https://www.vulnhub.com/entry/evm-1,391/
Review
- Directory enumeration will lead to a wordpress site
- WPScan the site to gain creds
- Use metasploit to gian wp admin access
- Search for hidden files to find the password for the root user
Enumeration
Run nmap scan to find for open ports.


Run a gobuster scan to find for hidden directories.

Port 80

Unable to load the wordpress site.
Let’s use WPscan to enumerate.

Since I cant load the WordPress site I’ll use metasploit to see if I can gain access.
Set up the options.

Foothold
A shell is gained.

Head to the home folder and check the directory. Search for hidden files and there will be the root password.

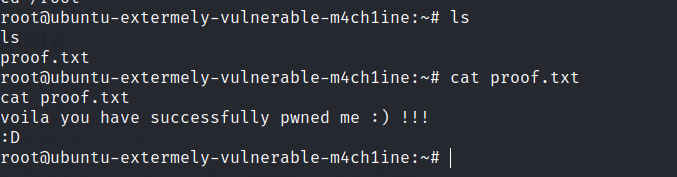
Privilege escalation
Found the final flag.