https://app.letsdefend.io/training/lesson_detail/dynamic-malware-analysis-example-2
Connect to the Hands-On Practice lab in the page. LetsDefend has set up a system with the necessary tools for the malware analysis.
Since it is dynamic analysis we should set up the following tools before running the malware.
Start up Process Hacker which is a free, powerful, multi-purpose tool that helps you monitor system resources, debug software and detect malware

Then Process Monitor, which is an advanced monitoring tool for Windows that shows real-time file system, Registry and process/thread activity

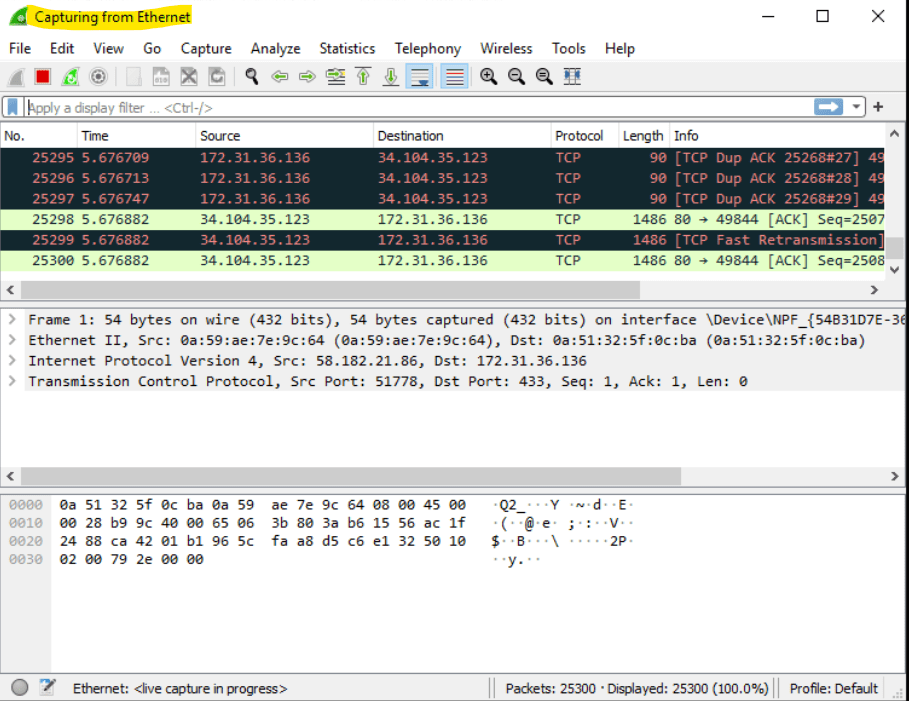
Net will be WireShark which is a widely-used network protocol analyzer.
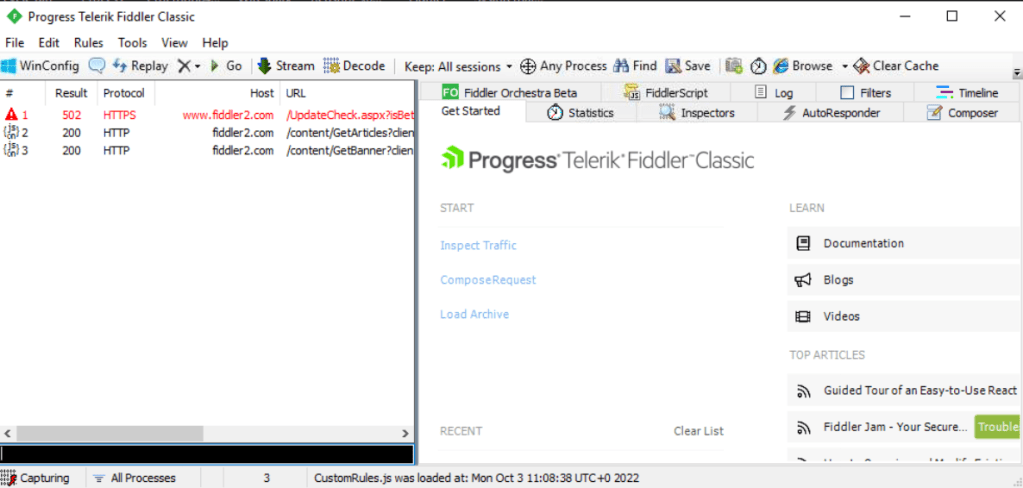
Lastly it will be Fiddler that helps you debug web applications by capturing network traffic between the Internet and test computers.
Unzip the malware and execute the file.

Head to process hacker and check if the malware is running. Take note of the process ID (PID).

Head to process monitor, use the process tree function to have a better view of the processes running. Search for the malware and add process and children to include filer.

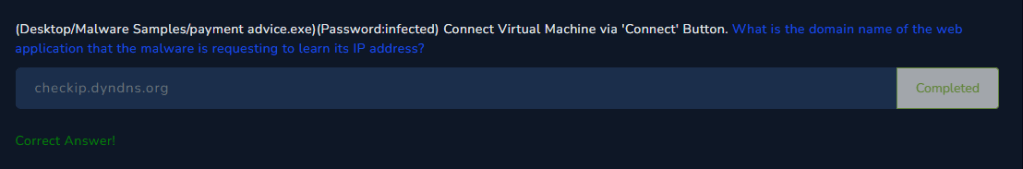
Question 1
What is the domain name of the web application that the malware is requesting to learn its IP address?
The domain name can be found in Fiddler.

Question 2 & 3
What is the domain name that the malware connects to for data hijacking?
What port does the malware communicate over?
We can use the Anyrun analysis provided by the tutorial.
https://app.any.run/tasks/1c8f0ad5-c14b-4cbe-aafd-17d03c1f4740/
Th domain name can be found in the connections tab.

Question 4 & 5
What is the username used by the malware to authenticate to the mail server it connects for data hijacking?
What is the password that the malware uses to authenticate to the mail server it connects for data hijacking?
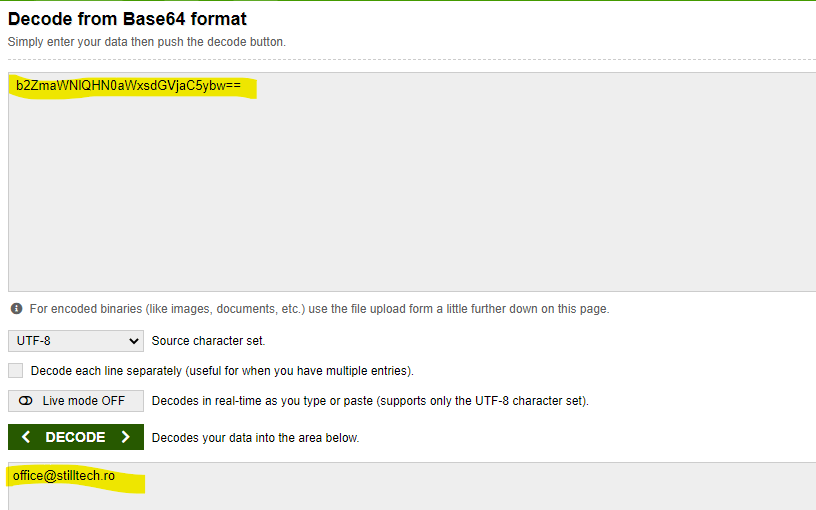
We can check the network stream and change the view to Text form. The log can be viewed in the stream. The credentials are all base64 encoded and we can just decode them using any online tool.