https://www.vulnhub.com/entry/pwned-1,507/
Review
- Enumeration will lead to hidden directories
- Find a direcotrie list and re enumenrate the web server
- Examine the source code to find FTP credentials
- Access FTP to find a private key
- Once access is gained exploit the script with code injection and bind a shell
- Use docker exploit to gain root access
Enumeration
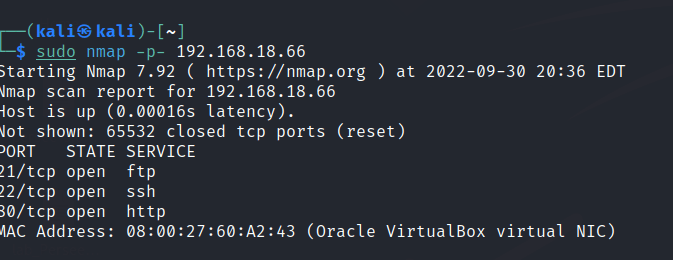
Run nmap scan to find for open ports.

Run a gobuster scan to find for hidden directories.

Port 80

A clue found on port 80 source code.

/robots.txt

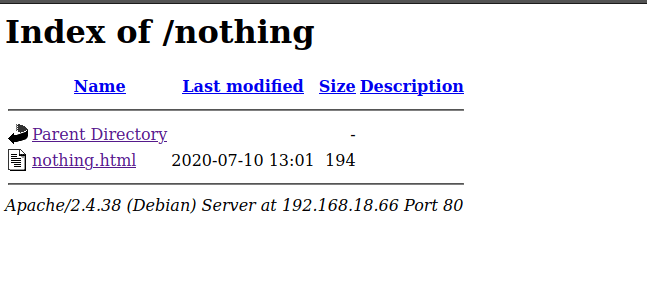
/nothing

/hidden_text
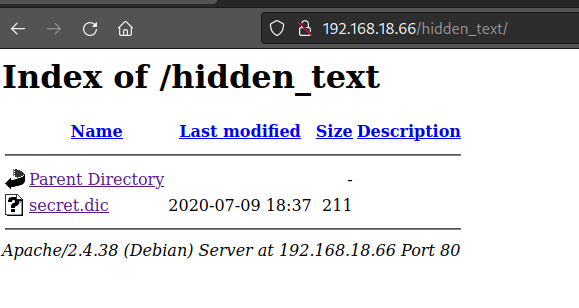
Found some kind of directory list.
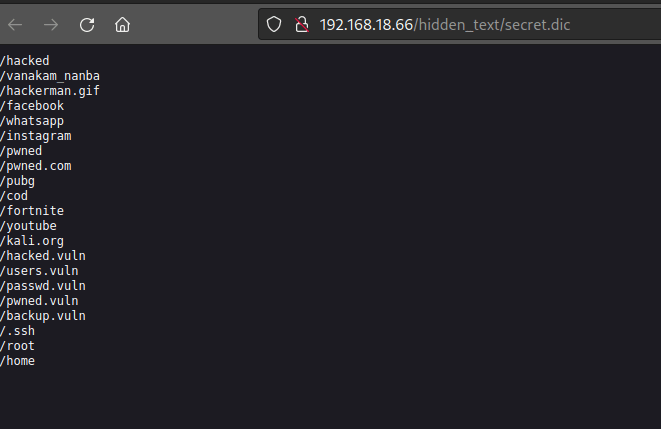
Use that list to enumerate the web server again.
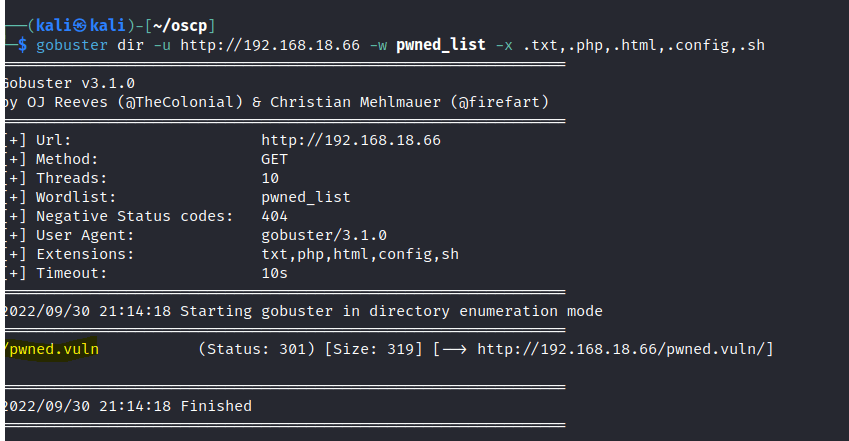
Found a page.
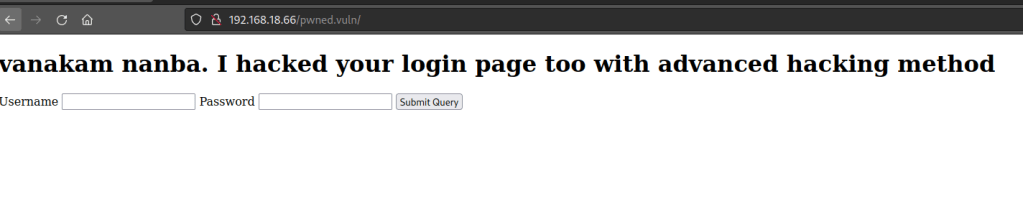
source code of /pwned.vuln


The files contains a note stating a potential user name and a private key.

Foothold
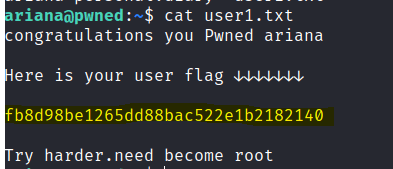
User access gained.

Found the first flag.
Found a note that has potential user names.

Check sudo permissions

Found the messenger script in the home directory.

We can run sudo -u selena /home/messenger.sh to interact directly with the selena user. Let’s use a bind shell to connect.


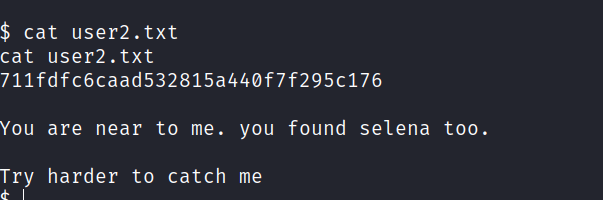
Selena access gained.


We find the second flag.
Privilege escalation
After some trial and error I resorted to linpeas. I missed out on the ID in the beginning. Selena user is able to use docker.

We search docker exploit on GTFObins.

Run the script and root user is gained.

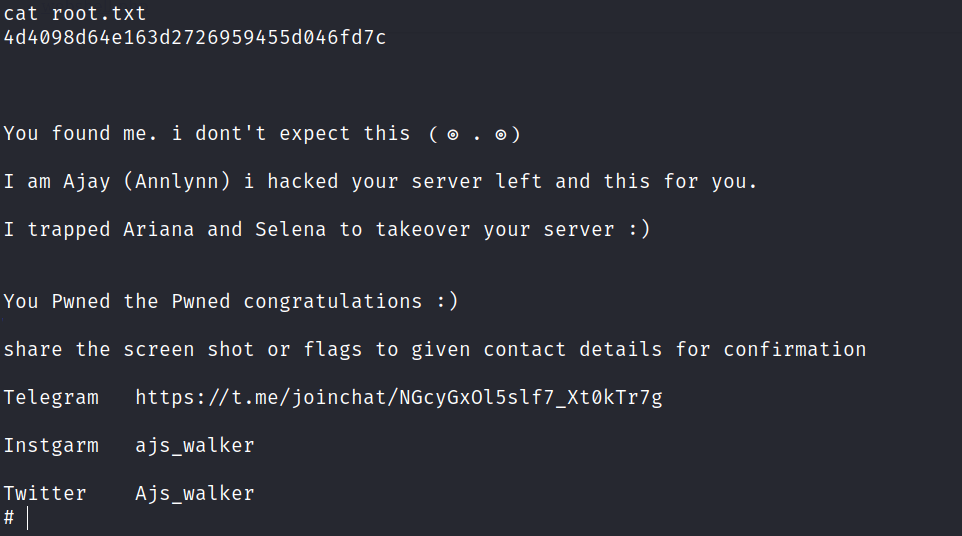
Found the final flag.