Category: Hacking
-
476f64’s easyAF
https://crackmes.one/crackme/5eae2d6633c5d47611746500 Determine the file type Use the file command to determine the file type. Test the program Strings Use strings to print the sequences of printable characters in files. Analyze Dissemble the program in GDB Test the program
-
linux_crackme by cyrex
https://crackmes.one/crackme/5ab77f5633c5d40ad448c2d6 Determine the file type Use the file command to determine the file type. Test the program Strings Use strings to print the sequences of printable characters in files. Analyze Dissemble the program in GDB The program will get an input and use strcmp to check and the jne instruction next. The password is stored…
-
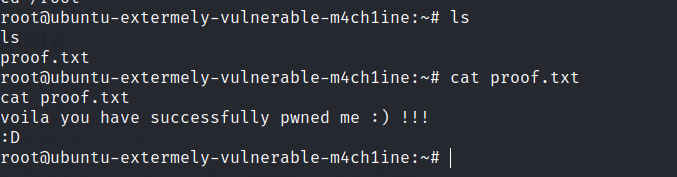
doubletrouble: 1
Download the machine: https://www.vulnhub.com/entry/doubletrouble-1,743/ Overview Enumeration Run nmap scan to find for open ports. Run a gobuster scan to find for hidden directories. Port 80 /secret Download the image and check if there are any hidden files inside the file. Let’s search searchsploit for some exploits. since we have some creds let’s use the RCE…
-
exzettabyte’s JustSee
https://crackmes.one/crackme/5b81014933c5d41f5c6ba944 Determine the file type Use the file command to determine the file type Test the program Strings Use strings to print the sequences of printable characters in files Analyze Dissemble the program with GDB Peda Set a breakpoint at the test instruction. Run the program and observe the registers. Test the program
-
Dripping Blues: 1
Download the machine: https://www.vulnhub.com/entry/dripping-blues-1,744/ Overview Enumeration Run nmap scan to find for open ports. Check the FTP server as anonymous. Crack the password on the zip file. Read the text. Run a gobuster scan to find for hidden directories. Port 80 /robots.txt In the robots text file there is a hidden directory that looks like…
-
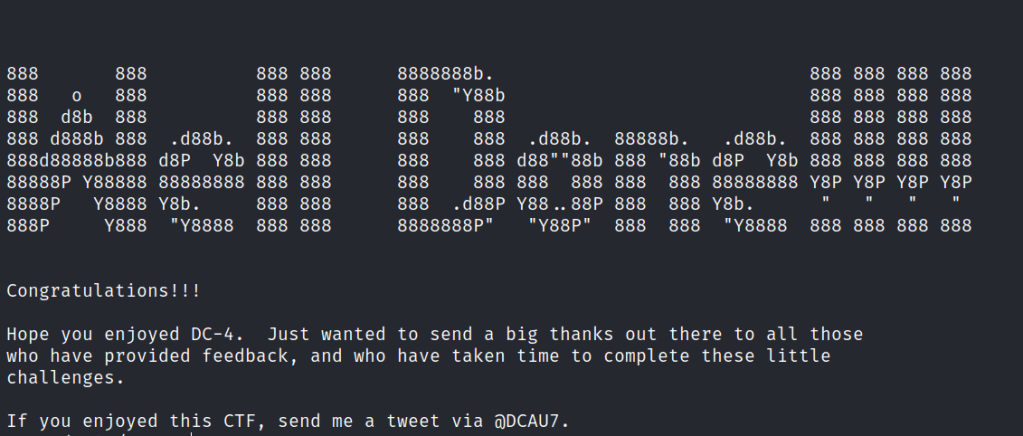
FristiLeaks: 1.3
A small VM made for a Dutch informal hacker meetup called Fristileaks. Meant to be broken in a few hours without requiring debuggers, reverse engineering, etc..
-
W34kn3ss: 1
The matrix is controlling this machine, neo is trying to escape from it and take back the control on it , your goal is to help neo to gain access as a “root” to this machine , through this machine you will need to perform a hard enumration on the target and understand what is…
-
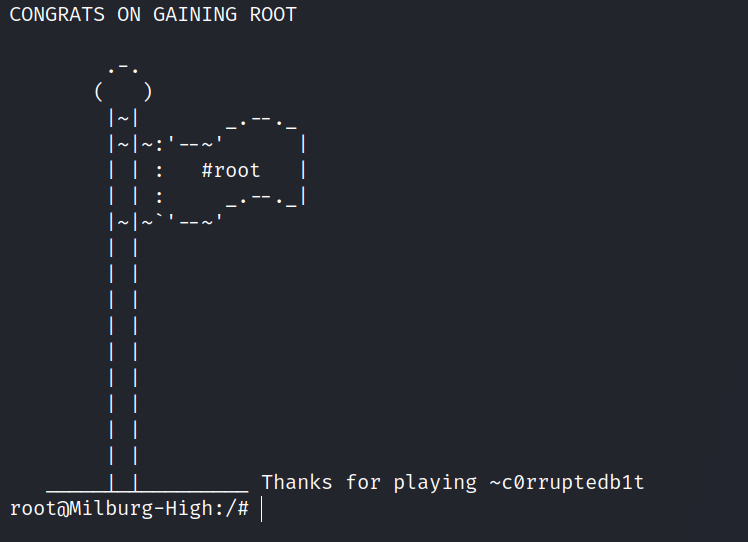
Bob: 1.0.1
The Milburg Highschool Server has just been attacked, the IT staff have taken down their windows server and are now setting up a linux server running Debian. Could there a few weak points in the new unfinished server?
-
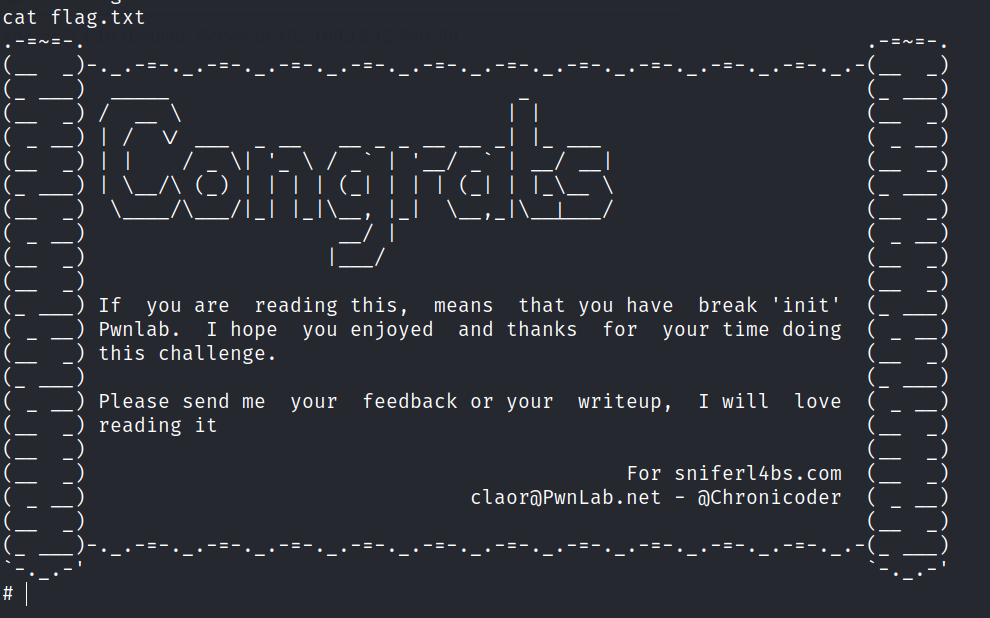
PwnLab: init
https://www.vulnhub.com/entry/pwnlab-init,158/ Review Enumeration Run nmap scan to find for open ports. Run a gobuster scan to find for hidden directories. Port 80 Found a login page. Tried using SQL injection and bruteforcing but to no availability. In the gobuster enumeration found a config.php file , however it doesn’t show any results. After some googling I…
-
HA: Wordy
Wordy is design for beginners to experience real life Penetration testing. This lab is completely dedicated to Web application testing and there are several vulnerabilities that should be exploited in multiple ways. Therefore, it is not only intended as a root challenge boot, the primary agenda is proactive in exploiting tops listed web application vulnerabilities.
-
Trying to learn Assembly for Reverse Engineering
I became interested in cybersecurity because I was curious about how malware creates damage. After some time of research and learning the fundamentals of computers and cybersecurity. I realize malware are like any other programs but with a malicious intent. (Yes, I took weeks to discover this) After getting my hands on Practical Malware Analysis by…
-
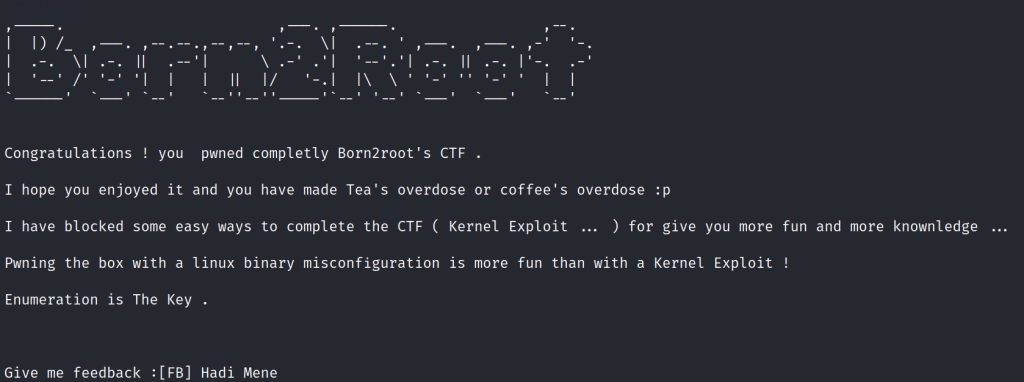
Born2Root: 1
https://www.vulnhub.com/entry/born2root-1,197/ Review Enumeration Run nmap scan to find for open ports. Run a gobuster scan to find for hidden directories. Port 80 /robots.txt /wordpress-blog / icons Found a RSA key. Use the private key to SSH into the 3 users found on the homepage. It is a key for martin. Foothold After some enumeration ,…
-
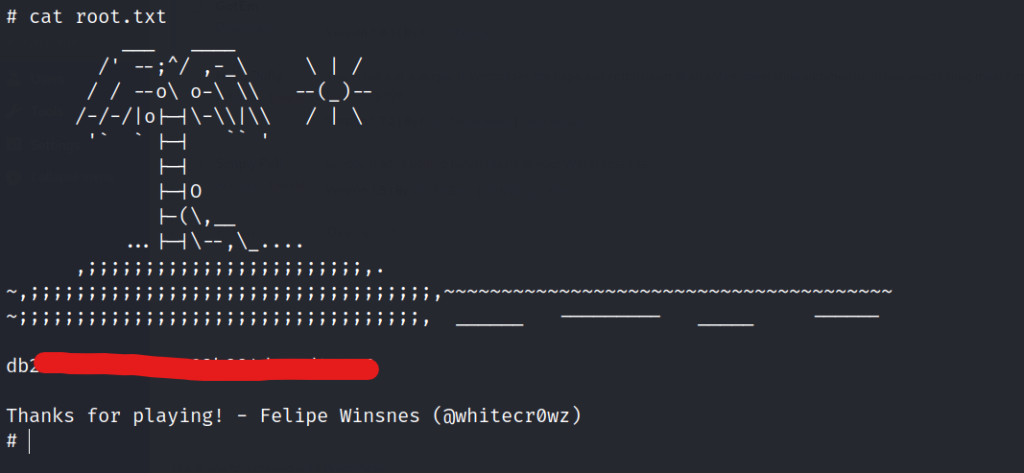
Sunset: Midnight
https://www.vulnhub.com/entry/sunset-midnight,517/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. /robots.txt Only found the admin user by using WPscan. Tried the bruteforce the WP admin user but it took too long. Decided to bruteforce the MYSQL server instead. Check out the MYSQL server.…
-
LetsDefend : Investigate Web Attack
https://app.letsdefend.io/challenge/investigate-web-attack/ In order to have any persistency this payload creates a user called hacker and password as Asd123!!
-
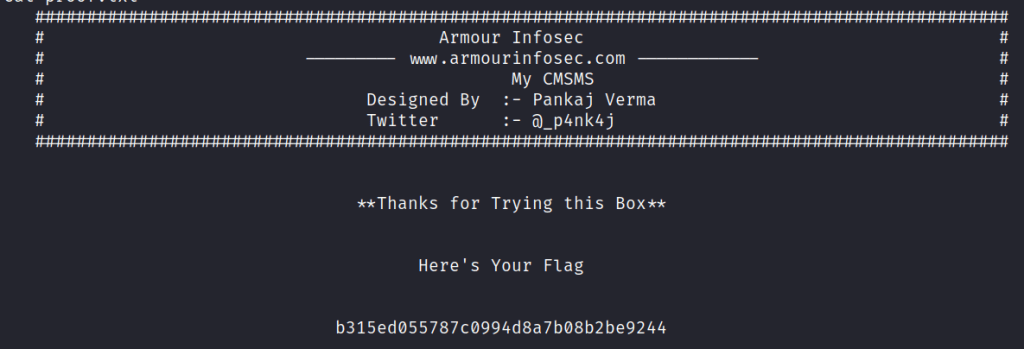
My CMSMS: 1
This VM has been designed by Pankaj Verma. Like its name, this box contains some interesting things about CMS. It has been designed in way to enhance user’s skills while playing with some privileges. Its a quite forward box but stay aware of rabbit holes.