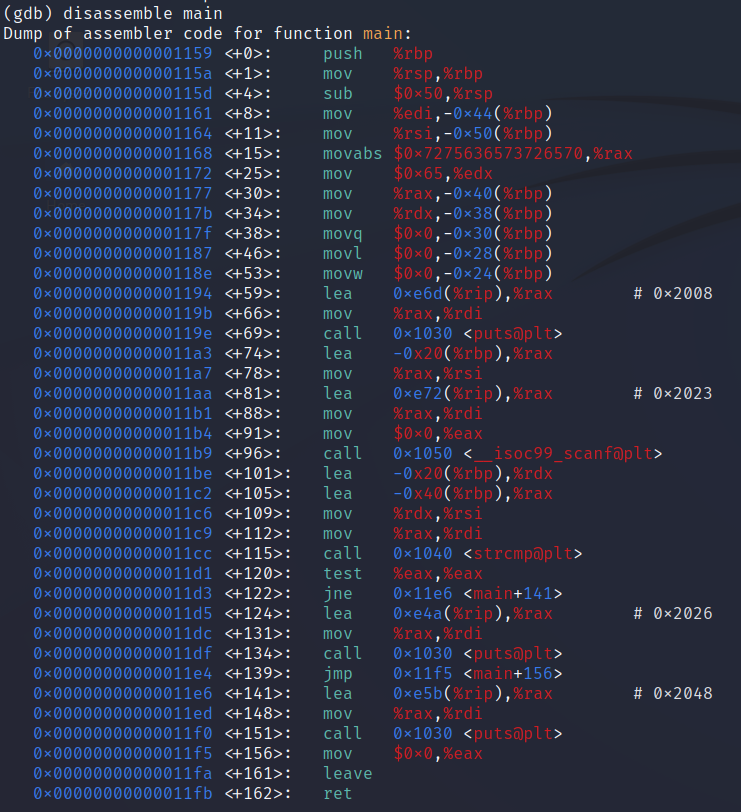
You did not make a mistake it’s suppose to look like this. By default it comes with AT&T syntax. Use set disassembly-flavor intel to change it to the intel syntax. *Most tutorials are done with Intel syntax so I’m going to use it too.
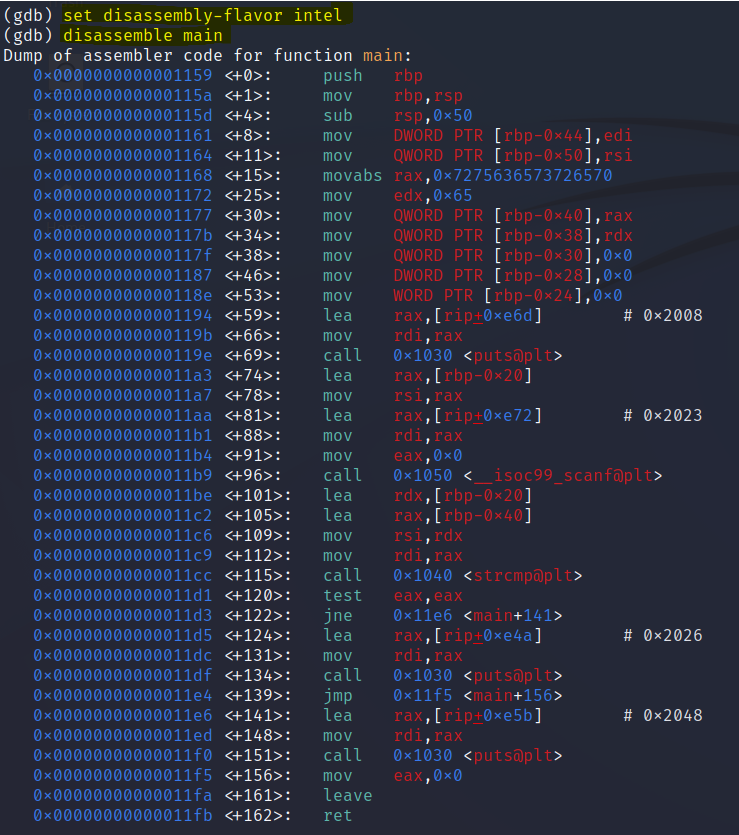
Much better I guess?
Let’s see if I can categorize the functions and explain the code.
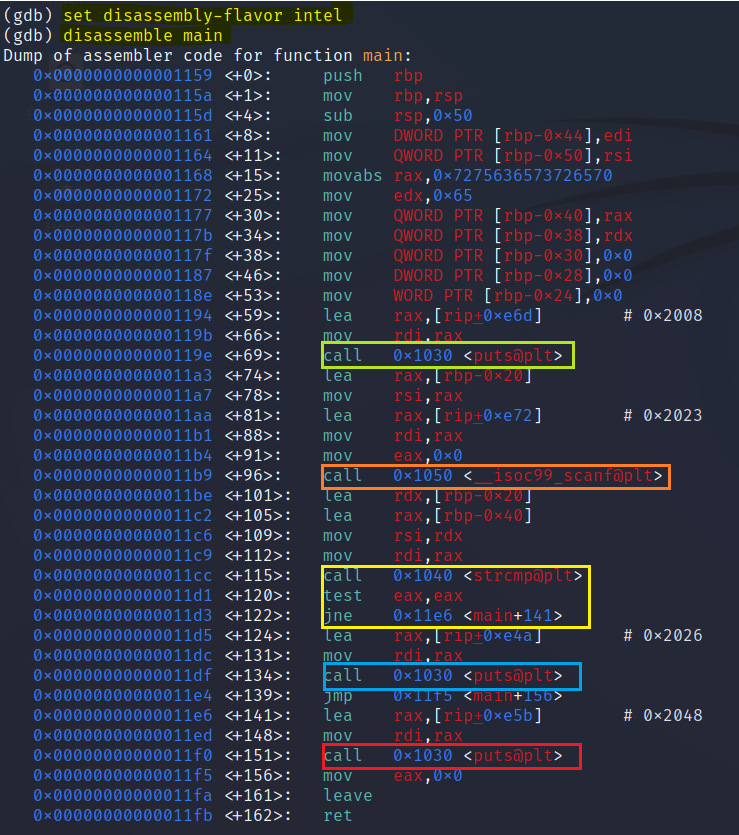
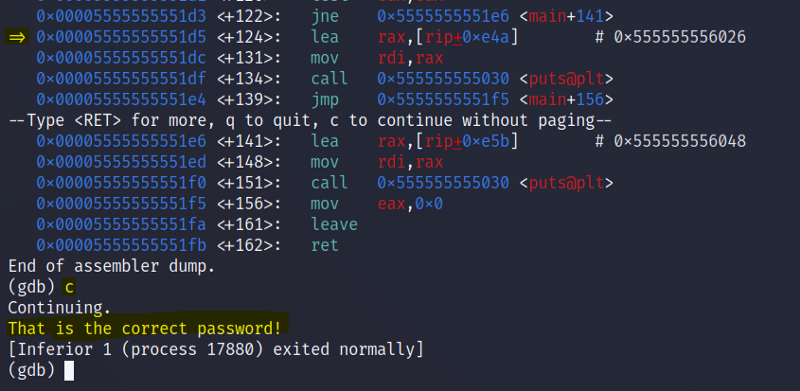
When the strcmp function is called the test instruction is invoked to compare the user input and the password. The jne flag means “jump not equal” if the test result is 0 it continues with the next instruction till it reaches the “Correct” message (blue box) if not, it will jump to the <main+141> address that leads to the “Wrong message” (red box).
One of the most crucial debugging methods in your toolkit is the use of breakpoints. Anywhere you wish to pause the debugger, you place breakpoints.
Place a breakpoint at the start of the main function with break *main and run the program with “r”.
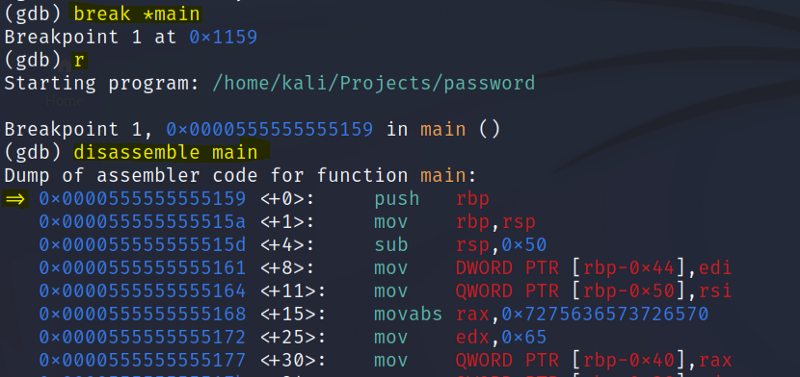
There will be an arrow pointing to where the breakpoint stops.
Add another breakpoint ofthe address of the test instruction. break *<ADDRESS> and continue the program with “c”
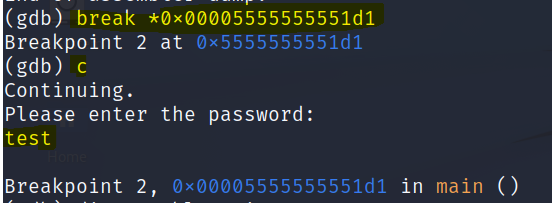
Enter a random password and the breakpoint 2 will stop at the test instruction.
We can see this with arrow pointing to the test instruction.
If the test instruction results in 0 it means that our password is correct. However we do not know the password and chances are it is a wrong one. It will result in 1. Which will activate the jne command and prints us the wrong message.
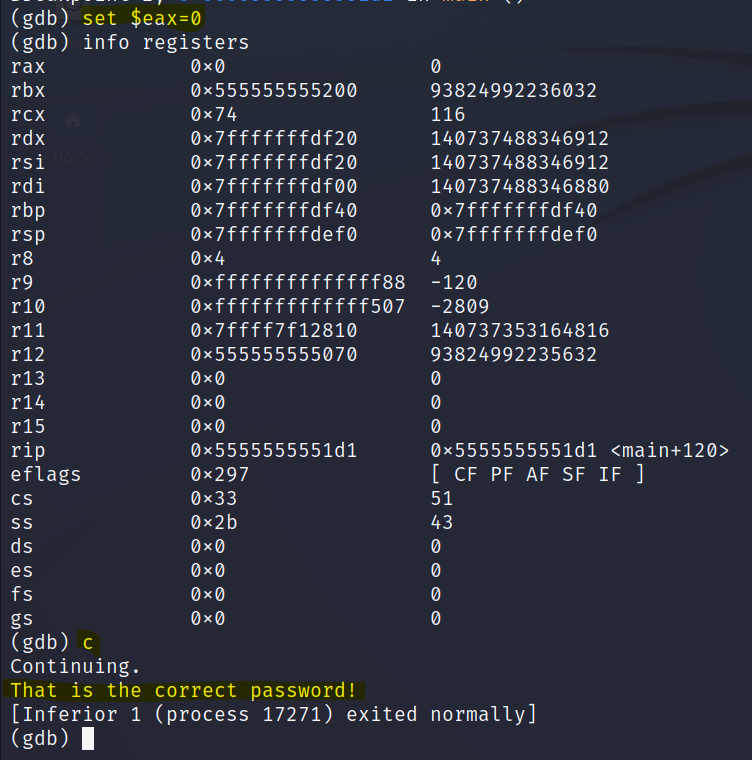
To bypass this we can change the eax value of the test instruction to 0. We can use set $eax=0

info registers is a command we can use to check the values of the registers in that current address.
Now when we continue to run our program we bypassed the jne and got the correct message.
Another method we can use is to set the instruction pointer of the program to the address after the jne instruction. This will bypass everything. Use set $rip=<ADDRESS AFTER JNE>
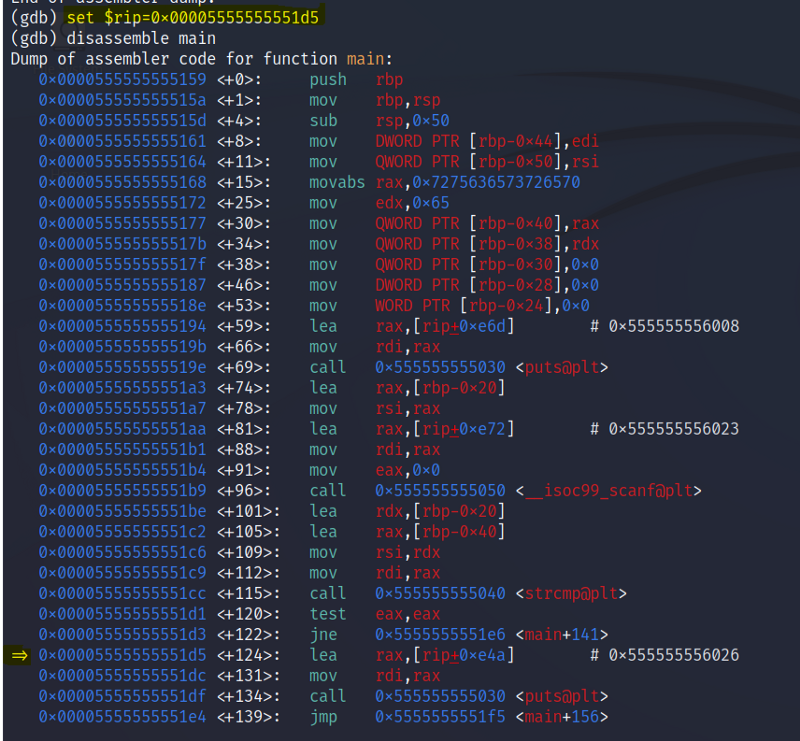
Now when we run the program we have the correct message.
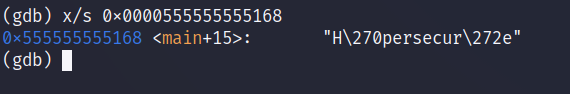
Another option to find the password in plaintext is to look for the address that has stored the password. GDB has an option to view the address in string format. From my experience in doing basic crackmes this is only possible if the password is hardcoded.
Use x/s <ADDRESS OF STORED PASSWORD> *strings might be various order*
Final thoughts
There are indeed many tools and easier methods to crack simple crackmes but I wanted to experience using a debugger like GDB. Reverse engineering is not just about crackmes , It’s an integral part of malware analysis and research, but it’s also one of the most advanced skills a researcher can possess.