Category: Hacking
-
So Simple : 1
This is an easy level VM with some rabbitholes. Enumeration is key to find your way in. There are three flags (2 user and 1 root flag).
-
RickdiculouslyEasy :1
https://www.vulnhub.com/entry/rickdiculouslyeasy-1,207/ Review Enumeration Run nmap scan to find for open ports. FTP Server Able to access it annoymously. Found a flag. Port 9090 Unable to do much with he website as there is no login or password input. Port 13337 Port 60000 Netcat into the port to find a flag Port 80 Run a gobuster…
-
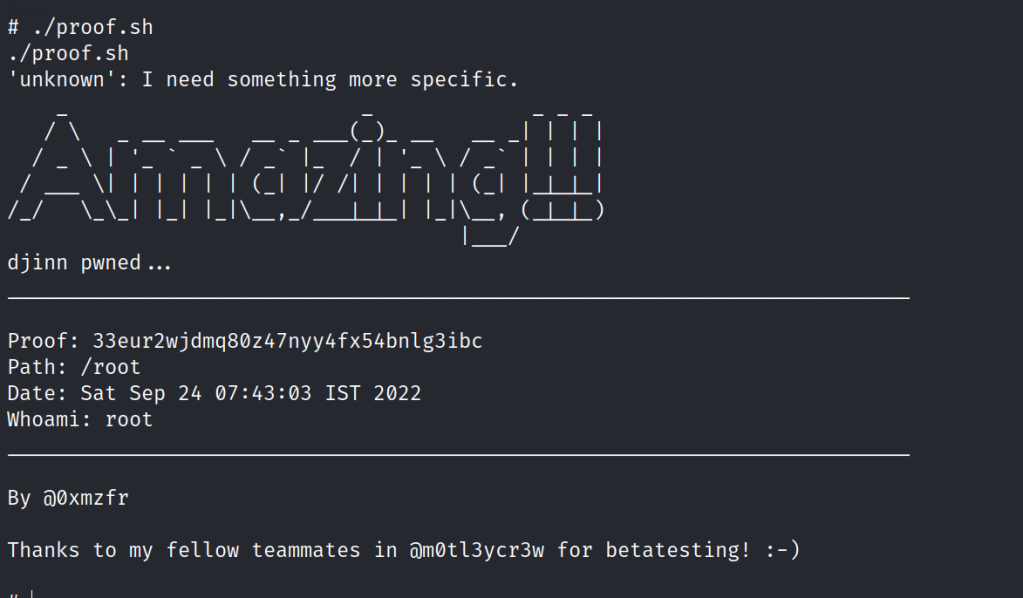
Djinn : 1
https://www.vulnhub.com/entry/djinn-1,397/ Review Enumeration Run nmap scan to find for open ports. FTP Enumeration Let’s try connecting to the game server. Let’s use netcat to connect. Port 7331 Http Run a gobuster scan to find for hidden directories. /genie is just an error page /wish We are able to input cmd and view the info in…
-
Windows Fundamentals 1
In part 1 of the Windows Fundamentals module, we’ll start our journey learning about the Windows desktop, the NTFS file system, UAC, the Control Panel, and more..
-
MalwareTech Challenges
The purpose of these challenges is to familiarize beginners with common malware techniques.
-
BBS (cute): 1.0.2
https://www.vulnhub.com/entry/bbs-cute-102,567/ Review Enumeration Run nmap scan to find for open ports. Port 80 Port 88 Run a gobuster scan to find for hidden directories. index.php We find CuteNews interface. Let’s register a new user , for the Captcha code we can use /captcha.php to find one. In the profile section of the interface we are…
-

Practical Malware Analysis : Lab 3-3
Tools used: Questions Execute the malware found in the file Lab03-03.exe while monitoring it using basic dynamic analysis tools in a safe environment. 1. What do you notice when monitoring this malware with Process Explorer? Run the malware and check Process Explorer. Once the malware is executed it creates a svchost.exe and deletes itself. 2.Can…
-
Photographer : 1
This machine was developed to prepare for OSCP. It is boot2root, tested on VirtualBox (but works on VMWare) and has two flags: user.txt and proof.txt.
-
Cybersploit : 1
https://www.vulnhub.com/entry/cybersploit-1,506/ Review Enumeration Run nmap scan to find for open ports. Port 80 Found a username in the sourcecode. Run a gobuster scan to find for hidden directories. /robots.txt Use base64 to decrypt the code and the first flag is found. Foothold Let’s try to ssh into the itsskv user with the flag password. Found…
-
DriftingBlues:6
https://www.vulnhub.com/entry/driftingblues-6,672/ Review Enumeration Run nmap scan to find for open ports. Port 80 Run a gobuster scan to find for hidden directories. /robots.txt , /robots /textpattern/textpattern /spammer gives us a zip file Let’s crack the password for the zip protected file. Found the credentionals. Foothold Login via text pattern From textpattern interface we are able…
-

Practical Malware Analysis : Lab 3-2
Tools used: Questions Analyze the malware found in the file Lab03-02.dll using basic dynamic analysis tools. 1.How can you get this malware to install itself? Use PEview to examine the malware. The malware can be installed with the following command rundll32.exe Lab03-02.dll,installA 2.How would you get this malware to run after installation? Before running the…
-
DC: 1
https://www.vulnhub.com/entry/dc-1,292/ Review Enumeration Run nmap scan to find for open ports. port 80 Run a gobuster scan to find for hidden directories. robots.txt gives us a long list. After some time exploring the robots.txt folders , I am unable to find anymore clues. From the Nmap scan we know that Drupal is running version 7.…
-

Practical Malware Analysis : Lab 3-1
Tools used: Questions 1. What are this malware’s imports and strings? The malware seems to be obfuscated. Check the strings 2. What are the malware’s host-based indicators? Start up Process Explorer , ProcMon , ApateDNS and execute the malware. Observe the lower pane view in handles and a mutant is found Observe the dll and…
-

Practical Malware Analysis : Lab 5-1 (TBC)
Tools used: Questions 1. What is the address of DllMain? 1000D02E 2. Use the Imports window to browse to gethostbyname. Where is the import located? .idata:100163CC 3.How many functions call gethostbyname? 9 times with 5 different sub routines. 4. Focusing on the call to gethostbyname located at 0x10001757, can you figure out which DNS request…