Tools used:
- PEview
- Procmon
- Process explorer
- Malcode Analyst Pack
Questions
Analyze the malware found in the file Lab03-02.dll using basic dynamic analysis tools.
1.How can you get this malware to install itself?
Use PEview to examine the malware.
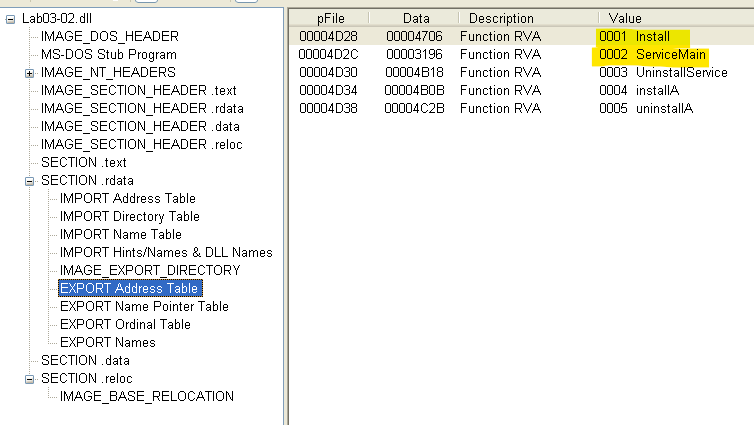
- In the exports there is ServiceMain which suggests a service for installation


- There are interesting import function highlighted above.
- HttpSendReuquest suggests the malware uses HTTP


The malware can be installed with the following command
rundll32.exe Lab03-02.dll,installA
2.How would you get this malware to run after installation?
Before running the malware take a Regshot to compare changes later.
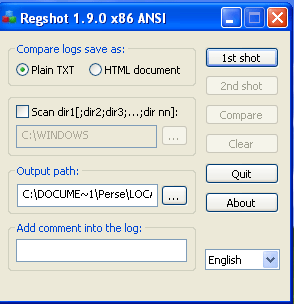

Take the 2nd regshot and compare the difference.


- Malware uses the IPRIP service
- The imagepath is set to svchost.exe
- Use the net start IPRIP to start the service.
3.How can you find the process under which this malware is running?
Use process explorer to find the dll and we can see that svchost.exe has the malware dll file.

The malware is trying to connect to server via the internet.
