Category: Persecure
-
Sunset: Midnight
https://www.vulnhub.com/entry/sunset-midnight,517/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. /robots.txt Only found the admin user by using WPscan. Tried the bruteforce the WP admin user but it took too long. Decided to bruteforce the MYSQL server instead. Check out the MYSQL server.…
-
LetsDefend: Dynamic Malware Analysis Example #2
https://app.letsdefend.io/training/lesson_detail/dynamic-malware-analysis-example-2 Connect to the Hands-On Practice lab in the page. LetsDefend has set up a system with the necessary tools for the malware analysis. Since it is dynamic analysis we should set up the following tools before running the malware. Start up Process Hacker which is a free, powerful, multi-purpose tool that helps you monitor…
-
LetsDefend: Dynamic Malware Analysis Example #1
https://app.letsdefend.io/training/lesson_detail/dynamic-malware-analysis-example-1 Connect to the Hands-On Practice lab in the page. LetsDefend has set up a system with the necessary tools for the malware analysis. Since it is dynamic analysis we should set up the following tools before running the malware. Start up Process Hacker which is a free, powerful, multi-purpose tool that helps you monitor…
-
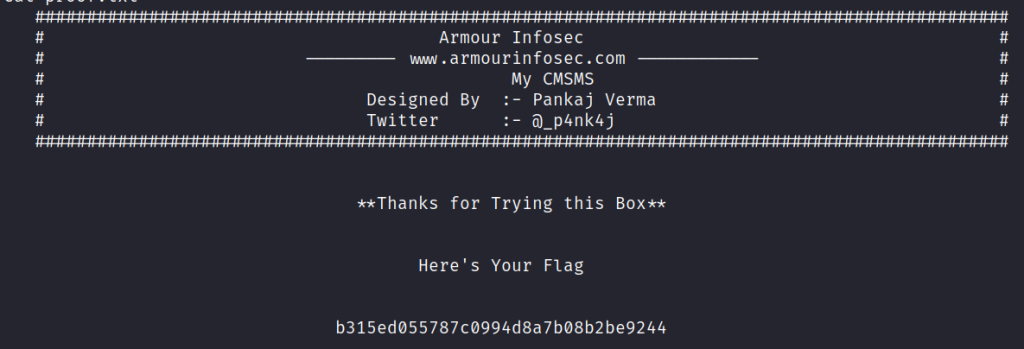
My CMSMS: 1
This VM has been designed by Pankaj Verma. Like its name, this box contains some interesting things about CMS. It has been designed in way to enhance user’s skills while playing with some privileges. Its a quite forward box but stay aware of rabbit holes.
-
LetsDefend Challenge: Port Scan Activity
https://app.letsdefend.io/challenge/port-scan-activity/ First download the Log file which contains a pcap file and open it in Wireshark. Question 1 What is the IP address scanning the environment? We can see that is 10.42.42.253 sending a TCP 3-way handshake to a couple of different IP addresses. This suggests that that particular IP address is initiating a scan.…
-
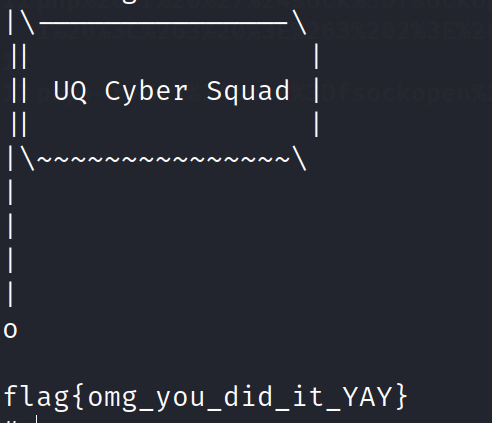
So Simple : 1
This is an easy level VM with some rabbitholes. Enumeration is key to find your way in. There are three flags (2 user and 1 root flag).
-
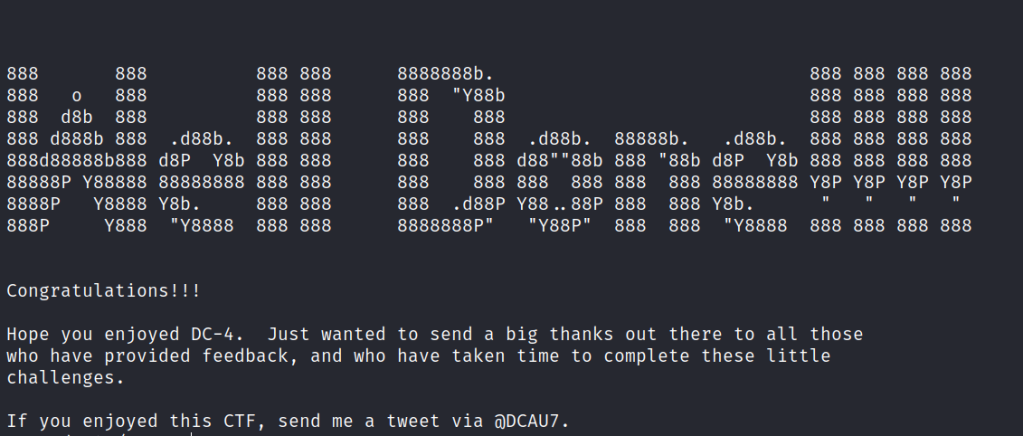
RickdiculouslyEasy :1
https://www.vulnhub.com/entry/rickdiculouslyeasy-1,207/ Review Enumeration Run nmap scan to find for open ports. FTP Server Able to access it annoymously. Found a flag. Port 9090 Unable to do much with he website as there is no login or password input. Port 13337 Port 60000 Netcat into the port to find a flag Port 80 Run a gobuster…
-
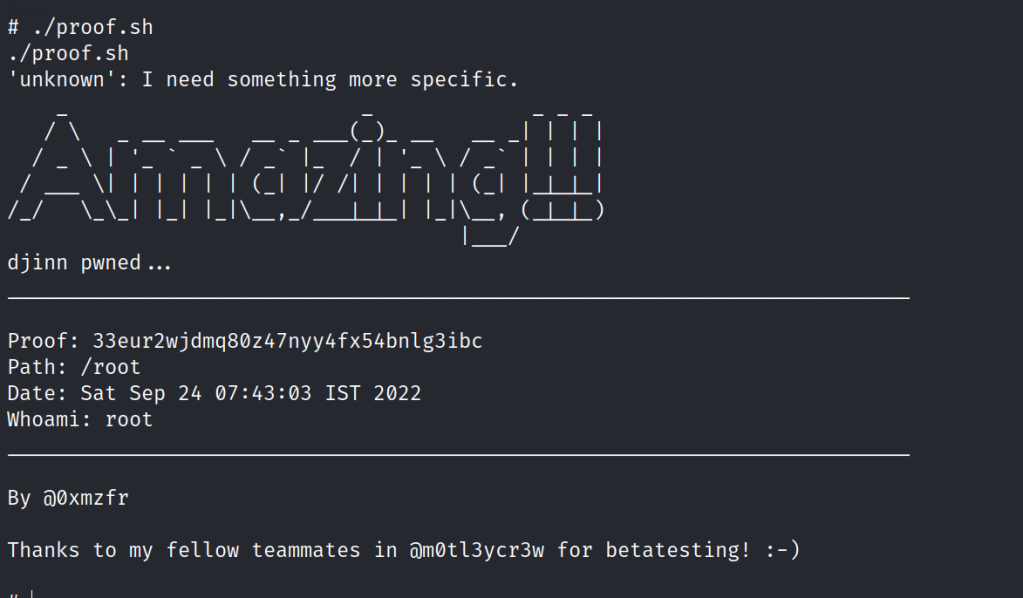
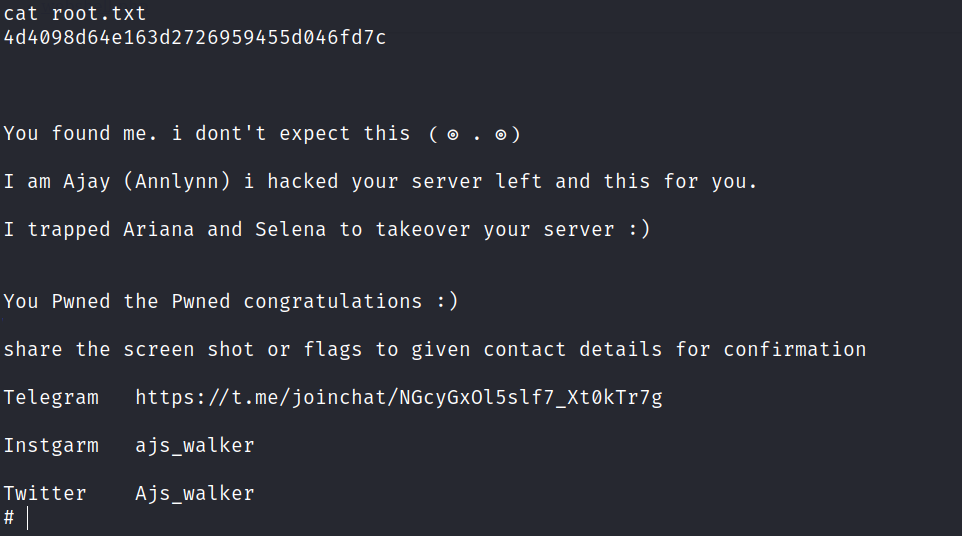
Djinn : 1
https://www.vulnhub.com/entry/djinn-1,397/ Review Enumeration Run nmap scan to find for open ports. FTP Enumeration Let’s try connecting to the game server. Let’s use netcat to connect. Port 7331 Http Run a gobuster scan to find for hidden directories. /genie is just an error page /wish We are able to input cmd and view the info in…
-
MalwareTech Challenges
The purpose of these challenges is to familiarize beginners with common malware techniques.
-
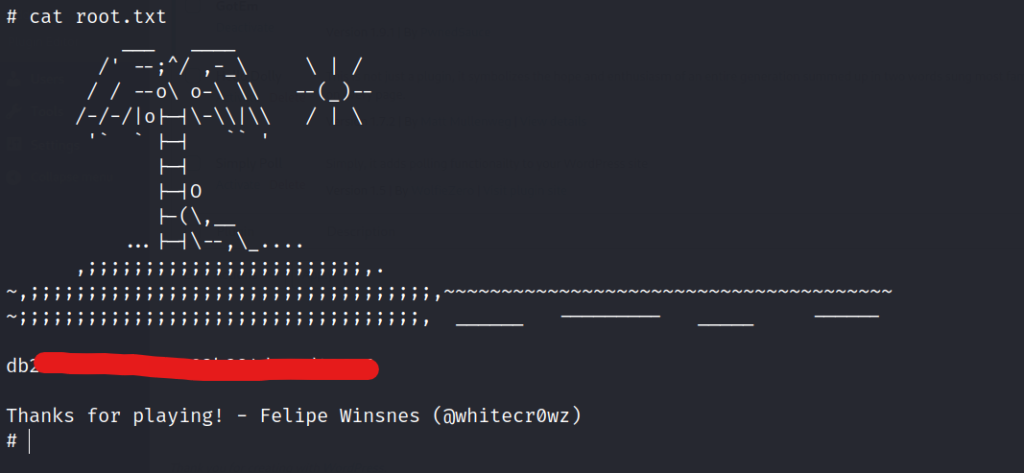
BBS (cute): 1.0.2
https://www.vulnhub.com/entry/bbs-cute-102,567/ Review Enumeration Run nmap scan to find for open ports. Port 80 Port 88 Run a gobuster scan to find for hidden directories. index.php We find CuteNews interface. Let’s register a new user , for the Captcha code we can use /captcha.php to find one. In the profile section of the interface we are…
-

Practical Malware Analysis : Lab 3-3
Tools used: Questions Execute the malware found in the file Lab03-03.exe while monitoring it using basic dynamic analysis tools in a safe environment. 1. What do you notice when monitoring this malware with Process Explorer? Run the malware and check Process Explorer. Once the malware is executed it creates a svchost.exe and deletes itself. 2.Can…
-
Photographer : 1
This machine was developed to prepare for OSCP. It is boot2root, tested on VirtualBox (but works on VMWare) and has two flags: user.txt and proof.txt.
-
DLL Hijacking
Tools needed: By taking advantage of the way some Windows applications look for and load Dynamic Link Libraries, a technique known as “DLL hijacking” allows malicious code to be injected into an application (DLL). This tutorial will showcase a simple DLL hijacking via the DVTA application. The application can be downloaded here. Download the application…