Category: Persecure
-
Practical Malware Analysis : Lab 3-1
Tools used: Questions 1. What are this malware’s imports and strings? The malware seems to be obfuscated. Check the strings 2. What are the malware’s host-based indicators? Start up Process Explorer , ProcMon , ApateDNS and execute the malware. Observe the lower pane view in handles and a mutant is found Observe the dll and…
-
Practical Malware Analysis : Lab 5-1 (TBC)
Tools used: Questions 1. What is the address of DllMain? 1000D02E 2. Use the Imports window to browse to gethostbyname. Where is the import located? .idata:100163CC 3.How many functions call gethostbyname? 9 times with 5 different sub routines. 4. Focusing on the call to gethostbyname located at 0x10001757, can you figure out which DNS request…
-
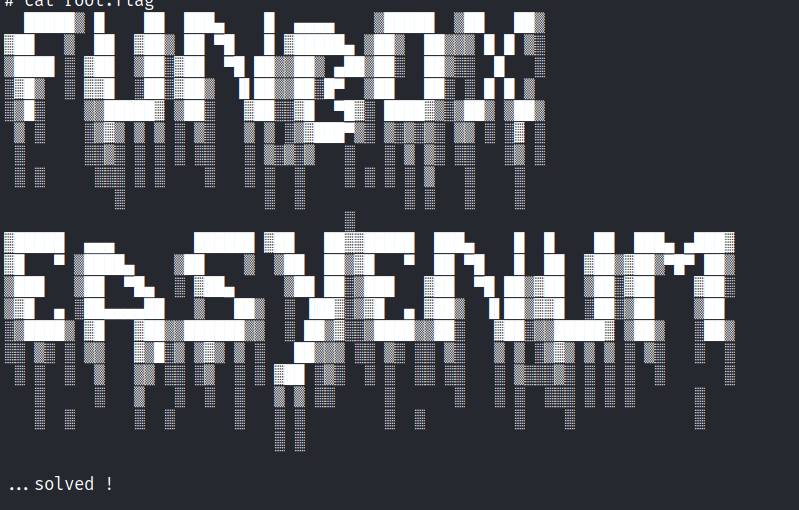
Funbox : EasyEnum
https://www.vulnhub.com/entry/funbox-easyenum,565/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. robots.txt secret/ mini.php/ In this mini shell we are able to upload files. Let’s upload a php reverse shell and execute it. Foothold Access gained. In the home directory there are the following…
-
Reverse Engineering : Mathematical Functions
Let’s create a simple program to see how the code is disassembled. Disassemble the program in IDA Pro.
-
Reverse Engineering : Variables Initiation
Let’s create a simple program to see how the code is dissasembled. Disassemble the program in IDA Pro. Spaces are allocated for each variable and the values are then moved to the allocated spaces.
-
Funbox : Rookie
https://www.vulnhub.com/entry/funbox-rookie,520/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. /logs/ gives us not found. FTP login Found some clues. Let’s use john to crack the zip files. The zip files contain the private keys. Foothold We are able to gain access via…
-

Funbox : Easy
https://www.vulnhub.com/entry/funbox-easy,526/ Review Enumeration gives us multiple pathways Use default credentials to gain access to an online bookstore Add a book that has a php reverse shell attached Once user access is gained , a password file is stored in the open SSH to the user and check for sudo permissions. Use GTFOBins to find for…
-
Vegeta: 1
https://www.vulnhub.com/entry/vegeta-1,501/ Review Enumeration uncovers hidden directories Check all the way to the bottom for clues Decode file and look out for double encoding Use a more through enumeration if stuck Decode a morse code to find for clues Check bash_histroy to find for clues Enumeration Run nmap scan to find for open ports. Run a…
-
Infosec Prep: OSCP
This machine was created for the InfoSec Prep Discord Server
-
HTB : Armageddon
https://app.hackthebox.com/machines/Armageddon Review Find service version through enumeration Metasploit exploit will give a web shell Databases credentials are stored openly Use mysqldump to dump password hashes Cracked hashes gives password for SSH login Able to run snap install without root Utilize dirty sock exploit to create an account and switch to root user without password Enumeration…
-
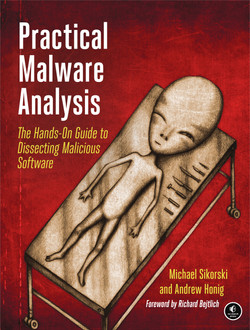
Practical Malware Analysis : Lab 1-3
Tools used: VirusTotal.com PEview PEiD Dependency Walker Malcode Analyst Pack Questions 1. Upload the Lab01-03.exe file to http://www.VirusTotal.com/. Does it match any existing antivirus definitions? 2. Are there any indications that this file is packed or obfuscated? If so, what are these indicators? If the file is packed, unpack it if possible. The file is…
-
HTB : Nibbles
https://app.hackthebox.com/machines/Nibbles Review Directory enumeration revels hidden information Login page credentials are simple RCE can be done from plugins Privilege execution can be achieved by editing a monitor script Enumeration Run nmap scan to find for open ports. Port 80 View source gives a clue. Run a gobuster scan to find for hidden directories. Main site…