Tools used:
- IDA Pro Free
Questions
1. What is the address of DllMain?


1000D02E
2. Use the Imports window to browse to gethostbyname. Where is the import located?


.idata:100163CC
3.How many functions call gethostbyname?
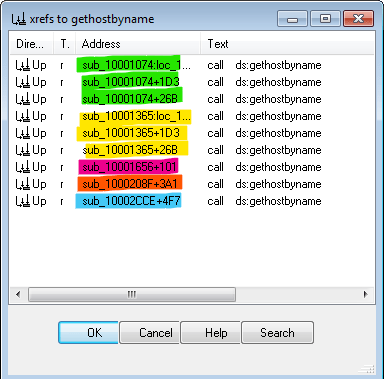
9 times with 5 different sub routines.
4. Focusing on the call to gethostbyname located at 0x10001757, can you figure out which DNS request will be made?

5.How many local variables has IDA Pro recognized for the subroutine at 0x10001656?
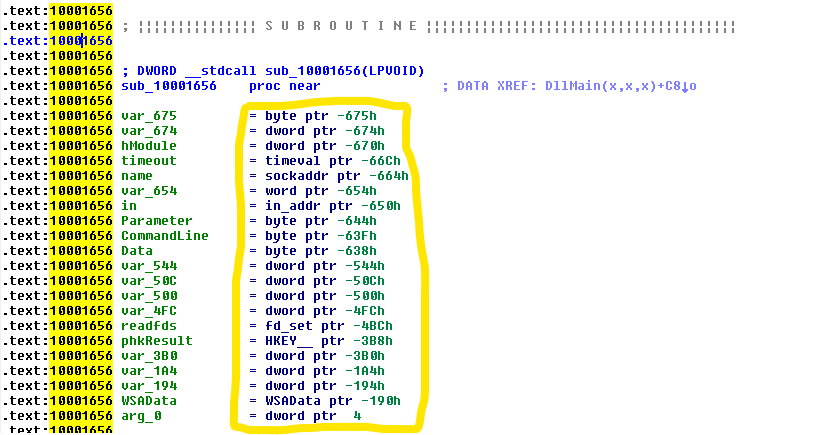
6. How many parameters has IDA Pro recognized for the subroutine at 0x10001656?

7. Use the Strings window to locate the string \cmd.exe /c in the disassembly. Where is it located?

8.What is happening in the area of code that references \cmd.exe /c?

Viewing the function in graph form we can follow the different entries.
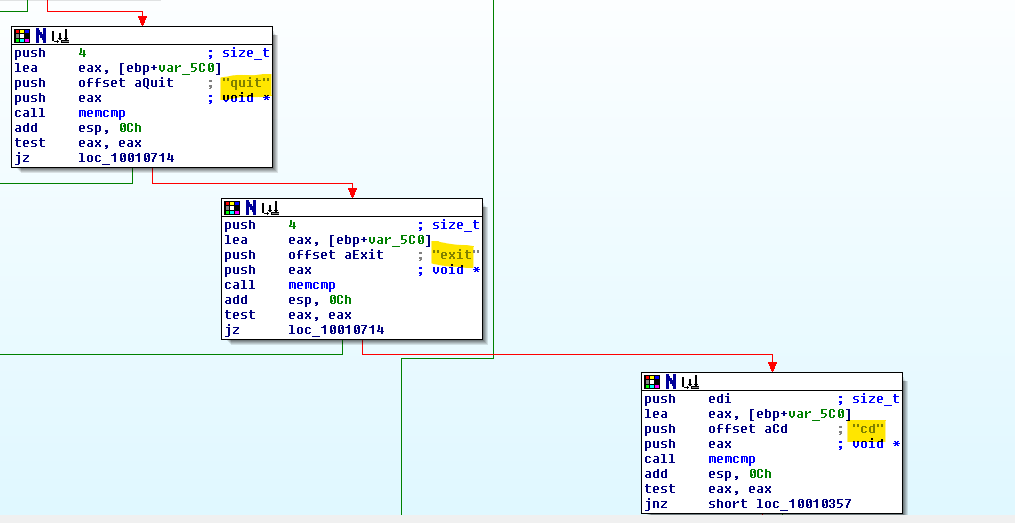

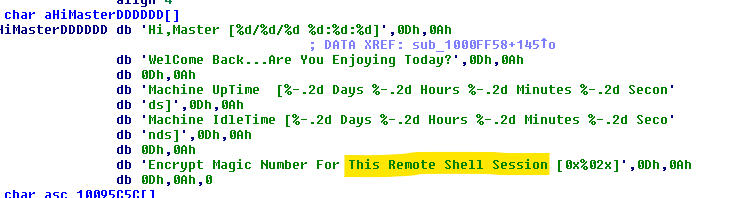
This area of code seems to be a Remote Shell Session.
9.In the same area, at 0x100101C8, it looks like dword_1008E5C4 is a global variable that helps decide which path to take. How does the malware set dword_1008E5C4? (Hint: Use dword_1008E5C4’s cross-references.)
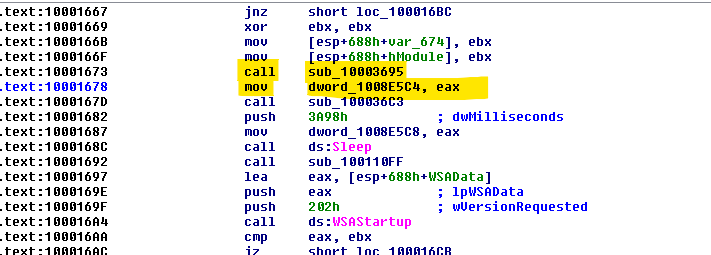


The malware will check the version of the operating system and decides on the path.
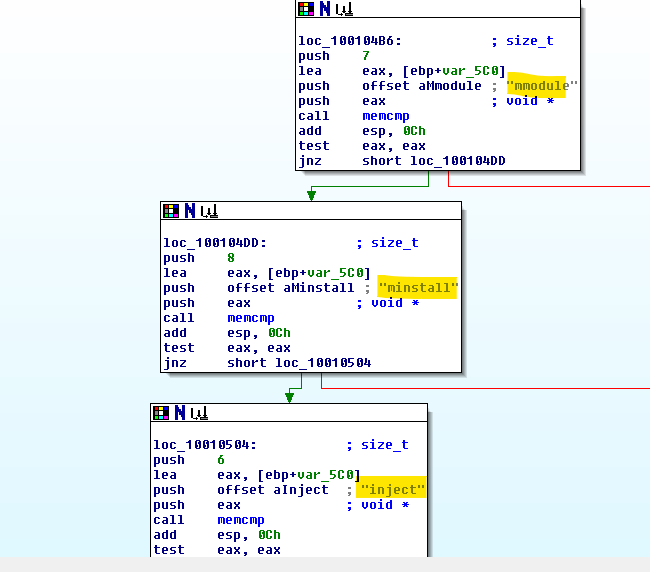
10.A few hundred lines into the subroutine at 0x1000FF58, a series of comparisons use memcmp to compare strings. What happens if the string comparison to robotwork is successful (when memcmp returns 0)?
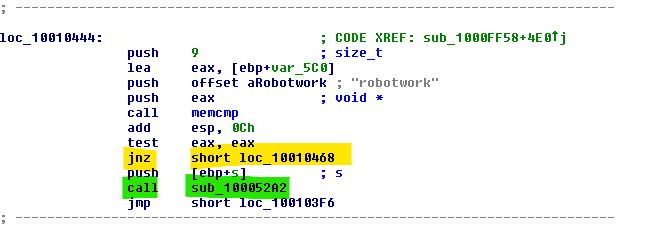


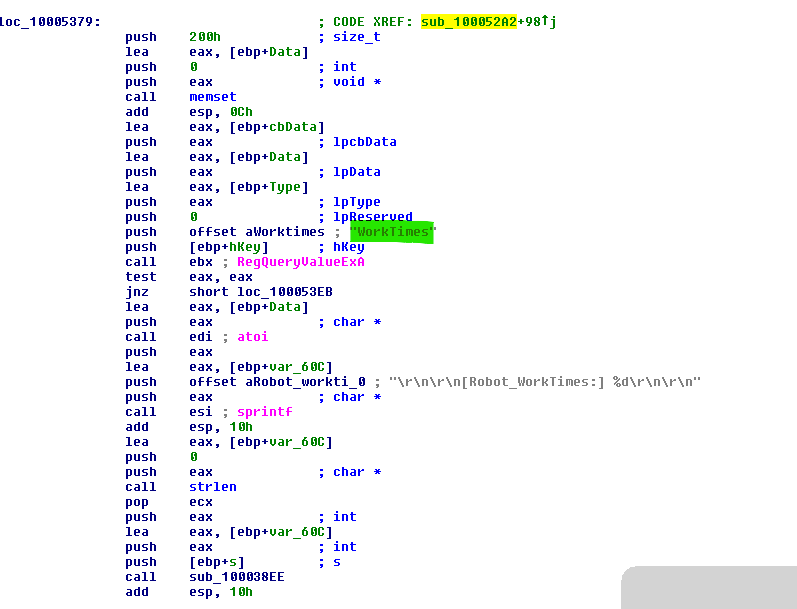
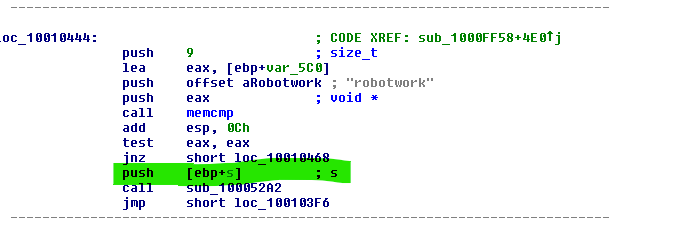
The registry values are queried and sent over the remote shell.
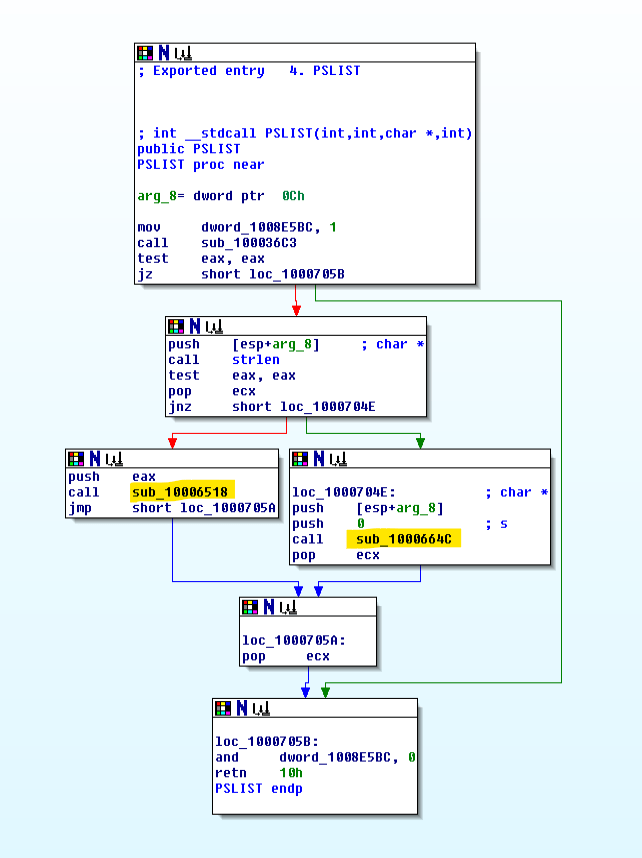
11.What does the export PSLIST do?