After Karen started working for ‘TAAUSAI,’ she began to do some illegal activities inside the company. ‘TAAUSAI’ hired you to kick off an investigation on this case.
You acquired a disk image and found that Karen uses Linux OS on her machine. Analyze the disk image of Karen’s computer and answer the provided questions.
https://cyberdefenders.org/blueteam-ctf-challenges/64#nav-questions
Download the challenge folder and use FTK imager to view the image of the system file.
Q1
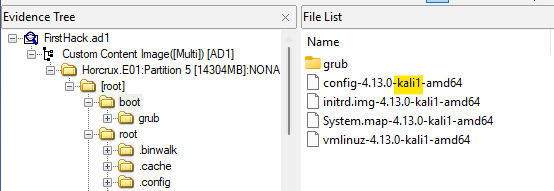
What distribution of Linux is being used on this machine?
The distribution of the Linux system can be seen in the boot folder.
Q2
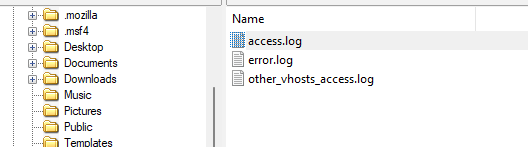
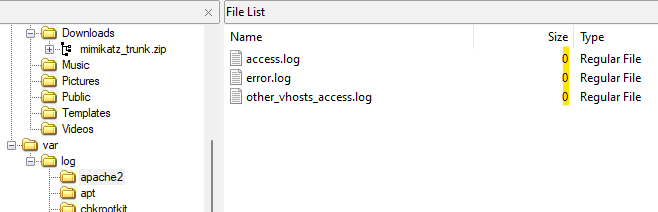
What is the MD5 hash of the apache access.log?
Locate the access.log and export the file as a hash to find the answer.
Q3
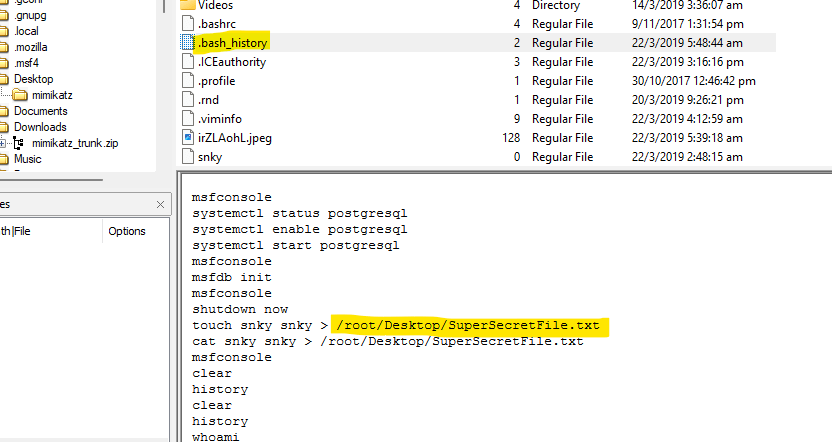
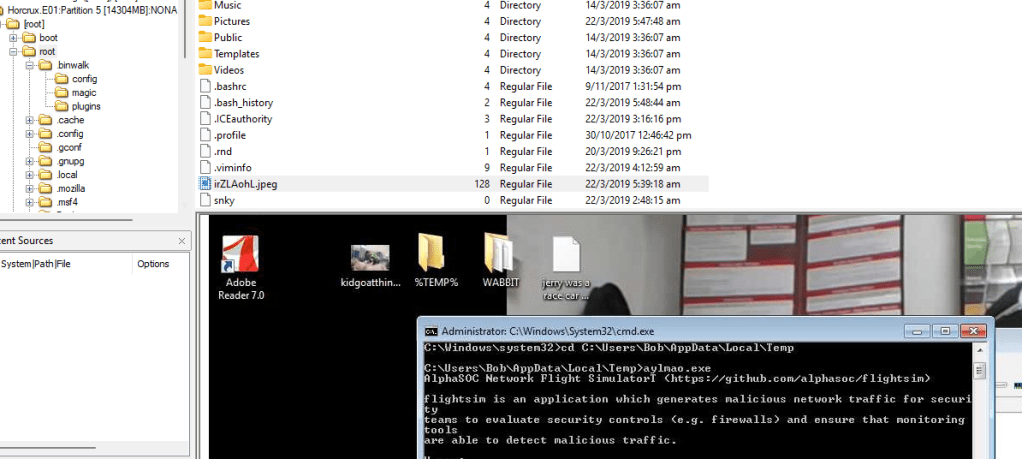
It is believed that a credential dumping tool was downloaded? What is the file name of the download?
Find the file in the downloads folder.

Q4
There was a super-secret file created. What is the absolute path?
View the bash history file to find the secret file that was createad.
Q5
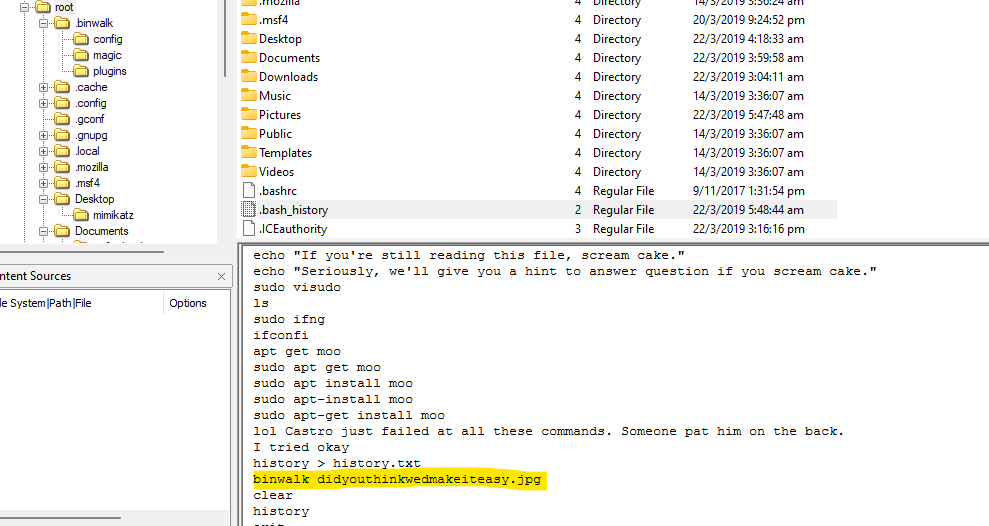
What program used didyouthinkwedmakeiteasy.jpg during execution?
Check the bash history file to find the program used to run the image.
Q6
What is the third goal from the checklist Karen created?
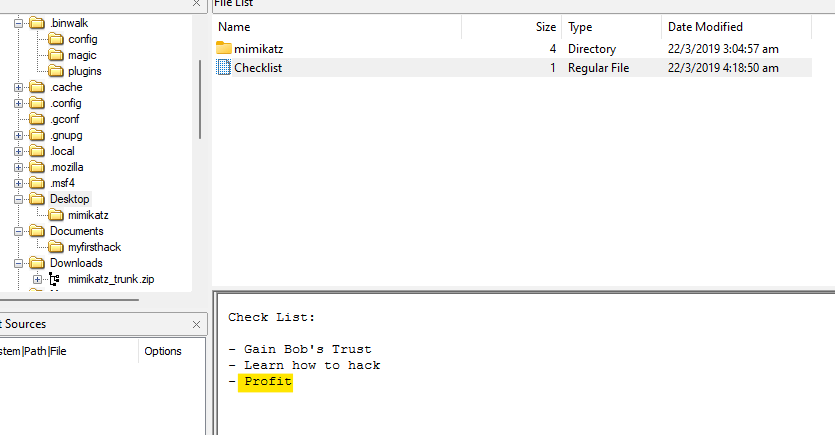
Q7
How many times was apache run?
Since all the sizes are 0.
Q8
It is believed this machine was used to attack another. What file proves this?
There is an image of a windows machine in the foot folder.
Q9
Within the Documents file path, it is believed that Karen was taunting a fellow computer expert through a bash script. Who was Karen taunting?

Q10
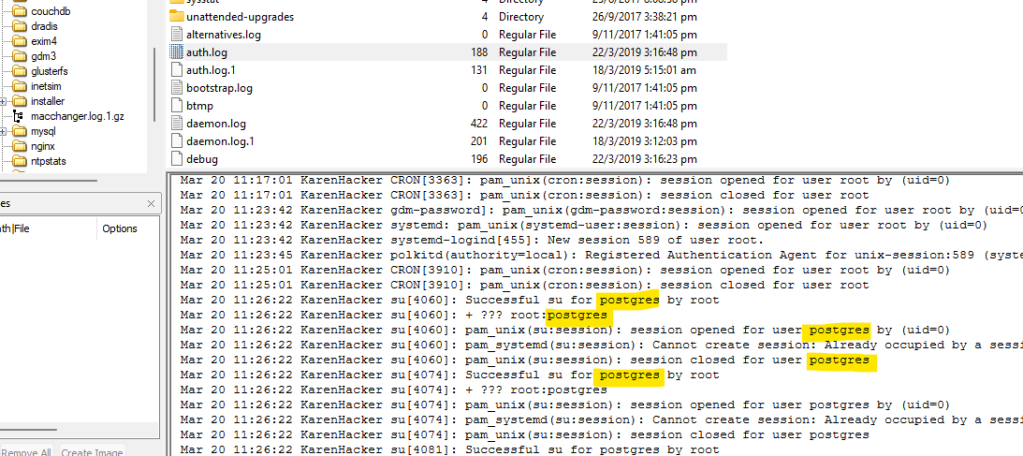
A user su’d to root at 11:26 multiple times. Who was it?
Head to the auth.log file in /var/log and search for the time.
Q11
Based on the bash history, what is the current working directory?
Check the bash history file and look out for the last “cd” command.
