Tools used:
- Procmon
- Process explorer
Questions
Execute the malware found in the file Lab03-03.exe while monitoring it using basic dynamic analysis tools in a safe environment.
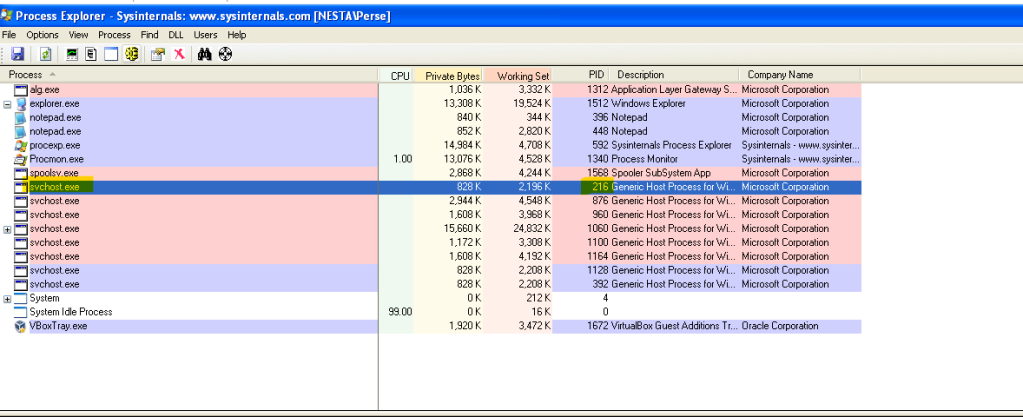
1. What do you notice when monitoring this malware with Process Explorer?
Run the malware and check Process Explorer. Once the malware is executed it creates a svchost.exe and deletes itself.
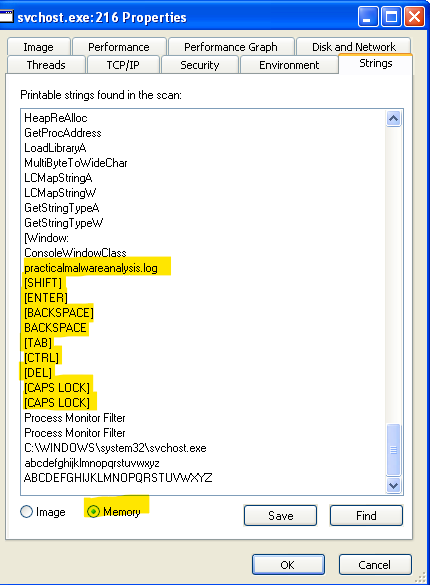
2.Can you identify any live memory modifications?
Check the properties of this particular svchost.exe and look at the strings function. Toggle to the Memory option and the strings show attributes of a keylogger. That records the commands in practicalmalwareanalysis log. Which is different from the Image option.

3.What are the malware’s host-based indicators?
Test the keylogger with writing something on the notepad.

Head to process monitor and filter out with the following options.
- Process Name is svchost.exe
- PID IS 216
- Operation is CreateFile
- Operation is WriteFile

From the filtered out results we can see the malware writes the keylogger actions to practicalmalwareanalysis.log.

4.The program performs process replacement on svchost.exe to launch a keylogger
And by inspecting the folder we can see the malware execute a svchost.exe program and logs it in a file call practicalmalwareanalysis.log
