Category: Persecure
-
Cybersploit : 1
https://www.vulnhub.com/entry/cybersploit-1,506/ Review Enumeration Run nmap scan to find for open ports. Port 80 Found a username in the sourcecode. Run a gobuster scan to find for hidden directories. /robots.txt Use base64 to decrypt the code and the first flag is found. Foothold Let’s try to ssh into the itsskv user with the flag password. Found…
-
DriftingBlues:6
https://www.vulnhub.com/entry/driftingblues-6,672/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. /robots.txt , /robots /textpattern/textpattern /spammer gives us a zip file Let’s crack the password for the zip protected file. Found the credentionals. Foothold Login via text pattern From textpattern interface we are able…
-

Practical Malware Analysis : Lab 3-2
Tools used: Questions Analyze the malware found in the file Lab03-02.dll using basic dynamic analysis tools. 1.How can you get this malware to install itself? Use PEview to examine the malware. The malware can be installed with the following command rundll32.exe Lab03-02.dll,installA 2.How would you get this malware to run after installation? Before running the…
-
DC: 1
https://www.vulnhub.com/entry/dc-1,292/ Review Enumeration Run nmap scan to find for open ports. port 80 Run a gobuster scan to find for hidden directories. robots.txt gives us a long list. After some time exploring the robots.txt folders , I am unable to find anymore clues. From the Nmap scan we know that Drupal is running version 7.…
-

Practical Malware Analysis : Lab 3-1
Tools used: Questions 1. What are this malware’s imports and strings? The malware seems to be obfuscated. Check the strings 2. What are the malware’s host-based indicators? Start up Process Explorer , ProcMon , ApateDNS and execute the malware. Observe the lower pane view in handles and a mutant is found Observe the dll and…
-

Practical Malware Analysis : Lab 5-1 (TBC)
Tools used: Questions 1. What is the address of DllMain? 1000D02E 2. Use the Imports window to browse to gethostbyname. Where is the import located? .idata:100163CC 3.How many functions call gethostbyname? 9 times with 5 different sub routines. 4. Focusing on the call to gethostbyname located at 0x10001757, can you figure out which DNS request…
-
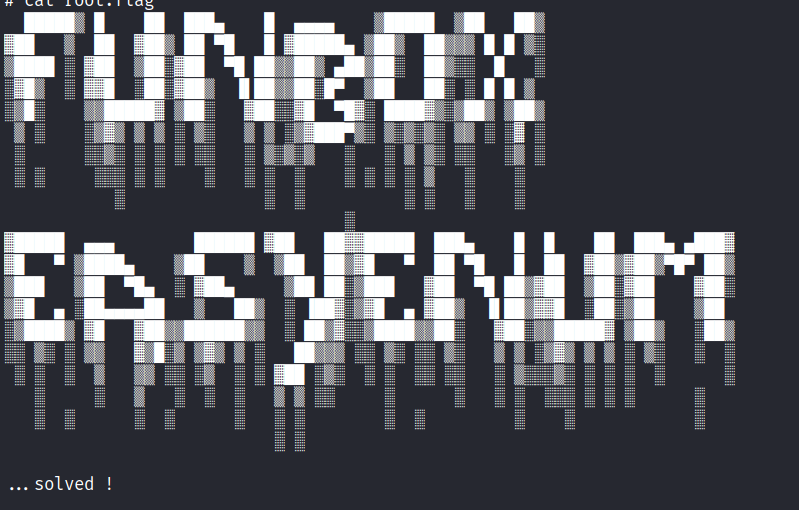
Funbox : EasyEnum
https://www.vulnhub.com/entry/funbox-easyenum,565/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. robots.txt secret/ mini.php/ In this mini shell we are able to upload files. Let’s upload a php reverse shell and execute it. Foothold Access gained. In the home directory there are the following…
-
Reverse Engineering : Mathematical Functions
Let’s create a simple program to see how the code is disassembled. Disassemble the program in IDA Pro.
-
Reverse Engineering : Variables Initiation
Let’s create a simple program to see how the code is dissasembled. Disassemble the program in IDA Pro. Spaces are allocated for each variable and the values are then moved to the allocated spaces.
-
Funbox : Rookie
https://www.vulnhub.com/entry/funbox-rookie,520/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. /logs/ gives us not found. FTP login Found some clues. Let’s use john to crack the zip files. The zip files contain the private keys. Foothold We are able to gain access via…
-

Funbox : Easy
https://www.vulnhub.com/entry/funbox-easy,526/ Review Enumeration gives us multiple pathways Use default credentials to gain access to an online bookstore Add a book that has a php reverse shell attached Once user access is gained , a password file is stored in the open SSH to the user and check for sudo permissions. Use GTFOBins to find for…