The start of a series of rooms covering Malware Analysis…
https://tryhackme.com/room/malmalintroductory
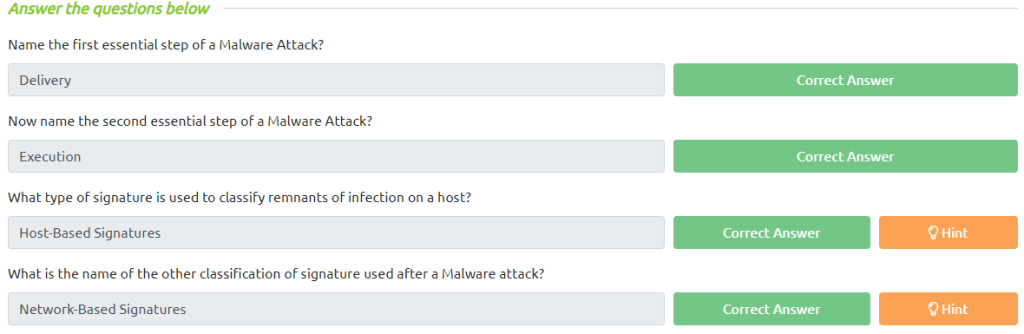
Task 2 Understanding Malware Campaigns

Task 3 Identifying if a Malware Attack has Happened
Task 7 Obtaining MD5 Checksums of Provided Files
The MD5 Checksum of aws.exe

The MD5 Checksum of Netlogo.exe
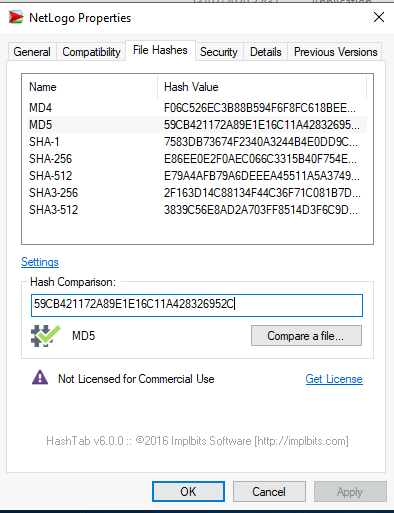
The MD5 Checksum of vlc.exe

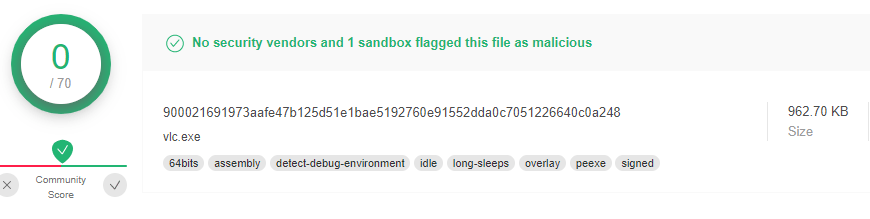
Task 8 Now lets see if the MD5 Checksums have been analysed before
Does Virustotal report this MD5 Checksum / file aws.exe as malicious? (Yay/Nay)
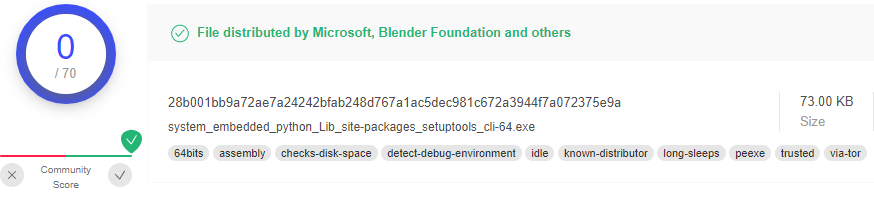
Does Virustotal report this MD5 Checksum / file Netlogo.exe as malicious? (Yay/Nay)

Does Virustotal report this MD5 Checksum / file vlc.exe as malicious? (Yay/Nay)
Task 9 Identifying if the Executables are obfuscated / packed
What does PeID propose 1DE9176AD682FF.dll being packed with?

What does PeID propose AD29AA1B.bin being packed with?

Task 10 What is Obfuscation / Packing?
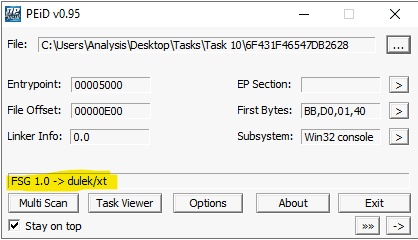
What packer does PeID report file “6F431F46547DB2628” to be packed with?
Task 12 Introduction to Strings
What is the URL that is outputted after using “strings”

How many unique “Imports” are there?

Task 13 Introduction to Imports
How many references are there to the library “msi” in the “Imports” tab of IDA Freeware for “install.exe”

Task 14 Practical Summary
What is the MD5 Checksum of the file?

Does Virustotal report this file as malicious? (Yay/Nay)
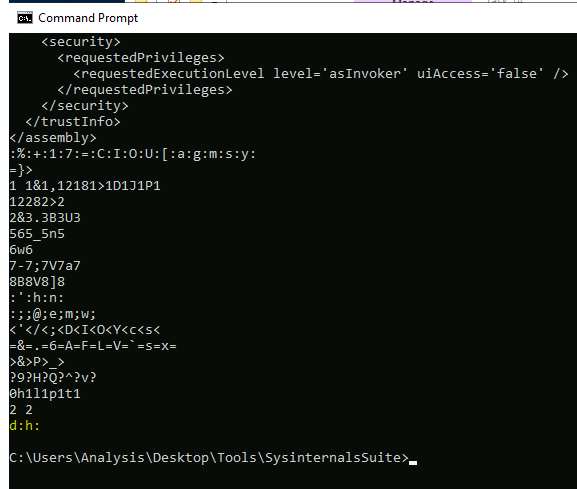
Output the strings using Sysinternals “strings” tool.
What is the last string outputted?
What is the output of PeID when trying to detect what packer is used by the file?
